Mainstay security provider Symantec has launched it’s latest salvo in the personal internet safety and security space: Norton Internet Security 2008. The suite comes packed with features and at $59.95 the suite offers a lot for the money. But is this veteran ready for retirement or has it been reinvented to compete with the new hot shots in the barracks? Read on to find out.
Overview
A solid package that offers plenty of robust features.
Price: $59.95 for a 1 year subscription for use on up to 3 PCs
Main features: Virus scanner, firewall, email and IM scanner, password manager, form filler, rootkit detection, network security manager, subscription model
Vista supported: Yes
Product link: Norton Internet Security
Setup (4 out of 5)
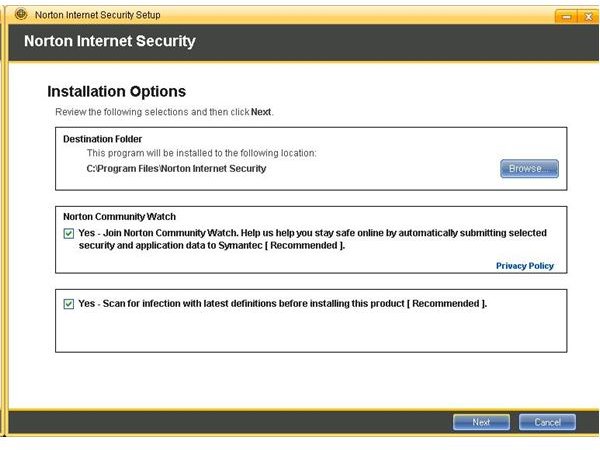
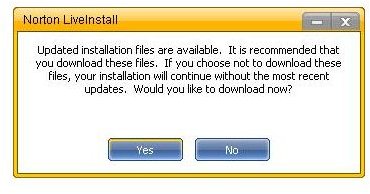
Setup was smooth and unproblematic. The setup application offered to download updates before setup began and to do a scan of the computer after the product was installed. Setup appears to be written as an application in and of itself in that it performs the tasks needed to not only install the software, but prep the system for the software and for creating a secure environment on the system. In the days of pre-packaged setups, this is a refreshing attention to detail.
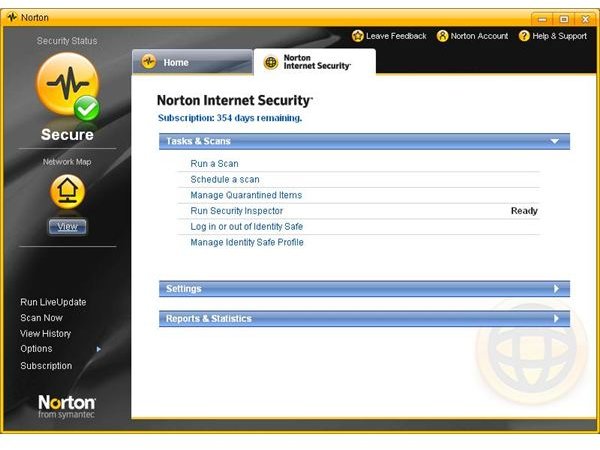
User Interface (4 out of 5)
The user interface is polished and solid. The icons and buttons are contemporary and a pleasure to look at. This is a UI that one wouldn’t mind spending some time in. The interface invites the user to explore and engage with the product. But this is also a negative as the interface can appear somewhat busy. The main UI includes two tabs, “Home” and “Norton Internet Security”, from which the system’s features can be accessed. To the left of the tabs is a general status icon, an button that provides a handy “Network Map” and a list of common tasks like “Scan Now” and “Run Live Update”. The UI is keyboard accessible.
The “Home” tab provides information about the computer (mainly spyware and virus protection), the internet connection (email scanning, the firewall, and intrusion protection) and personal identity protection (phishing protection). In a single view, users can check the security status–or at least Symantec’s interpretation of the security status–of each of these areas. Clicking on any of the sub areas under the general categories provides rationale for why the area has the status it does. The Home tab provides no access to the tools themselves.
