AccessChk is a free utility, which allows you to quickly assess access to folders, files, processes, or services on Windows workstations or servers.
The Challenge
System administrators and security professionals usually know what to do to ensure trustworthy processing environments. After all, there are plenty of blogs, articles, books, etc. on the subject. Many administrators diligently design and implement access controls, assuming their well-planned configurations actually provide expected levels of security. However, we can’t think of everything during the design phase of controls implementation. No system lock-down controls should be implemented without checking the result, ensuring the access constraints we intended are actually in place.
Workstation- or server-level validation can be tricky. Not only should you check folder and file access. Access to processes, services, and OS components must also be verified. AccessChk enables checking of all these components.
AccessChk
AccessChk , is a free downloadable Windows (XP, VIsta, 2000 and Server 2003 supported) command line utility. Part of Microsoft’s Sysinternals Suite, it’s one of several troubleshooting solutions, which target specific security challenges.
Using AccessChk is simple, and Microsoft provides use case examples as part of it’s online documentation. However, its ability to communicate issues if something doesn’t work right is very limited. So it’s important to adhere strictly to the command line syntax.
The command’s syntax is very simple,
accesschk [modifiers] [user/group] [process/service/file/folder]
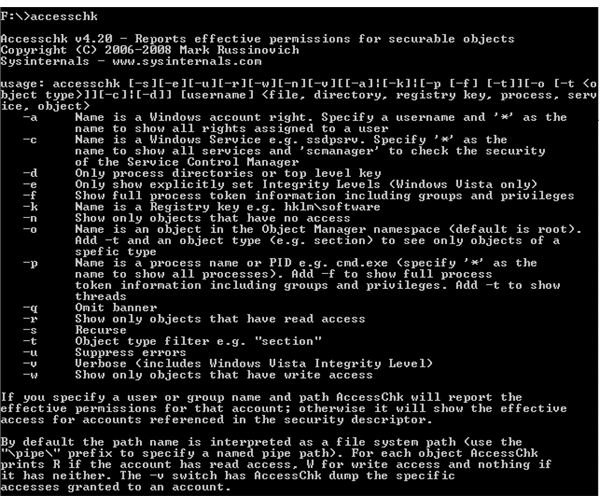
Entering accesschk with no parameters results in a help listing as shown in Figure 1. As long as you follow the syntax provided, you can quickly check access levels for inviduals users or groups. The following are some examples.
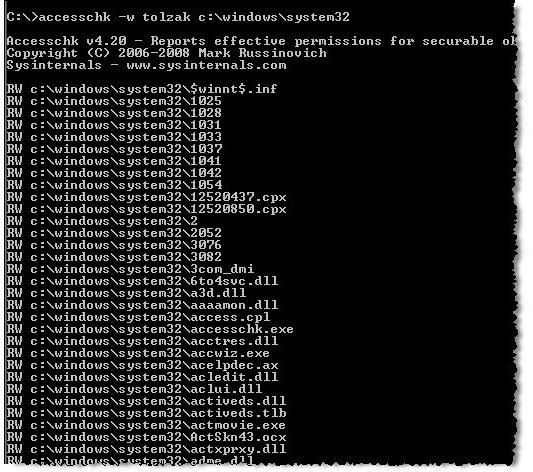
- Check for write access, for a specific user, to Windows system files (Figure 2): accesschk -w tolzak c:\windows\system32
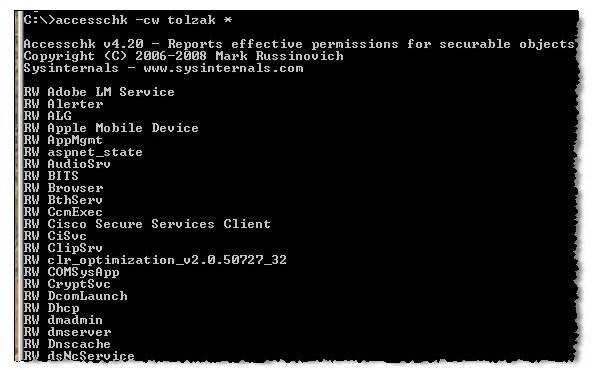
- Check for write access, for a specific user, to all Windows services (Figure 3): accesschk -cw tolzak *
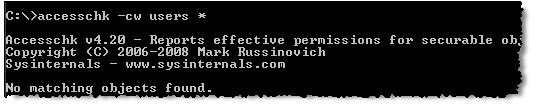
- Check for write access, for members of the USERS group, to all Windows services (Figure 4): accesschk -cw users *
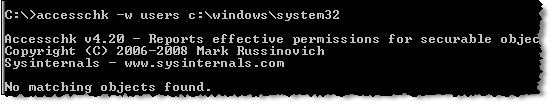
