Sometimes a script or other application providing automatic management oversight over end-user devices or servers needs session and logon data. Two free utilities provide the functionality necessary to achieve these outcomes in a Microsoft Windows environment.
Overview
Occasionally, security and network administrators need information about who is logged into a system–both locally and remotely. Sometimes this information feeds a script or other application providing automatic management oversight over end-user devices or servers. Two free utilities provide the functionality necessary to achieve these outcomes in a Microsoft Windows environment–LogonSessions and PsLoggedOn . Both are SysInternals utilities available from Microsoft. PSloggedOn is part of the PSTools suite, provided free by Microsoft, to help administrators secure and protect Microsoft Windows environments.
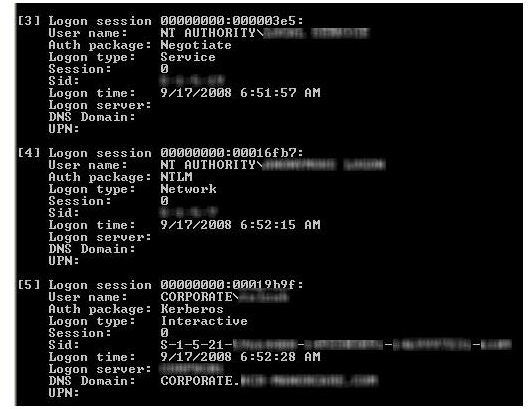
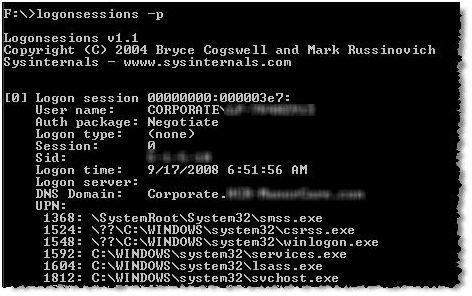
LogonSessions
LogonSessions provides information about the machine on which it runs. Run from the command line, the default output–when no command line parameters are supplied–is shown in Figure 1. The SID, logon date and time, domain controller authenticating a domain user, and a user’s AD domain are all listed. But what if you want to see the processes running in each logon session? Just add the “-p” command line parameter, as depicted in Figure 2.
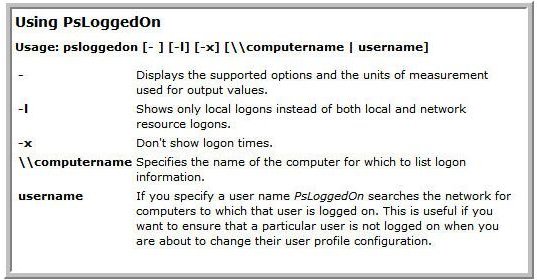
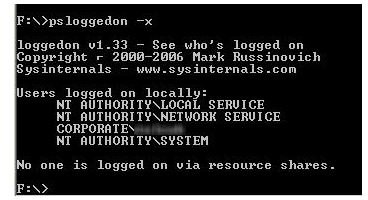
PsLoggedOn
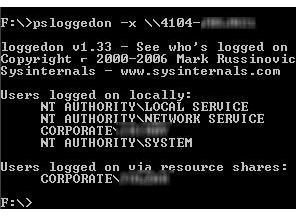
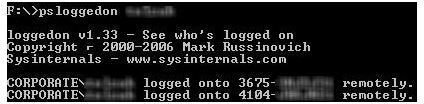
PsLoggedOn doesn’t provide session process information. However, it has another unique property. An administrator can list all remotely or locally connected users on any machine on the network, by running the command line utility only from the administrator’s computer. He or she can also list all devices to which a specific user is authenticated. Five command line parameters enable these features, as shown in Figure 3. Figure 4 shows the results of requesting logons to another machine on the network. Figure 5 shows PsLoggedOn output when logons on a specific system are requested. In Figure 6, systems are listed–after a network segment search–to which a specific user is logged on.
The final word
The output of both utilities can be redirected to a text file, allowing administrators to easily provide input to management scripts and other applications. Together, they are a powerful utility set providing simple, under-the-hood assessments of who is logged on, what systems they are accessing, and the processes involved.
Tables and Figures (Hover for caption, click to enlarge)
This post is part of the series: Use SysInternals security utilities to manage network and system security
SysInternals provides free security utilities for managing Microsoft Windows networks and systems. Available for download from Microsoft, they provide a powerful set of applications for oversight and protection of network assets.
- Validate System Access with AccessChk
- Streamline Kiosk Operation with Auto-logon
- Enumerate Windows File and Folder Access with AccessEnum
- LogonSessions and PsLoggedOn to Oversee and Manage System Access
- Use Autoruns to Improve Performance and Identify Malware
- Manage, Monitor, and Kill Windows Processes with Process Explorer
- PSExec: Free Security Testing and System Management Tool
- PsLogList: Free Utility to Parse and Review Windows Logs
- Map System Configs with PsInfo
- Use SigCheck to Validate System Files