The Windows Malicious Software Removal Tool and Windows Defender are system scanning applications that do not provide full antivirus protection. However, they are present on any Vista PC that has Windows Update and can find malware that even the major antivirus packages sometimes miss.
The Microsoft Malicious Software Removal Tool and the Windows Defender anti-spyware, anti-adware removal tools are sometimes maligned because they offer limited usability and don’t act as antivirus or protective tools. That’s not their function, but both are easy to use, have graphical interfaces, and can be run on demand. MS MSRT even has a deeper scan function that you can run manually. (The default is a Quick Scan, and that is what runs after Windows Update.) Similarly, the Windows Defender scan runs automatically and can be run by hand, but it has some interesting features that are not normally accessible to the user, too.
Think of MSRT and Windows Defender as “after the fact” utilities. Both have a list of items that they will look for and can remove, often without requiring a reboot. Anti-virus tools must be more robust and smarter because they have to deal with threats that are unknown, just arising, or actively evolving in the wild. MSRT and Windows Defender only deal with threats that have been identified and for which a removal method is known, which is good for those who are not running any other protection at all.
Let’s see what we can do with MSRT and Windows Defender.
Run a Full Scan in MSRT
You’ll want to run the scan when you have some time to spare or can leave your PC on overnight. Yes, the scan can take that long.
To access MSRT in Vista, click the Start button/orb and enter “mrt” in the search entry field. That’s right - if you search for “MSRT,” you won’t find it. The actual application name is “mrt.exe.” It should appear at the top of the list, so press Enter to start it.
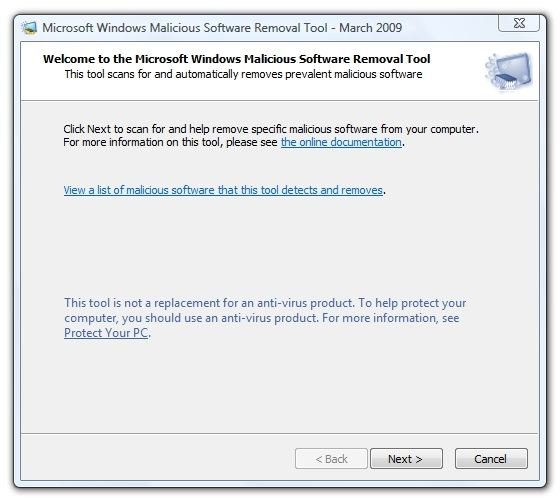
The first thing you’ll notice in the MSRT window is the link to the documentation. This takes you to Microsoft Knowledgebase article 890830 which does a pretty good job of explaining what MSRT is and what it is not. A point to take away is that MSRT removes threats from a computer that is already infected. In other words, it has no ability to block infections. That job is left to antivirus software. (MSRT is designed to cohabitate with your existing antivirus service.)
Here’s the MSRT startup screen. (Hover over the image to read the caption or click it to enlarge.)
MSRT is designed to run automatically, usually on or shortly after the second Tuesday of each month when the newest version of the database is downloaded by Windows Update or Microsoft Update.By default, this will be a “Quick Scan.” MSRT will rarely request that a full scan be run unless it finds an active threat. This is operating under the assumption that if you have one threat, others may also be present.
To manually run a full scan, click the “Next” button and select “Full Scan.”
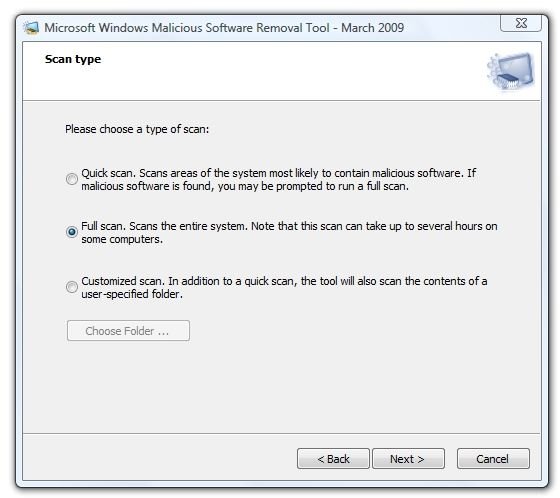
In the image below, the scan had been running slightly over an hour. This is a relatively fast “multimedia” 500 GB hard drive that’s almost full, so this is a relatively slow process.