The Norton Internet Security tab provides the interface to the tools such as the virus and malware scanner, the security inspector, and Identity Safe. Users can also view or change the settings for each of these tools and view reports on scanning activity and phishing protection (which sites the tool blocked or how many were authenticated).
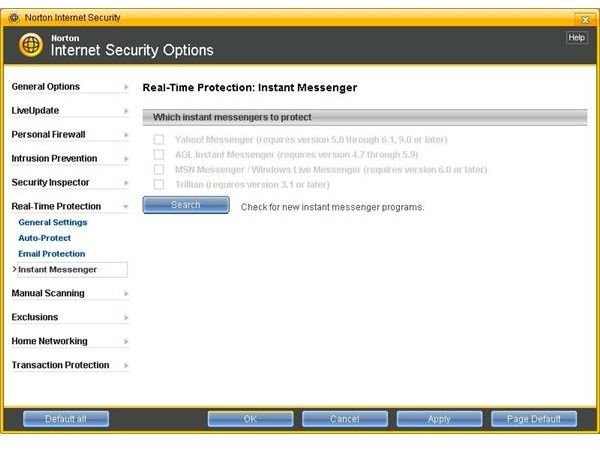
The UI in general was clear and generally responsive though on my 2.2Ghz Celeron with 760Mb of RAM (Windows XP SP3) I did notice some lag in screen redraws. As with most modern security tools, the UI exposed access to common tasks like scanning or information about problems with the system in 1 or no clicks. But Symantec didn’t ignore the power user either. For those interested in tweaking specific settings, the UI provides adequate access to lower level settings for all the tools. In fact, I was very impressed with what Norton Internet Security allows users to tweak. For example, it is possible to enable the scanners scan Microsoft Office documents when they are opened or scan files received by instant messaging applications. These features can be enabled or disabled rather than being a part of a larger “black box” scanner with no granular control.
The UI includes some satellite UI elements like a task bar icon (or button – the distinction between having one enabled over the other is unclear) and a phishing filter toolbar in Internet Explorer. The browser toolbar includes a password manager, form filler, as well as phishing filter status information. The browser bar lacks subtlety and users who choose to leave the toolbar enabled with be stuck with a big “Norton” in their browser toolbar area.
Overall, the design and function of the user interface is very good. It certainly contends with many of the top security tools I’ve tested from a form and function point of view. Of course, a usable interface is a matter of personal preference in an important way but Symantec has done a good job with the technical elements and has built in enough customizability to please, I would guess, most users.
Features (4 out of 5)
In addition to the primary features like the firewall and scanning tools (both are discussed in detail in subsequent sections), I want briefly to look at some of the “extras” included in the suite. Some of the tools included in Norton Internet Security Suite 2008 are included with most modern browsers. Thinks like phishing filters or password managers / form fillers come with major browsers like Firefox and Internet Explorer. Symantec offers their own version of these tools and using them will be a matter of personal preference.
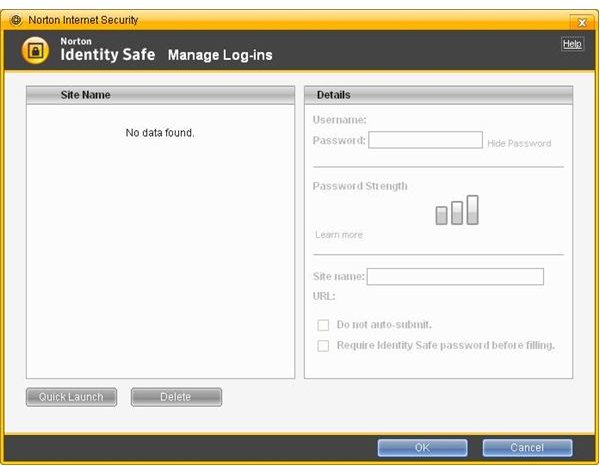
Identity Safe
The forms information and password manager, Identity Safe, has two main components. The forms filler consists of what Symantec calls “Identity Cards” and allows you to save three types of information. Each card supports including an image for easier access. A general tab appears to be a simple, personal contact card which includes basic personal information and, interestingly, a space for your OpenID URL. The contact tab is more detailed contact card similar to what you’d find in an email application. The final tab is for credit card information. Each card can be individually password protected and the Identity Safe application itself is password protected.
