Nmap is one of the most flexible and effective network scanning tools out there. It’s got the speed, depth, and track record to make it my top choice for scanning utilities. Binaries for Windows are available, and even a GUI interface. Let’s take a look at how to use Nmap for scans.
What’s Nmap?
Nmap is a tool for network scanning, port mapping, and OS & application discovery. It’s a simple and flexible tool for your arsenal. Whether you want to find and identify every host on a large network, or port map and discover every application running on a single host, nmap can do it. Nmap runs on numerous platforms, and has myriad options. The output of Nmap can even be used as input for other penetration testing applications. If you haven’t used it before, it can be a bit intimidating because of the long strings of potentially complex options. Let’s look at how to begin using it.
Get Nmap
Get nmap from here: https://nmap.org/download.html
Nmap is available as source code, as binaries for Windows, binaries for Mac OS X, and RPM packages for Linux distributions. The Windows port also needs Winpcap in order to function. There is a GUI version of Nmap available for Windows, as well as the traditional command line version.
On Windows the installation includes the Nmap core files, registers the application and makes registry updates, installs WinPcap if it is needed, installs the Zenmap GUI, as well as Ncat and Ndiff components for Nmap.
On a Unix-like platform it’s as simple as the usual ./configure, make, and make install.
How Do I Use It?
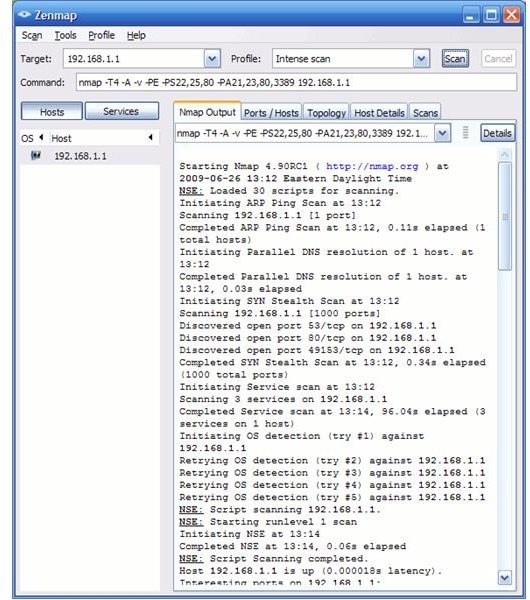
Let’s assume you’re on a Windows platform and using the Zenmap GUI. Launch Zenmap by clicking the desktop icon or the Start menu link. Here we see the startup screen for Zenmap. There are fields for the target, scan profile or type, and the nmap command line details. The rest of the window has panes for the results, with tabs providing different ways of viewing those results. There is even a network diagram view–nice!
Simply type in the address, subnet, or range of IP addresses in the target field. Choose the profile that suits the type of scan you want to run. Hit the Scan button. That’s it! After the scan completes you can click on the various tabs and items in the results to learn the details of the results. You can save the results of your scan if you like. Of course you can use the command line version of Nmap if you prefer that.
One of the neat things Nmap can do is identify the type and version of operating systems at the IP addresses on a network. This can make it very easy to identify what’s there, rather than trying to sort out what’s using each IP address manually. Updating IP address lists and diagrams is quicker when you know what’s there. It can also sometimes help find old versions of operating systems or firmware on hardware that’s out of sight.
Of course these are some of the least sexy uses of Nmap. There is excellent documentation out there and there are even some books that explain in depth how to use it. Good luck with your scans!