Packet filtering firewalls, as the name suggests, filter packets of data coming into and going out of your network – as you set it. It forms one of the common types of Firewalls and this article explains what they are, the advantages and disadvantages, and gives some examples.
I wager on one thing - there is never a time when you won’t need a firewall. Having said that, almost all of us have heard the “term” firewall at one point or the other, and that makes me think about the sheer importance “firewalls” have for users who connect to networks or the Internet itself.
A packet filtering firewall examines data packets (in large chunks or “Bytes” as you might like to call it) as these data packets move through the firewall. It then compares what it gleans through this packet of data with an already established set or rules ( as set by the individual or by the company) and then take decisions based on where it is coming from; where it intends to go; which port is being connected to and from where.
A primary advantage with using a Packet Filtering Firewall (PF) is that it is fairly easy to set-up and configure.
Firewalls: Packet Filtering Examples
As an example, if you wanted all your users within a company’s network NOT to use the Internet and browse websites because you thought they were wasting your time, you could configure your firewall such that it blocks all traffic going out of Port 80 ( a standard port used for web traffic, http protocol, etc) which will effectively curb all traffic requests to Internet Servers from within the Firewall’s systems.
On the other hand, if you wanted no one to see your website, which is being held secret until launch, you could block all the incoming traffic to the site’s web address through the same Port 80, which will deny any one from outside from taking a peek at your website.
The disadvantage with Packet Filtering is that the filtering is severely limited to just ports and IP addresses, and not the content. If you look at the way Internet Security threats are shaping up, a lot of them have to do with content too.
It can be used by anyone and on any network as deemed appropriate. However, it has certain limitations which the Packet Filtering type of firewall fails to combat. On top of that, customizing the way this type of a firewall works demands expertise which many normal users don’t have.
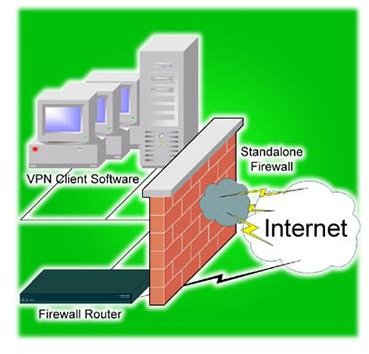
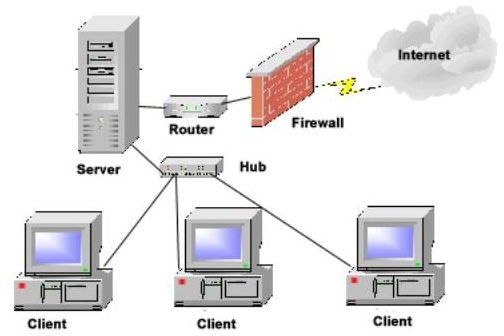
Images
Othe Information on Firewalls:
>»>Denial Of Service Attacks : What are they?
>»>A Beginner’s Guide to Firewalls : An Introduction
>» [A Beginner’s Guide to Firewalls: Debunking the Top 5 Myths about Firewalls](/tools/A Beginner’s Guide to Firewalls: Debunking the Top 5 Myths about Firewalls)