Be warned, if you happen to have a couple of Linux ISO image files on your hard drive, MSRT won’t be happy until it’s disassembled everything in the image and peered at it. It’s as though Microsoft thinks that a Linux distro just has to be evil. As I write this, it has spent the last hour looking at “OpenSuse-11.1-DVD.iso” and is still working on it. It is also six hours, twenty minutes into the scan. MSRT has looked at 1,460,981 files and seems like it’s about 90% through. I am very glad I don’t have a bigger hard drive.
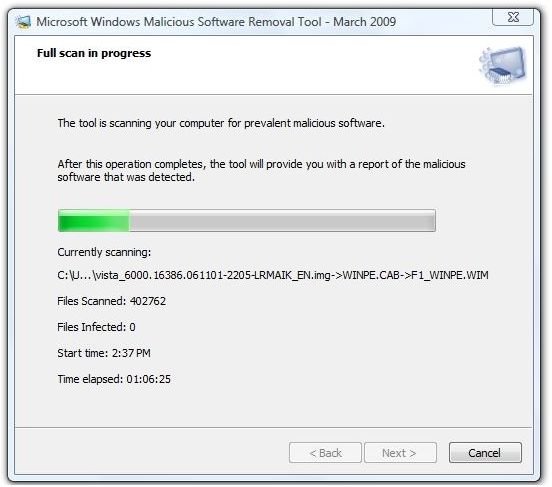
The entire scan ran for 7.5 hours and the conclusion was both precise and anticlimactic. It said, “No malicious software was detected.” It managed to examine 1.8 million files on my computer and presented a link called, “View detailed results of the scan.” Clicking this produced a list of all the malware it looks for with each line labeled, “Not infected.” That’s great, but it took a long time to find that out.
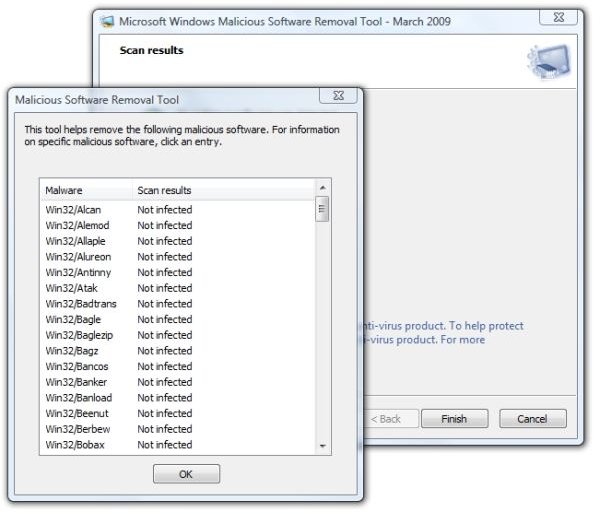
Still, this meets the objective, which was to run a full scan rather than the abbreviated “Quick Scan” that MSRT normally does, and we can now be confident that the malware that MSRT knows about is not present or running on this PC.
If malware were found on your PC, MSRT could have notified you, prompted you to remove it or even run a heavier-duty antivirus product to finish the repair. If you want to see the log of the current and past MSRT runs, navigate to Computer → C: Drive → Windows → Debug and use Notepad to open Mrt.log.
At this point, we know what’s not running and not lurking on our PC, at least of the items in MSRT’s list of malware. Let’s continue by finding out what applications are running on the PC.
Find Out What’s Running with Windows Defender
To start Windows Defender, click the Vista Start button/orb, type “Windows Defender” into the search entry field and press Enter. Here’s what Defender looks like at startup.