The log in manager wasn’t so streamlined or simple to use. In other password managers I’ve used (notably the on included with Windows Live Toolbar and an excellent password manager called RoboForm), when I hit a web page that contained credential fields, the manager would prompt me to save the user ID and password. Internet Security’s version did not appear to do this. Also, I could not find a way to add credentials using the “Manage Log-ins” interface. Finally, a perusal of the help file wasn’t much help either. After spending 5 minutes trying to figure it out, I gave up. If I have to spend more than that amount of time trying to figure out how to use a simple time-saving feature, I’m not sure it’s worth the investment. I finally discovered that I had to enter my credentials and click the login button before password manager came alive and prompted me to save the information. A visual cue of some sort that would let me know that Log-in Manager is aware of the page would be helpful. Windows Live Toolbar, for example, changes the background of the boxes it detects to yellow when a page loads. I like that.
Intrusion Prevention and Crimeware Protection
Norton’s Intrusion Protection feature is designed to protect your computer from intrusions which Symantec defines as an attack vector identified with network traffic information that contains specific signatures. These signatures are stored in a database and Internet Security checks your network traffic to see if any of it contains a malevolent signature. It seems to be similar to virus protection but whereas viruses typically are downloaded and run from the computer’s hard disk, this type of attack is able to do damage right from the network stream.
Crimeware Protection (Crimeware is a term I wasn’t familiar with prior to this review but apparently is an “official” term in Internet security) is designed to protect personal information from being stolen while you’re online. This is the description of the feature from Internet Security’s help file, " Crimeware Protection scans your computer while it is connected to the Internet. Crimeware Protection looks for programs that are trying to capture any personal information you are entering on any Web page. If it finds any crimeware, Crimeware Protection blocks the crimeware and submits it to Symantec for analysis."
Remote Monitoring
Norton Internet Security 2008 includes a central management features which allows a single computer to manage the security of remote machines. Each satellite machine has to have Internet Security installed and each machine has to be set up separately. The visuals for the system are the best I’ve seen with tabs for each computer on the network and an informative information screen that allowed me to get a status update with a quick glance. I’ve used Microsoft’s OneCare central monitoring feature and, while it works well, it’s messy and difficult to glean important information quickly. Norton’s user interface is far superior in this regard.
Other Features.
As I stated in the introduction, Internet Security 2008 comes packed with features too numerous to mention here. Interested readers should download the trial and spend some time going through the user interface to determine whether the extras might be helpful or would just take up extra disk space.
Firewall (3 out of 5)
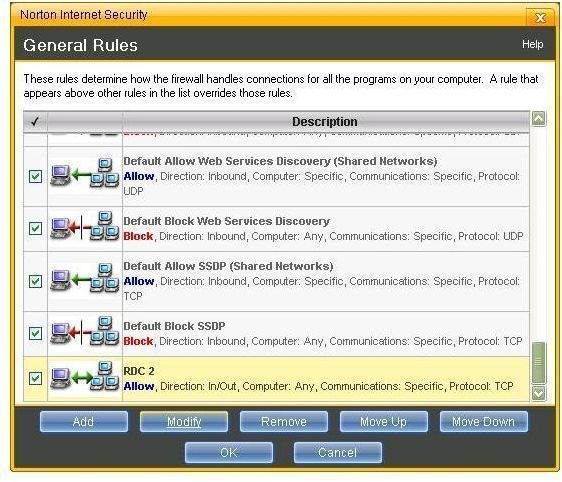
I reviewed Symantec’s standalone firewall program for Brighthub here . Symantec seems to have not included the same application in this suite or modified substantially enough to solve many of the problems I encountered with that application. The firewall in Norton Internet Security seems to be much more intelligent and far less intrusive than the standalone product I tested. In fact, I received very little by way of dialogs, popups, or even system tray warnings. My Google sidebar was able to download RSS feeds with no problems and Internet Explorer downloaded my home page without being blocked. Beyond being intelligent, the firewall is powerful and provides access to a substantial level of granularity when it comes to reviewing firewall status or setting firewall exceptions.
