Whether it is keeping your passwords secure or protecting a vast network from catastrophe, the elements of maintaining computer security are ever shifting as security threats evolve and develop.
With scheduled scanning, real-time protection software, and the overall increased automation of IT security, it is easy to become complacent when it comes to defending your website or network. Yet both IT professionals and casual users can benefit from constant training, if only to gain insights into the latest threats and security technologies. Refresher training is essential for any IT security professional due to the fact that threats and methods of dealing with them are constantly adapting. Also, the more certifications you have, the greater your earning power! The IT security community on the Internet is vast, so we here at Bright Hub have collected a comprehensive list of resources for every security experience level.
Know Your Enemy
New computer security threats are being developed on a daily basis. With modern software tools, even an entry-level programmer can now create bots, viruses, and other malware in a matter of hours. Before you can react to a threat, you must be aware of its existence. Even premium security suites are vulnerable to a new threat until it is added to a database. In addition to targeted threats, networks are vulnerable on account of such inanities as outdated equipment, human error, and negligence. Therefore, whether you are an IT professional, business owner, or an individual PC user, up to date knowledge is your first line of defense. The information here can improve security on a single PC, a small business network, and even a full-fledged enterprise system.
- List of Network Security Threats: It’s Not All About the Malware
- Common Online Fraud Methods: How to Spot and Avoid Them
- Computer Security 101
- Small Business Network Security Standards
- How to Find Free Online Security Training
- Basic Course For Key IT Employees (For any Organization)
- Types of Wireless Network Attacks
Tips, Tutorials and More
It is well known that these days, the simple act of surfing the web can expose you to all sorts of incursions on your privacy. From phishing websites to online behavior-tracking bots, almost every move made online by an exposed user can be tracked and cataloged for purposes fair and foul. There are some simple steps that can reduce the data mined online from the surfing activities of you and your users. Every operating system and most popular web browsers come equipped with a certain level of defenses that are absolutely useless if you are unaware of them or do not have them correctly configured. Fortunately, there is no shortage of resources on how to access and implement these included features. If you conduct any kind of financial transactions online, it is important to know that your site and the data that passes through it with each sale are ripe targets for data thieves. Failure to protect your customer’s data can expose you to damaging comments and negative user reviews at best, and at worst, crippling lawsuits.
- Computer Security Resources for Beginners
- Protect Your Users With Anonymous Web Browsing
- Beginners Guide to Trojan Removal
- How to Prevent Your System Users From Installing Potentially Dangerous Software
- Free Guide to Securing Fax and Email Messages
- E-commerce Security Guide
Software Guide
Each user or organization has different needs and budgets, therefore some knowledge about the different software options is essential when installing or upgrading your current security suite. This collection of reviews, comparisons, and tutorials is designed to give the reader an unbiased and balanced assessment of the available security tools. Both network professionals and casual users are faced with the dilemma of balancing protection and system performance. Some software suites that provide first-class protection have the effect of significantly reducing system performance. While this is a sacrifice well worth making, your network has many thousands of sensitive data sets. Someone with a system optimized for speed and performance without such a data liability may benefit more from a suite with lower system loads. If you have an internal network or are hosting your own website or forum, network monitoring tools are essential for keeping an eye on your users and detecting intruders.
- Quality Security Programs With Low System Requirements
- Is Norton’s Protection Worth the Loss in Performance?
- Best Free Firewalls for Windows 7
- Norton Antivirus Vs Avast!
- Designing Your Own (Hopefully) Impenetrable Network Security System
- The Best Network Monitoring Program s
Professional’s Corner
Thus far we have focused on information relevant to all PC users. IT network professionals can benefit from all the resources above, but there are tips and tricks specific to maintaining the security of a large network or an enterprise suite. Here you may find resources to brush up on your knowledge, or get pointed in the right direction as far as becoming qualified as an IT security professional. Even if you have been managing a network for years, you know very well that pro’s have greater ongoing training needs because the security manager who doesn’t stay up to date is like a general trying to fight tanks with cavalry. IT professionals must also be up to speed on the latest regulations. Simple actions such as deleting regulated data can cost you your job and even lead to prison time. We include some of the most recent (2011) regulations that every system administrator must abide by.
- Advanced Avast Antivirus Tips: Why its The Geek’s Favorite
- Online Courses to Become an IT Security Professional
- Collection of Free Security Training Resources
- Best IT Security Magazines for Pros
- Keep Your SOX Clean: Sarbanes Oaxley Data Protection Regulations
- Boost Your Salary with a Free certification From Cisco
References
- Author’s Knowlege
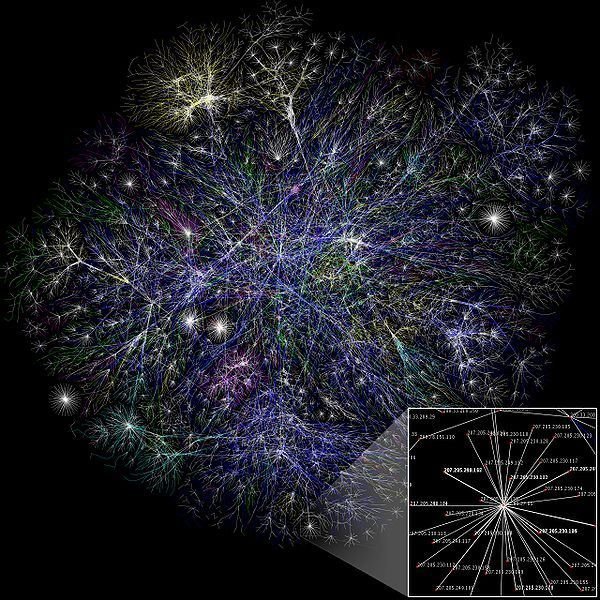
- Photo Credit: Map of the Internet , Licensed under the Creative Commons Attribution 2.5 Generic license.