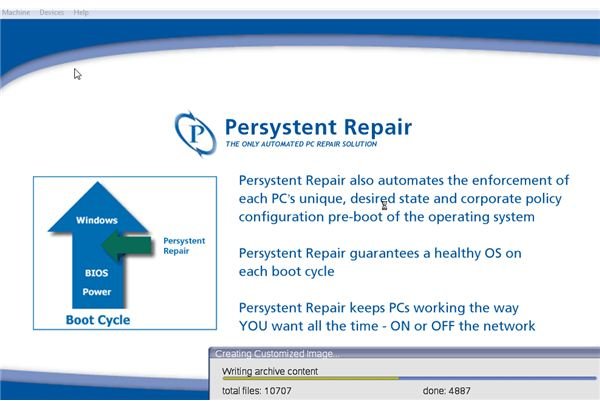
Want to keep windows running all of the time even if your windows install is corrupt? Persystent Repair checks your system files, windows state and registry before windows starts. This software starts before your operating system loads ensuring business continuity and up time for your workstations
Overview
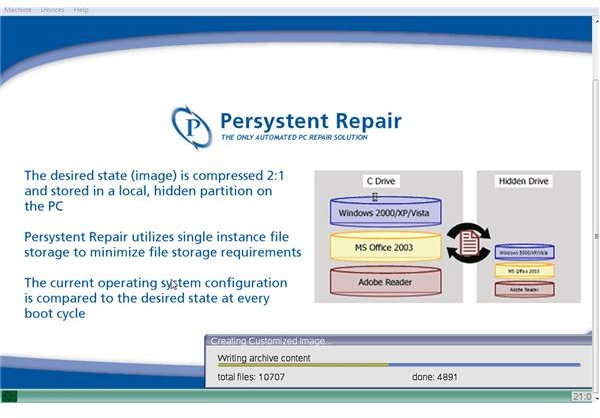
Persystent Repair is a new technology recovery system for workstations. Persystent checks and protects windows files, system state and system registry. Persystent Repair checks the operating system before the operating system can begin to boot and engage. With this checking your system just after the BIOS, this software is used for business continuity and disaster recovery. Although the software does not back up data files, it makes sure your computer’s operating system remains fully functional.
Installation (4 out of 5)
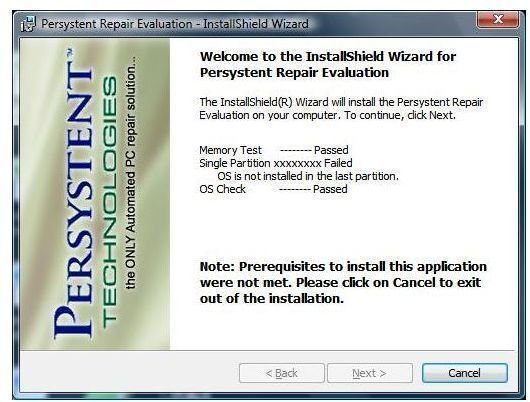
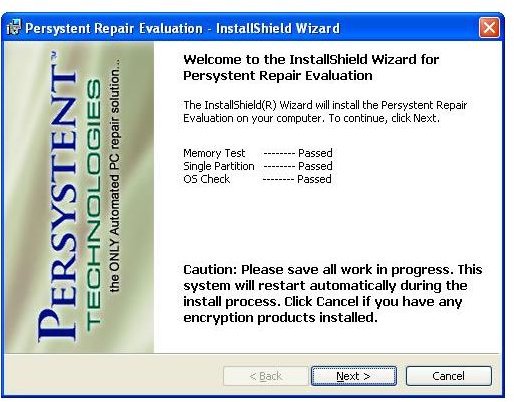
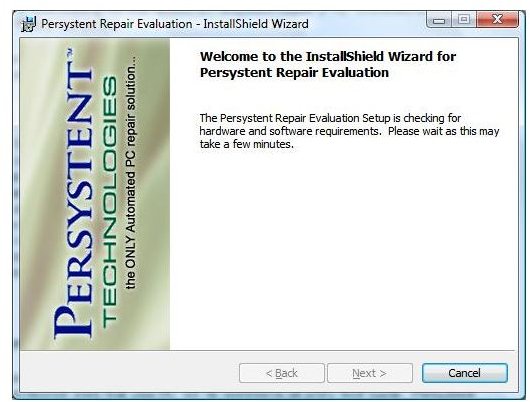
Persystent failed on my HP laptop because of a hidden restore partition. With so many computers with hidden partitions, the program should be changed to allow this. My choice after discovering this was to install the software inside of virtual machine running Windows XP Pro.
