Tenable Nessus is a powerful network security vulnerability scanner that can scan for, detect and report on over 30,000 network security vulnerabilities. This article will show you how to use Nessus to perform network vulnerability scans against your network.
Overview
Vulnerability scanning is an important task every network administrator should perform on a regular basis. Using a tool such as Tenable Nessus can make your job much easier in detecting potential network security vulnerabilities. Other useful tools – including some free network security tools can be found in my article called Free Network Security Tools .
Before you get started, make sure your machine supports the system requirements for running Nessus.
Nessus can be run on the following supported Operating Systems:
- Red Hat ES 4,5
- Fedora Core 10,11,12
- Debian 5
- FreeBSD 7
- Ubuntu 8.04, 8.10, 9.10
- Mac OS X 10.4\10.5
- Windows XP, Vista, Windows 7, Server 2003, 2008
- SuSE 9.3, 10
- Solaris 10
System Requirements
- 1GB RAM – up to 4 depending on size of network scanned
- Pentium 3 processor @ 2GHz+
- Unix: OpenSSL, zlib and GNU C Library
- Windows: Some performance issues with Windows XP SP2+
- Adobe Flash Plugin
Installing Nessus
Nessus installs as a web service and is accessible to any computer on your network via web interface, username and password. For the purposes of this article, I will install Nessus on a Windows 2003 Server.
- Go here and click the link to Obtain and activation code. Click on the ProfessionalFeed or HomeFeed option. Request an evaluation license, fill out the requested information and wait for your activation code to arrive via email.
-
Next, go to the Nessus site and download Nessus – available here . Follow the default prompts to install Nessus.
Advertisement -
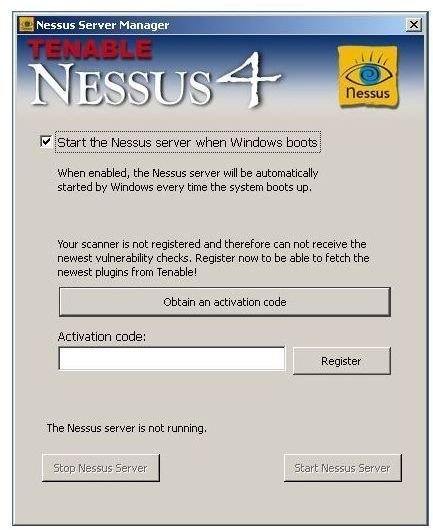
A new desktop icon should appear after the installation completes. Double click on Nessus Server Manager.
-
Nessus will ask you to enter your activation code (Figure 1). Enter the code you received in step 1 and click “Register”. Nessus will start downloading and installing the plugins that enable Nessus to perform scans. This process may take a while (30+ minutes) depending on the speed of your computer.
Advertisement -
The server manager will be left open when the plugin installation finishes. Click on the “Manage Users…” button.
-
Click the “+” button to add a new user. Enter a username and password, select the “Administrator” checkbox and click Save.
Advertisement
- You can close the window – Nessus will run as a service.
Creating a Policy
Before you can run a Nessus scan, you’ve got to create a policy. Nessus Policies track the vulnerabilities you want to scan for.
-
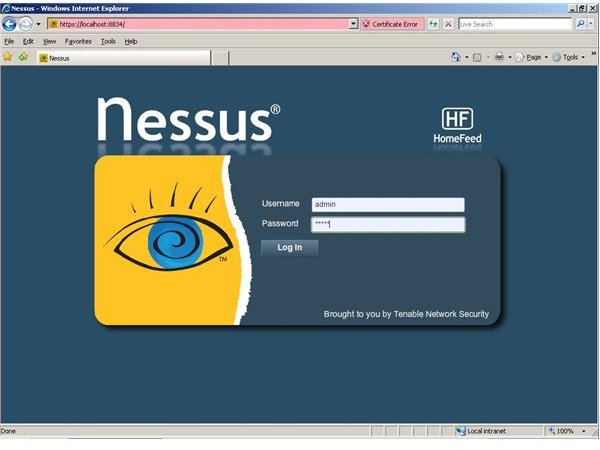
Open up the Nessus interface by browsing to https://localhost:8834 on the machine you installed Nessus (Figure 2). Enter the username and password created earlier and click Log In.
Advertisement -
Click on the Policies tab at the top of the screen.
-
Click the Add button to create a new policy.
Advertisement -
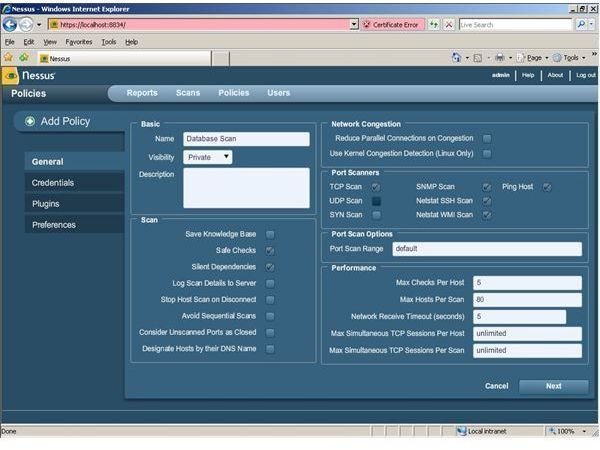
Give the scan a name and make sure “Safe Checks” and “Silent Dependencies” are checked – leave the remaining scan options the default (Figure 3). Click Next.
-
Enter credentials for the scan to use. You can use a single set of credentials or multiple sets. Click Next when you’re ready to continue.
