Rootkits, Trojan Horses, worms, viruses, spyware, adware, fake AV and other type of malware require different computer virus removal tools. You need to know your enemy before using any self-help guide or removal tools, so check out this guide to learn about them all.
Free Virus Removal
There’s no need to pay or subscribe to a service for computer virus removal. If you have the right tools and are familiar with how it works, you’ll get back your system in no time. There’s plenty of self-help guides but you have to be careful to not fall into websites of rogueware affiliates, offering free downloads of trial versions of anti-malware or anti-virus programs. Not that there is something wrong in using trial versions but if what you install only offers a free to scan without free malware removal, you just wasted your time and potentially infected your system with rogueware .
Removing Fake, Misleading or Rogue Programs
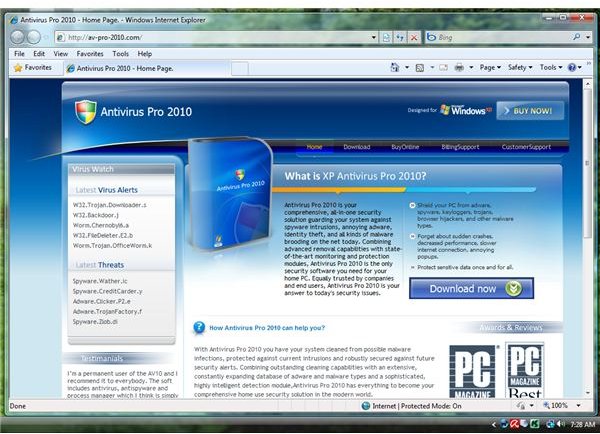
Rogue and fake AV distributors will use blackhat SEO techniques to get their malicious page on top of search engine results. Any
Internet user who views the page is a potential victim of a Trojan downloader that will install fake AV. Some of the bad guys will rip up the user’s existing interface and database of trustworthy and popular antivirus or antispyware programs or it will detect non-existing threats.
To remove rogue programs, follow the steps below:
- Use Rkill to automatically shutdown the malicious process by the fake AV. If it will not work or run, use Process Explorer to manually kill the malware process. If you are using Windows XP, you can use the Task Manager included in xp_emergencyutil.zip by Windows Expert, Doug Knox.
- You must not reboot the computer after shutting down the malware process. Immediately, install removal tools such as Ad-Aware , EmsiSoft (formerly known as A-squared Free), Malwarebytes , Spybot - S&D or SUPERAntiSpyware .
- Update the removal tool and run a quick scan.
The fake or rogue programs should be taken care of by using any of the above tools.
Removing Trojans, Viruses or Worms

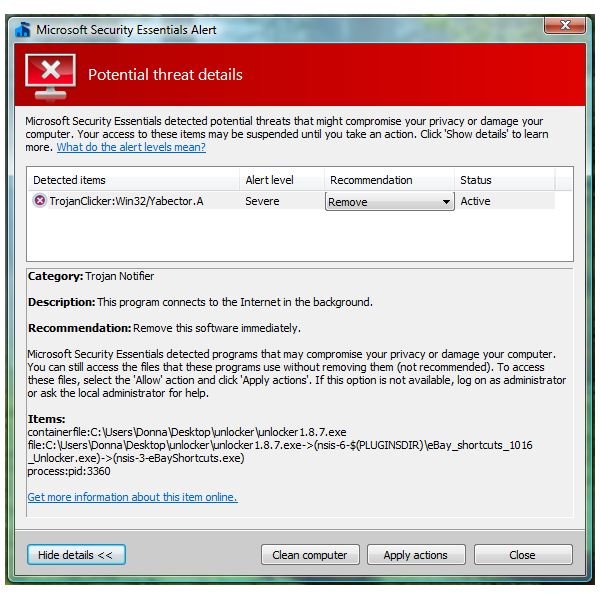
Not all Trojans will install fake or rogue AV because there are also Trojan horses that will install keyloggers to record and steal your personal information such as credit card numbers, login credentials, passwords and other valuable data.
A computer worm is another type of malware that will use your computer to infect other people’s PC in your network or spam your contacts. Worms often affects computers that are not protected with the latest security updates. Most worm creators will take advantage of unpatched security flaws in Windows (also known as Zero-day vulnerabilities). The infect computer may also become part of a botnet .
Viruses will replicate and reproduce by infecting other files in the computer, usually important files such as critical system files. It can infect other computers in the network or transfer through a removable drive such as a USB drive, floppy disc, CD or DVD.
If you suspect that the PC is infected by worms, computer viruses or a Trojan horse, use the following steps to clean the computer:
- The first step is to disconnect the computer’s internet connection. You have to do this to prevent your computer from sending spam across the network or to your contacts. If your PC has been infected with worms for several days and is being used as a robot or zombie in a botnet, your ISP should have alerted you!
- Use a clean computer to download worm, trojan and virus removal tools: McAfee Stinger , Microsoft Windows Malicious Software Removal Tool , Trend Micro SysClean , F-Secure Easy Clean or Dr.Web CureIT .
