Plenty of encryption software exists on the Internet. This article talks about optimizing privacy and lists some encryption software for Internet security.
Is Encryption Sufficient?
Even if you have encryption related Internet security software, it might not be sufficient always. There are people out there who want to steal your data for their own benefits. They employ all possible tactics to get hold of your data so that they can use it for themselves or sell it off.
An encryption related security software encrypts only your data. There is much more to the data that travels on the Internet. This extra data, often found through headers, can reveal a lot about your browsing habits and may create particular interests in people who read it. These headers also reveal your Internet usage pattern to the hackers or anyone else interested in you.
The headers of each data packet reveal the source of data origin, the network it traveled through and the destination of data. If studied carefully by people with malicious intentions, this data can give out enough information that can be used to exploit you.
For example, if you are visiting an e-commerce website, the website may present you with increased rates for an item based on the country it intercepts by reading the data present in headers. Similarly, if you are accessing your company server from abroad, people can find out whom you work for and what servers you accessed - irrespective of whether the connection is encrypted.
After going through the above, you may have got an idea that using only an encryption software is not enough. You need anonymity too. Many people use proxy servers for anonymity. I suggest you use a pooled resource like “Tor” that makes it impossible for people to track you down.
How Tor Helps When Used with Encryption Software
Tor, when used in addition to encryption software for Internet connectivity, helps you stay protected so that no one can know what you are doing. Be it shopping online, sending out important emails, or collaborating on a project, people trying to snoop on you can never know what are you doing until you choose to make it public.
The Internet is actually a network of servers/computers spread across the world. When you start surfing or chatting, the network first assesses what all resources are free to get you a path for your data to pass. It then encrypts the header temporarily and passes on to the nearest free computer on the network. The receiving computer creates a new header instead of appending the previous header and removes previous traces. The resource selection is random and the path will change for each data packet involved in your communication.
The idea behind Tor is to offer a random (tricky) path so that by the time you reach your destination, the information about the source is lost. In this process, anyone following you will lose track as your data is passed from one pooled resource to another. Not even the computers in the Tor network can know where the original data packet originated and where it was going as there is no evidence left on the computer once the data is passed on to the next computer/server in the Tor network.
Though originally meant for US government and journalists, Tor is now used by almost everyone who understands the risks of being traced. Visit the Tor website for more detailed information.
CRYPTO - Free Email Encryption
CRYPTO is a free encryption related Internet security software that operates on the company website. The company offers several options to encrypt your messages and emails. You need not install the free version onto your computer to use it.
All you have to do is to open the website and select an online encryption method. In the resulting webpage, type the message or copy/paste the message. When you click on Encrypt, it encrypts the text using the algorithm you selected on the home page, under Online Encryption. To decrypt the message, select Online Decryption. Paste the encrypted message into the text box and click Decrypt. You can see the decrypted message in a readable form.
The method can be time consuming as you have to open the website and perform the additional steps for copy pasting. The encryption offered is strong but I feel personally that if I can access the website and encrypt the message, anyone who knows that I’ve been using the website can easily copy the encryption into those text boxes and decrypt them.
However, that’s just my personal thinking. You might find the service useful. Please let me know if you used it and are satisfied.
Comodo Email Internet Encryption Security Software
Comodo is a leading company in the field of security products. The email encryption software from this company offers you strong encryption for your emails. You need to download and install the software on your computer. When you install the software, it automatically detects the email clients you are using and configures them to encrypt and digitally sign your emails for making sure that the emails are encrypted and to check that they have not been manipulated in their course to the destination.
The service comes both free and paid. The service is free for individuals while enterprises have to pay for the secure email certificates. You can download the free encryption software and then decide whether or not you wish to buy it.
When you send the encrypted emails to your recipients, a copy of the encrypted email is stored on Comodo’s secure servers. The recipients receive a link to the email and a password so that they can click on the link and use the password to view the message. Alternatively, they can also download and install the free version of the Comodo SecureMail so that they can view the emails using their email clients.
FlexCrypt - Multipurpose Encryption Security Software
FlexCrypt is yet another security software for Internet encryption. Unlike the previous two, FlexCrypt offers encryption for offline files and folders as well. This offers protection against someone snooping on your messages on the Internet but also against unauthorized access to your computer’s hard disk.
Unlike the above two, FlexCrypt comes at a cost. You can download FlexCrypt for a 30 day trial period. You can also use TrialPay to get it for free. For using TrialPay, you need to buy something else from its affiliates so that it compensates the cost of FlexCrypt.
These are three encryption Internet security software options that when used with Tor, provide maximum protection to your online communications. If you wish to add anything, please feel free to use the comments section.
References
https://www.torproject.org/about/overview.html.en
https://www.comodo.com/home/email-security/secure-email.php
https://www.flexcrypt.com/flexcryptfree.html
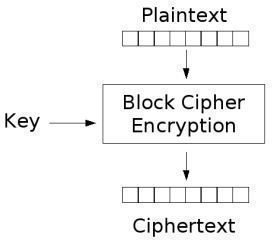
Image on page one from Wikimedia Commons by LunkWill
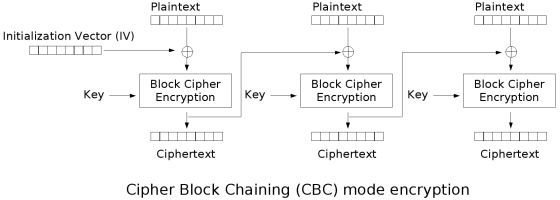
Image on page two from Wikimedia Commons by Unknown
This post is part of the series: Encryption Software
This series contains articles that talk about encryption and methods to encrypt data for different uses.