Many organizations need shared workstations, kiosks providing general information to most or all its employees. The challenge is getting a network-connected computer to access resources without giving every employee a network login. Auto-logon can help.
The Challenge
Delivering information to employees using computers for day-to-day tasks is easy. Send an email, use a portal note, etc. But what about employees who don’t use computers at the office? How do you reach them?
Many organizations use kiosks. Kiosks are shared computers, placed in common areas, on which employees can access information related to benefits, participate in company-provided training, and browse other information provided for their benefit on the the company intranet. This raises the challenge of getting the user logged in.
Forcing each user to enter a network ID every time he or she wants to access information via the kiosk is not workable. It takes too long and users often walk away without logging out. This causes other issues, not the least of which is loss of user accountability. A better way is configuring the kiosk to auto-logon and then manage security by application. The workstation is always logged in to the network. Users simply walk up and access publicly accessible information without entering any credentials. Those that need access to more sensitive information can be required to log in to the application Logon controlled application sessions should time out after a short period of non-use.
Configuring a kiosk for auto-login can be accomplished in a number of ways; some more secure or easier than others.
Configuring Auto-logon
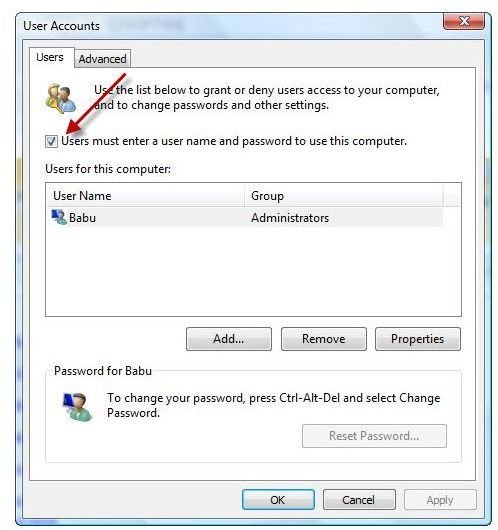
The easiest way to configure auto-logon in Windows XP and Windows VIsta is using the Microsoft-provided account management utilities. These work only if the kiosk is not added to an Active Directory (AD) domain. In XP, typing control userpasswords2 in the Run window brings up the required configuration attribute (See Auto Logon for Windows XP ). In Vista, enter netplwiz. Figure 1 is the result in Vista. In both versions of Windows, unchecking the box indicated by the red arrow, Users must enter a user name and password to use this computer, causes Windows to prompt for a logon user name and password. These credentials are used on restart or power up to logon, eliminating the credentials prompt from the user’s logon steps. Again, this only works–and the check box only appears–if the kiosk is NOT a member of an AD domain.
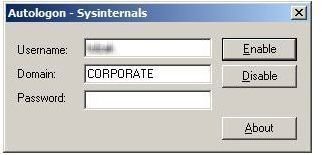
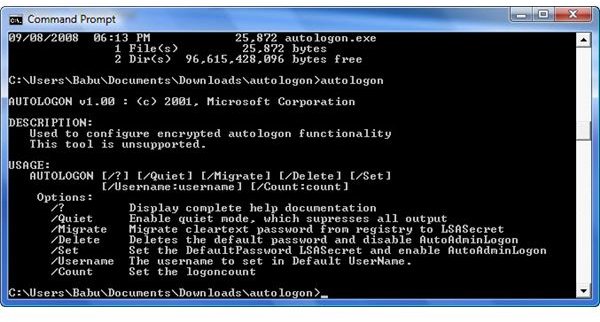
If you require the kiosk to have domain membership, there are two other utilities available. The first is the Sysinternals’ Autologon utility, a free download from Microsoft. It provides both a GUI (See Figure 2) and a command line interface for Windows XP. Its real value is its ability to configure auto-logon even when a kiosk is attached to a domain. It bypasses the Windows utility. A different utility, also named autologon , is available for free download to allow bypassing the domain membership constraint in Vista (See Figure 3). Using these utilities is easy, but’s there’s a catch.
These utilities write the auto-logon credentials to either the registry or to LSASecret. In either case, they are easily retrievable by anyone with access to the kiosk. Under no circumstances should the logon account have more than the most limited network resource access. Provide additional access via application credentials, if necessary. If elevated privileges are necessary for the auto-logon account, consider using a commercial product like LogonExpert .
Tables and Figures (hover for caption, click to enlarge)
This post is part of the series: Use SysInternals security utilities to manage network and system security
SysInternals provides free security utilities for managing Microsoft Windows networks and systems. Available for download from Microsoft, they provide a powerful set of applications for oversight and protection of network assets.
- Validate System Access with AccessChk
- Streamline Kiosk Operation with Auto-logon
- Enumerate Windows File and Folder Access with AccessEnum
- LogonSessions and PsLoggedOn to Oversee and Manage System Access
- Use Autoruns to Improve Performance and Identify Malware
- Manage, Monitor, and Kill Windows Processes with Process Explorer
- PSExec: Free Security Testing and System Management Tool
- PsLogList: Free Utility to Parse and Review Windows Logs
- Map System Configs with PsInfo
- Use SigCheck to Validate System Files