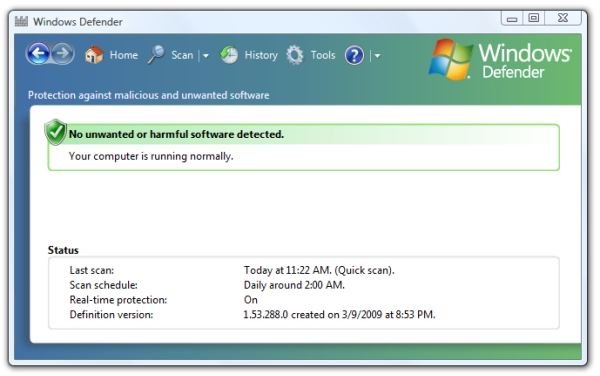
Options from the startup dialog include running a scan, obtaining a scan results history, a Tools menu, and Help. Other than the scan for spyware, of course, the most interesting feature Defender offers is under the Tools menu. Scroll down if needed, and you’ll find “Software Explorer.”

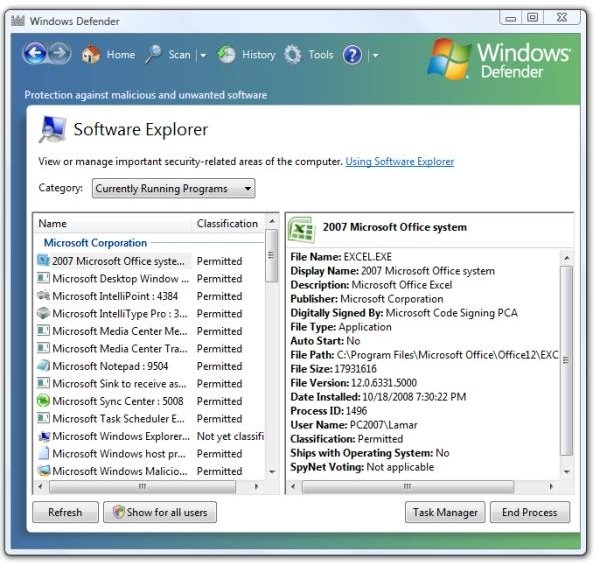
This is pretty nifty - this shows you a list of all your currently running applications and information about each one, including those that are not running on the desktop and are therefore not visible.
This information is available in other areas of Vista, but is not found without digging around in the plumbing or clicking around in Task Manager. Having it available from the Defender interface is a very nice free bonus.
Here’s what the Software Explorer section looks like.
Next: More of What’s Running, Doing a Full Scan in Windows Defender (and finding something!)
While looking at the list, I found an application that I had trialed some time ago, but decided not to purchase. To my surprise, I found it running. Hmm, I thought, did I really buy it? Or didn’t I uninstall it?
No. The application was still installed, and it had a process running on my system. I started it up and discovered that it was running in order to tell me that the demo period had expired. With it selected in Windows Defender, I selected “End Process” and then went to Control Panel to uninstall the application, and that was that.
Other useful information is the file name and path, whether it’s part of Windows, and the Process ID (or PID) the application is running under.
The Software Explorer in Defender is very handy for identifying applications running on the PC. If you find one that you can’t identify from the description and program location, often a Google search for the executable’s name will provide more information. Try to avoid stopping or uninstalling processes or applications that appear under the PC manufacturer’s name, as doing so may have unintended side effects like losing the keyboard functionality.
Now we have looked for trojans, viruses, and worms on the hard drive, and we have a handle on the applications running on our PC. Next, let’s look for adware and spyware
Run a Full Scan in Windows Defender
As with MSRT, Windows Defender’s default action is to do a “Quick Scan.” During this, it looks in places where it thinks that spyware is most likely to exist. Select a Quick Scan by clicking the “Scan” link at the top of Defender dialog. Start a full scan by clicking on the down-arrow immediately to the right of the Scan link and selecting “Full Scan.”
Here’s what it looks like when the Full Scan is running.