- Check for write access, for members of the USERS group, to Windows system files (Figure 5): accesschk -w users c:\windows\system32
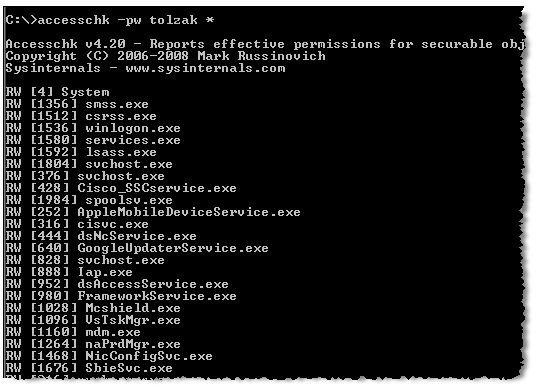
- Check for write access, for a specific user, to all running processes (Figure 6): accesschk -pw tolzak *
Tips
Many Windows administrators aren’t used to using command line utilities. So here are some tips.
- Create a specific folder for your command line utilities. Don’t place them in OS folders (e.g. system32 or windows).
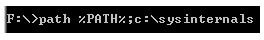
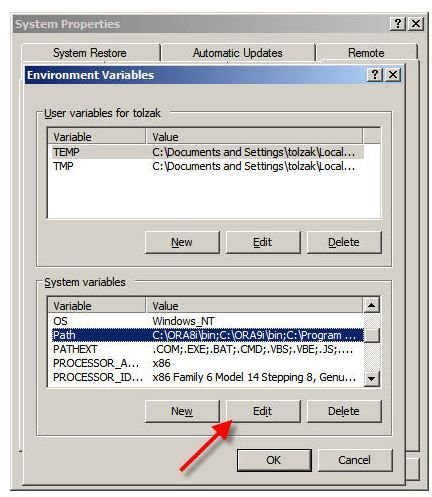
- Make sure your PATH environment variable contains the path to the command line utility folder. Windows searches the paths in the PATH variable when an executable is invoked at the command line. PATH is changed from the command line or via My Computer properties. Figure 7 shows the command line syntax for adding an additional path (c:\sysinternals) to the the existing PATH contents. But be careful with this. If you type it wrong, you’ll make unintended changes. For those who prefer the safer GUI approach, right click on My Computer then on Properties. At the bottom of the Advanced tab display, click Environment Variables. As shown in Figure 8, click on the path variable then the Edit button. (Example uses Windows XP)
- If you want to place the output of the command in a text file for input to a script or for later reference, use the command line redirect function. For example, accesschk -pw tolzak * > whoop places the output of accesschk into a text file named whoop.
Tables and Figures (hover for caption, click to enlarge)
This post is part of the series: Use SysInternals security utilities to manage network and system security
SysInternals provides free security utilities for managing Microsoft Windows networks and systems. Available for download from Microsoft, they provide a powerful set of applications for oversight and protection of network assets.
- Validate System Access with AccessChk
- Streamline Kiosk Operation with Auto-logon
- Enumerate Windows File and Folder Access with AccessEnum
- LogonSessions and PsLoggedOn to Oversee and Manage System Access
- Use Autoruns to Improve Performance and Identify Malware
- Manage, Monitor, and Kill Windows Processes with Process Explorer
- PSExec: Free Security Testing and System Management Tool
- PsLogList: Free Utility to Parse and Review Windows Logs
- Map System Configs with PsInfo
- Use SigCheck to Validate System Files