In fact, this level of granularity caused me some problems when I attempted to set an exception for my Remote Desktop Connection. It took me multiple tries to tweak the settings so that I could connect to the machine using RDC. I ran into two issues. The first was deciding whether the connection was inbound, outbound or both (using “both” worked). The second was whether I wanted to allow local or remote ports which fell under a “locality setting.” The help file for this setting reads, “This rule can be applied to local and remote ports. Local ports are those on your computer that are usually used for inbound connections. Remote ports are on the computer with which your computer is communicating. They are usually used for outbound connections.” But since I was opening a port on this computer but wanted to allow a remote computer to connect to it, I wasn’t sure which was appropriate. I went with local port and that worked.
The firewall also includes the ability to trust or restrict networks (typically referred to as zones) and quickly view a list of trusted and restricted zones. I anticipate that most home users are on a single network so this feature would not come into play but for small businesses, this feature could be quite useful. Unfortunately it is not possible to put the firewall to sleep from the taskbar icon and like the standalone product, its not possible to sleep the firewall for increments other than the one’s Norton provides (15 minutes, 1 hour, 5 hours, until system restart, or permanently).
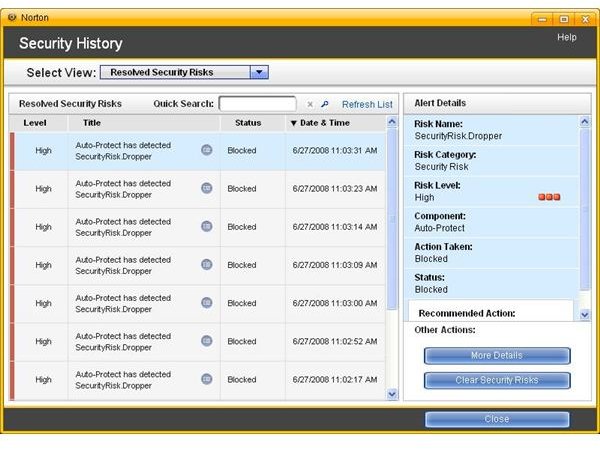
Virus and Spyware Protection (4 out of 5)
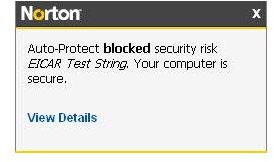
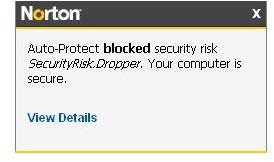
Virus and spyware scanning are done together in Norton Internet Security 2008 so I will treat them as a single unit here. I tested the virus and malware scanner by using the test files on Eicar.com Norton Internet Security 2008 blocked each test file including the file in the zip package (I tried to run the file enclosed in the Zip package without first copying it to my hard disk). The scanner was responsive and I noticed no noticeable lag or delay.
To test the spyware scanner, I used the test suite on Spycar.org. As with the virus scanner, the spyware scanner worked like a champ easily catching everything the Spycar suite threw at it. In fact, when I wanted to download a valid file from Spycar, Internet Security would not let me and I was unable to find an easy way to create an exception for the file I wanted. I had to actually turn off real-time scanning in order to download the file.
From the very basic and preliminary tests I ran, Internet Security 2008 performed well and would seem to keep your system safe from malevolent software.
Conclusion
Symantec’s Norton Internet Security 2008 is one of the better security suites I’ve tested. Many of my criticisms of previous Symantec offerings–overprotective firewall, sluggish UI, and cumbersome installer–have been addressed. The protection provided by the suite seems robust and the package is feature-rich. Since security software really proves itself in the real world, I always recommend that users download the trial software and test the package in their own environment before purchasing.
Images