Phishing is a continuing problem in today’s world. With information easily available, hackers and social engineers constantly evolving their attack methods, its easy to become a victim of a phishing attack. Understand the best practices to take to prevent being phished and to protect yourself.
Know Your Enemy
In a way, phishing is a multi-million dollar business, with accounts being stolen, used and sold every day. Its a constant topic of discussion on security forums and news channels with people from all over the world being affected. The best way to prevent yourself from being a victim is to understand the processes in place used by hackers and social engineers.
Before reading the preventative tips, I suggest you read my previous articles to understand phishing:
- Phishing Attacks and Techniques
- Social Engineering - Hackers and Social Networks
- Phishing and Identity Theft
- Phishing Versus Spoofing
In the articles above, I explained the attack vectors currently in place and at times, a brief idea of how to prevent yourself from being a victim. By reading these you’ve already taken the first step in phishing prevention and protection. Like any battle, knowing your enemy and understanding their attack vectors is the first step in fighting back.
Know Yourself
“If you know the enemy and know yourself, you need not fear the result of a hundred battles…” - Sun Tzu,
The Art of War
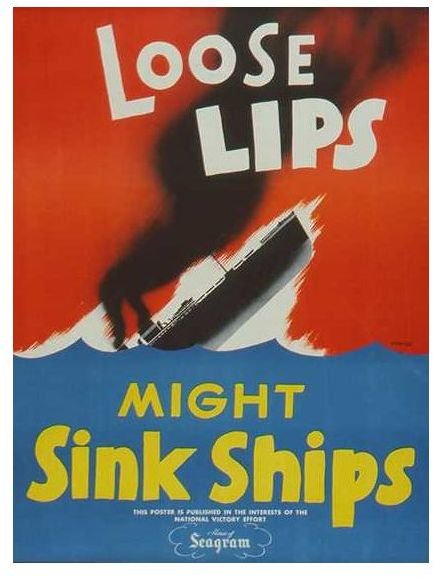
Now that you know the enemy, its time to know yourself. During World War 2, loose lips sunk ships and people were told to keep a tight lip around any type of information they may have had that could endanger their fellow troops. The same idea exists now in this cyber war against hackers and social engineers looking to phish accounts from victims.
Knowing yourself may seem like a simple idea but its much harder than one would expect. People, in general, have a tendency to trust others on the internet, not quite like the world outside of the internet. How likely are you to fill out a form asking for personal information sent to you from your bank over e-mail as opposed to someone knocking on your door and asking for the same information? How often do you click links from e-mails as opposed to walking down an unknown alley pointed out to you by a stranger? Are you more likely to think twice before typing in your social security number or credit card number in a form online, as opposed to writing it down on a piece of paper and sending it over mail?
The internet has an odd sense of ingrained security for some people. The idea that since information is being requested and placed into a computer makes some people feel as though it should be secure, that it needs to be secure, otherwise why would it be through a computer?
Part of phishing prevention and protection comes from being proactive and knowing the type of information that you give out without a second thought. The easiest way to know yourself is to compare the internet you and the you outside of the internet.
Prevention and Protection - Winning the Cyber War

Knowing the attack vectors and knowing how easily you trust internet sources are key items for phishing prevention and protection. The other key items is to be proactive and not reactive. Think two steps ahead of the game, look at the types of information that is currently available to the internet about you, and change your ways to prevent more information from getting out there.
Take a few minutes to read up on the latest phishing scams and check, are you placing the same type of information online? Understand the new attack vectors that are coming out, whether it be Facebook phishing attempts, Twitter feeds that link to malicious sites, latest viruses and trojan horses that have been coming out, its all important and should take about, at most, a half hour out of your day.
Think of phishing as a game of chess. Your information is the King and all the pawns, knights, rooks, bishops and queen in the game are the protective measures you take. You can easily just throw away all your pieces and throw caution to the wind, or you can prepare and prevent your King from being caught in a dreadful checkmate.
This post is part of the series: Phishing - Hook, Line and Sinker
Phishing is a constant thorn in security’s side and a constant reminder of how trusting people are, even to anonymous sources. Understand how phishers take advantage by learning their attack techniques and learn how to prevent and protect yourself from being a victim.