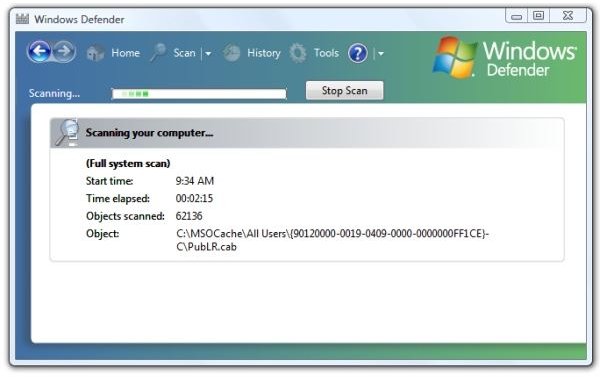
The full scan using Defender took 3 hours, 44 minutes and scanned 1,900,306 items. It found two items.
One was “Monitoring Tool:Win32/Overspy.” This is an application that can watch a computer and send a report away periodically about activities on the computer such as websites visited and keystrokes entered. I decided at the time that it was not worthy of review, so I deleted it and forgot about it. Defender correctly found that it had left files behind in the Win32 folder and in /Program Files/Over. It had also failed to clean out some values in the Registry. This was simply laxity on my part in not following up to see if Overspy had cleaned up after itself.
The other item found was “HackTool:Win32/PWDump.A.” This was part of an application that I looked at when researching for my article “Prepare a Laptop or Desktop PC for Sale, Giving Away, or Recycling .” I was looking for a safe way to recover website passwords from Internet Explorer without having to visit every site that had a password. I did not actually install the program. It’s sitting in a topic folder in my Bright Hub hierarchy. Let me also warn you that this business of obtaining passwords is fraught with the danger of getting a trojan, worm, or virus. For every legitimate application I looked at, another nine were dubious.
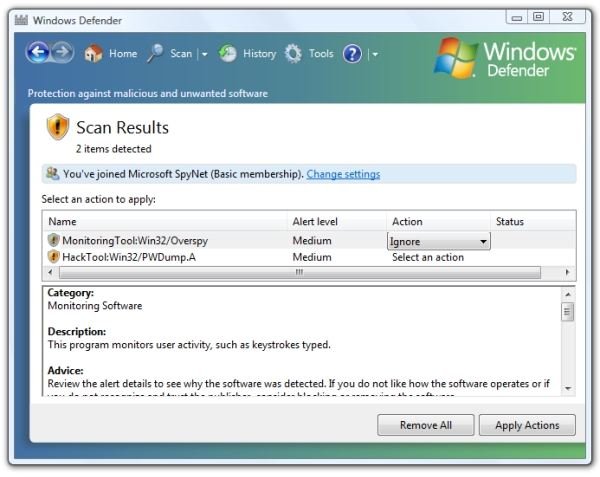
Since Defender had found these items, it seemed logical to let it deal with them, too. In each case, I selected “Remove” under the “Action” column and then clicked “Apply Actions.” It soon showed “Actions completed.” Let’s see what it did.
In the /Program Files/Over folder, it removed the “nt32.dll” file. It left behind the program folder and a file that its a shortcut (link) to their website. I then deleted the directory and checked the Registry. Overspy was finally gone.
Defender also deleted the RockXP file in my temporary working directory that was the source of the Win32/PWDump.A file.
Wrapping Up
In conclusion, I think it’s wrong to dismiss the Microsoft Malicious Software Removal Tool and Windows Defender as lightweight, limited programs. They are not intended to be full-suite antivirus/adware/spyware/malware solutions.
MSRT is aimed at known security problems that exist right now. It can be very effective, too, in stopping the spread of a virus, trojan, or worm by removing thousands and thousands of copies of the rogue program in a short time. This can have a shocking, chilling effect on netbot networks when a large proportion of the captive boxes in the network suddenly “go dim.” It’s also nice that MSRT looks everywhere - inside zip files and inside ISO image files, for example.
Windows Defender is an easy way to find out what applications are running on your PC and scan for known malware. I really didn’t intend to give Defender the workout that I did, but the items that it found were valid.
MSRT and Defender are especially long-running when doing Full Scans, but they work, compliment installed antivirus applications, and are decent, useful tools in the struggle between users and malware writers.