Advertisement -
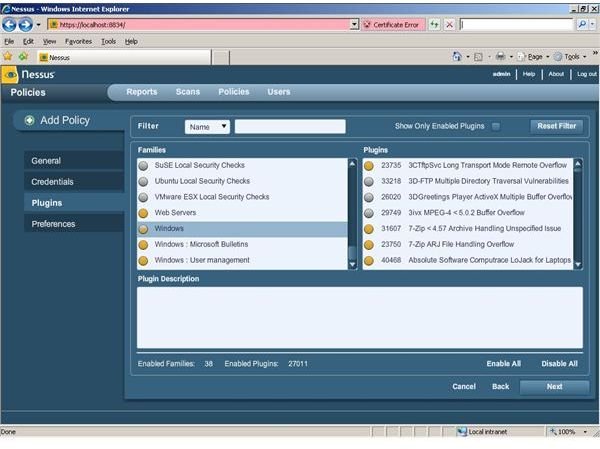
The plugins tab will let you choose which families of scans you’d like to perform. Nessus will have all plugins selected by default. Click the Yellow dot to disable any of the Families, or click on the text of the Family to see a list of individual plugins. You can also use the Enable All or Disable All buttons to help you pick the right groups of plugins (Figure 4). Click Next.
-
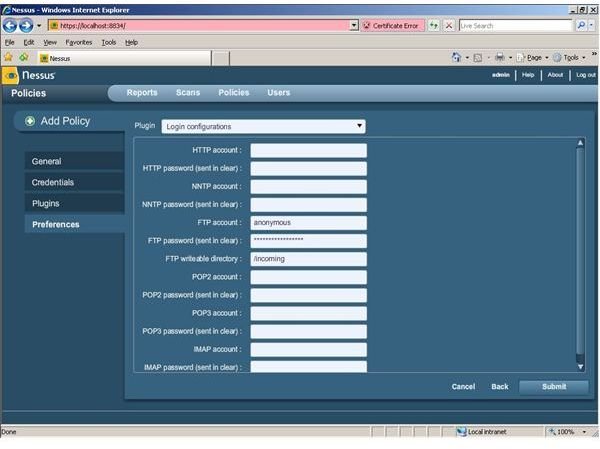
On the preferences screen, you will need to tailor the preferences to the machines you are scanning. Use the Plugin drop down box to select each plugin item and specify settings as needed. For example, if you are performing database, web or email scans, you will need to enter credentials for Nessus to use in the scanning process (Figure 5). Click Submit once finished.
Advertisement
Performing a Scan and Using the Reports
The Nessus scan is really the heart of Nessus as this process performs the vulnerability assessment against the machines you specified in your policy.
-
In Nessus, click the Scans tab and then click Add.
Advertisement -
Give the scan a name and select the policy you set up earlier.
-
In the Scan targets box, enter the list of machines you wish to scan. You can also import a list using the Targets file box. Click Launch Scan to begin the scan.
Advertisement
-
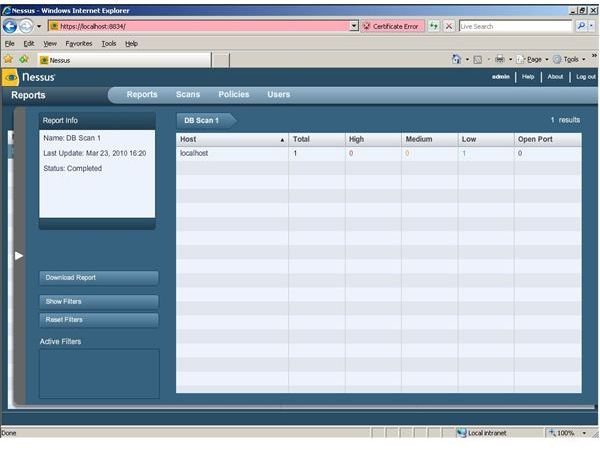
Depending on how many devices you are scanning, Nessus may take a while. When the scan is complete click on the Reports tab.
-
You will see the name of the scan you just completed. Double click on the san name to drill into the report.
-
Once in the report, you will see a listing of each host scanned along with the total number of High, Medium, Low vulnerabilities found (Figure 6).
-
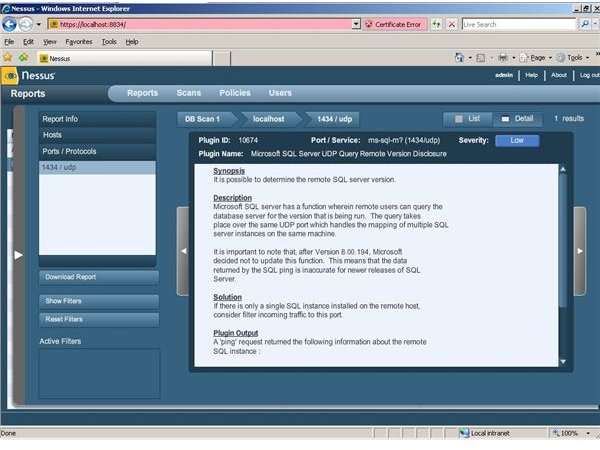
Double click on the host name to drill into a list of the vulnerabilities found. Drilling into each vulnerability and Plugin ID will give you a detailed description of the vulnerability found along with possible mitigation strategies (Figure 7).
That covers the basics of how to use Nessus. By frequently scanning your network for vulnerabilities, you’ll go a long way in protecting your network.