Partitioned vs. Non Partitioned Laptop
License Key
Persystent’s licensing appears to be straight forward. A key is sent and used during the installation process. This key has the extenstion .lic. The key is used for the initial installation of the software and this key insures your software will function correctly.. If you are unfamiliar with this type of installation, the software will not run without being properly licensed.
Image Creation (5 out of 5)
After installing the key, the computer was scanned by Persystant’s engine. This scan was finished within minutes and the software requested a reboot. This initial reboot was followed by a seondary reboot at which time the image was created. The image took around twenty minutes with a dual core, 2 Gb laptop. This is exceptionally quick considering the number of files I keep on my laptop. The program gave a detailed progress report on the number of files copied and files remaining. During this process, the system state and registry are backed up to ensure a complete recovery in the event of a disastrous failure.
Once this image creation is complete, you are being protected by Persystant. Given the short amount of time, this is exceptionally fast for a software to give you full protection.
Creating Image
Features and Performance (5 out of 5)
Features
The program primarily is the feature. Most features are hidden from the end user. These features are the high tech engine that checks and maintains files during the post BIOS / pre operating system loading.
Performance and Testing
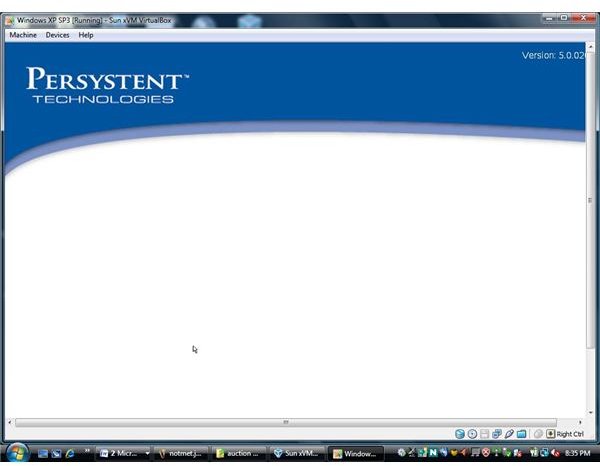
The system was tested on Windows XP Professional inside of VirtualBox. This testing is as real world as it gets considering virtualization is one fastest growing forms of information technology. The boot is delayed of course due to Persystent’s check of your operating system. This is expected and well worth the wait if you are protecting an operating system. After loading Windows XP, and deleting several files from the operating system, I rebooted only to find my system still funtional. Users are allowed to interact with Persystent and any interaction is simple and easy to use.
Viruses and Malware
I deliberately installed a virus on the test computer (Virtual computer running Windows XP Pro) and again, Persystent Repair again delivered as promise and corrected the system files that were infected. Persystent Repair is perfect for any user.
Recommendations
Persystent should also offer a customization feature where a logo could be added to the boot screen along with Persystent’s logo. This would give the ’teamwork’ branding making IT Managers and System Analyst more comfortable. Former software companies that offered some form of recovery software in the past had their logo only. The current branding with Persystent’s logo during boot gives a nervous feeling to these aforesaid IT professionals.
My final recommendation is to give a thumbs up and to recommend Persystent Repair. This software is an invaluable asset to any small business or corporation. With business continutity in today’s world being one of the most important aspects of business; this program performs as expected. Persystent delivers an excellent software that is much needed.
More Reviews!
Would you like to read more reviews? Look around Bright Hub and you’ll find reviews of numerous other leading security solutions including SpamTitan , GFI MailEssentials , Atek Secure Password Organizer , GFI LANguard , Norton Internet Security , Panda Internet Security , ESET Smart Security , McAfee Site Advisor , Norman Internet Security Suite and Undelete .