- Scan the computer using any of the above tools and reboot when prompted.
- Disable Autorun in any drive and check for updates for Windows and other applications. Use MBSA , Secunia PSI and Filehippo Update checker to determine what applications in your computer requires an update.
Please note that the above malware scanners in Removing Fake, Misleading or Rogue programs can also detect and remove Trojans, worms and viruses, but only use them if you have downloaded the anti-malware tools and its latest detection updates using another computer. Keeping your internet connection active may cause infection to other computers or infection of the tools themselves.
Image Credit: Wikipedia Commons/Luc.alquier (https://commons.wikimedia.org/wiki/File:Virus _ordinateur.jpg)
Removing Spyware, Adware and Potentially Unwanted Programs
Many legitimate programs will bundle their installer with spyware, adware and potentially unwanted programs (PUPs) to advertise or collect some information from computer users without their knowledge. The collected information can be sold or shared. Some spyware is nasty and will redirect your browser to an unwanted website or you’ll find your browser settings’ hijacked. To get rid of spyware, adware and PUPs, you need anti-spyware or anti-malware program. Your antivirus program should detect such risks. If you are using antivirus programs that actually bundle spyware or adware or does not actively detect spyware, you are better off replacing it. Any type of risk, even a simple privacy threat, should be detected and let the user decide whether to allow the adware, spyware and PUPs.
If you don’t have an antivirus program yet, consider using one of the free antivirus program from the list below:
- AntiVir by Avira
- Avast by Alwil
- Microsoft Security Essentials by Microsoft
- Panda Cloud AV by Panda Security
- AVG by AVG Technologies
If you rather use a paid or commercial antivirus solution, here are the best paid AV programs to date:
- NOD32 by Eset
- Kaspersky Antivirus by Kaspersky Labs
- VIPRE by Sunbelt Software
Please note that free antivirus programs are enough to protect your computer and are also good in removing known threats. Using free antivirus software does have its limitations. One of the limitations is the limited behavioral-based protection and detection. Consider using Trend Micro Rubotted , PrevX SafeOnline or ThreatFire in addition to a free antivirus solution. If you are using Windows Defender and the programs in the Removing Fake, Misleading or Rogue Programs section of this article, you should be fine as long as you regularly scan the computer using the tools.
To remove spyware, adware and PUPs, simply update the antivirus program or any malware scanner in the Removing Fake, Misleading or Rogue Programs section and then, run a scan. Close any opened browser or e-mail application to prevent interference in removing spyware or adware that was added or modified by spyware or adware programs.
Removing Rootkits and Using the Boot Sector Repair Tool
Rootkits are hidden files with administrator permission. They can install backdoors and Trojans and often target the boot loader, BIOS,
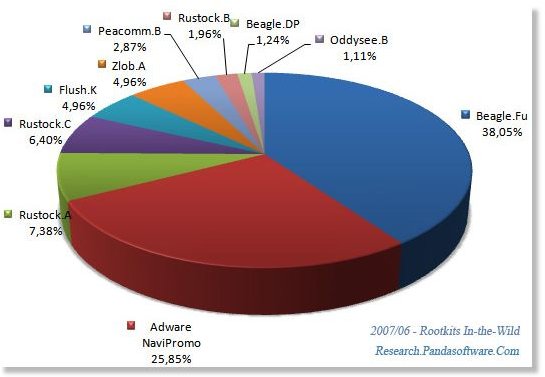
kernel and other libraries in the system. Many anti-malware software packages have rootkit detection and removal. However, there are rootkits that are hard to remove using malware scanners which means that you have to use a standalone rootkit scanner and remover:
If the boot sector has been infected, you need to use Avira Boot Sector Repair tool .
Google redirect virus is an example of a rootkit and Trojan infection. You need to use another computer virus removal tool to fix such infection. Most feedbacks that I received from readers of the articles says, TDSSKiller has helped.
When the rootkit scanner and remover fails to clean the computer, your only option is to seek help in Malware Removal Forums such as Aumha Forums or other HijackThis Forums .
Image Credit: Panda Research Blog (https://research.pandasecurity.com/rootkits-in-the-mist/)
Unbootable Computer Due to Malware Infection
When Windows don’t start normally by using any type of boot method, you need the help of other scanner. Before using any scanners to rescue your computer, consider using the bootable Windows disk to restore your computer to previous state. Windows Vista and Windows 7 users can use their installation DVD to restore the computer to previous state. Windows XP users should use the Recovery Console option.
Below are special tools to help you get the system back using virus removal tools:
- VIPRE PC Rescue
- [Kaspersky Rescue Disk](/tools/Kaspersky Rescue CD)
- Avira AntiVir Rescue System
- F-Secure Rescue CD
- BitDefender Rescue CD
- Dr.Web LiveCD
- Panda SafeCD
The download is in ISO file format which you need to burn using ImgBurn or similar program to a blank CD/DVD.