Virtual Private Networks use protocols to tunnel data from a client computer to a host computer by encrypting it. Apple Mac is a widely used operating system. This operating system was included because of its growing popularity. VPNs allow further security to your business environment.
Apple / MAC
I have access to an Apple / Mac and I elected to write about VPNs earlier this week. I am not an expert in Apple Mac computers, however I found it important to include the information below for system administrators wanting to create a VPN with this OS. The setup was easy. Several of the screen shots below were modified. This modification was made to hide key data on my network. In the final article, we will exam Linux Ubuntu.
VPNs and Apple MAC Computers
Below is a step by step guide on how to setup a Apple Mac Workstation on a Virtual Private Network
How to Setup a VPN on MAC OS X 10.5
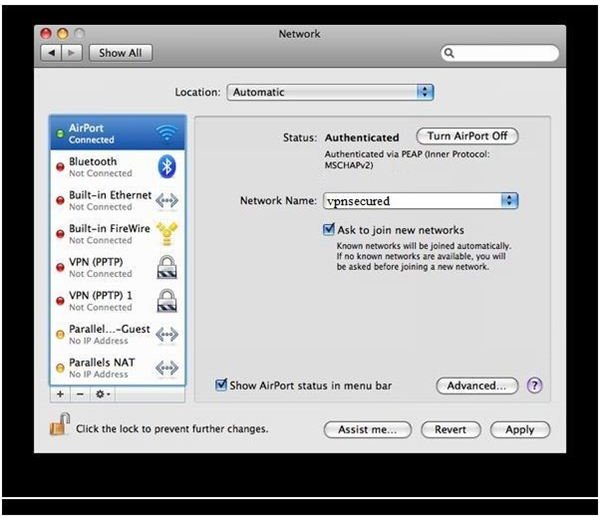
1. Choose Apple, System Preferences, and then click Network.
Selecting Network
Using the Network
2. Click Add (+) at the bottom of the network connection services list.
You may have to click the lock at the bottom if it is locked this is to activate the settings for Network)
Network Information
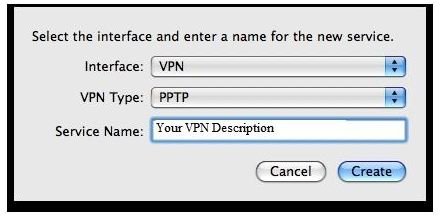
Selecting the Protocol
3.Choose VPN from the interface pop-up - You will see VPN
Choose “PPTP” from the “VPN Type”
Type in “Your Descriptor in the box” for the Service Name
VPN Type (Protocol)
Filling in the Address
- Type in the IP address in the “Server Address” box.
- Type in your username for “Account Name”.
- Choose “Automatic (128 bit or 40 bit) for “Encryption”.
Address Information

Password - Authentication
5.Click the Authentication Settings button.
Type in your password and click OK.
Password

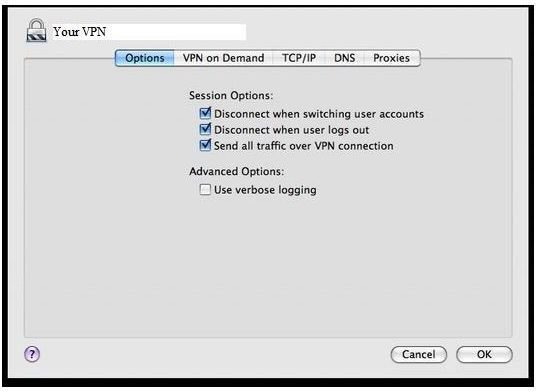
Options
6. Click on the “Advanced” button.
7. On the “Options” tab, make sure “Send all traffic over VPN connection” is checked-lick OK.
Directing VPN Traffic
Conclusion
Security Suites can block outbound traffic. The administrator should check any rules to ensure data is allowed out on specific ports. The most common port for a Virtual Private Network is TCP port1723. Other ports such as ports 50 and 47 may be used if GRE and ESP are used. If ISAKMP is used, it may be necessary to open UDP port 500.
After a connection is made to the server, your computer will obtain another internal private ip address from the server.
It is important to train users on how to use the VPN. Scripts can be added to map network drives to the server when using your VPN. This allows the user to have or share a folder on the server and ensures that whatever data is passed between the two is secure.
In the next part of this series, we will give a step by step tutorial on connecting Linux Ubuntu to a VPN server.
This post is part of the series: Virtual Private Networks in Business Environments
Virtual Private Networks provide encryption for your critical data while it is in transit to a server. This series gives a step by step tutorial on how to setup a VPN on Microsoft Windows Vista, Windows XP, Macintosh and Linux.
- Virtual Private Networks in Business Environments
- Virtual Private Networks in Buiness Environments: Windows Vista
- Virtual Private Networks in Business Environments: Windows XP
- Virtual Private Networks in Business Environments: Apple Mac
- Remote Access Service on Windows 2003 Setup Guy
- A Guide to VPN Setup in Ubuntu
- Virtual Private Networks in Business Environments - Wireless VPN Solution



