Access Control Lists are methods of restricting access to files or folders. ACLs are put in place to restrict access to an individual object. If an individual request permission to gain access to a specific folder or file, the ACLs that are put in to place come into play.
Access Control Lists
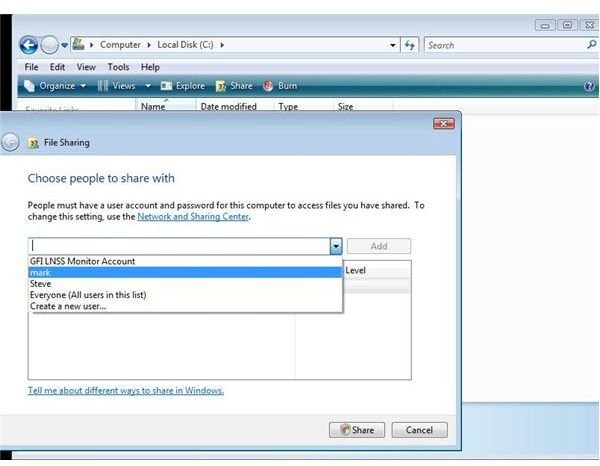
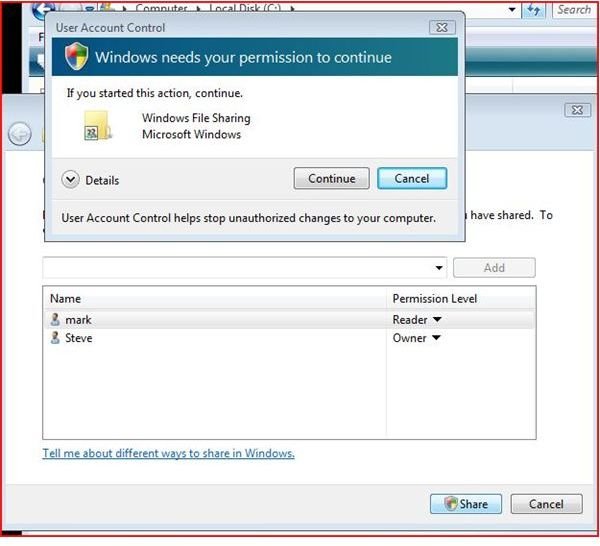
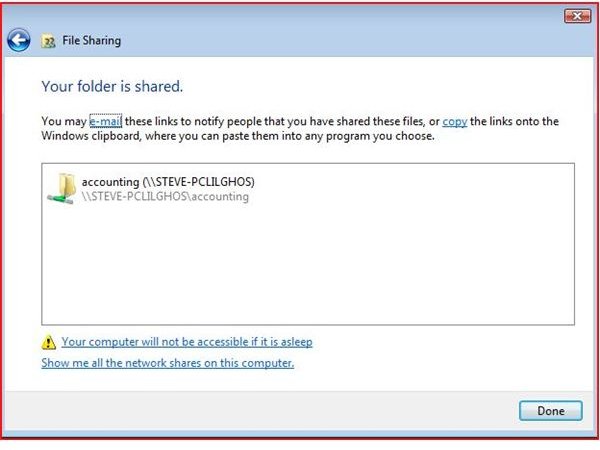
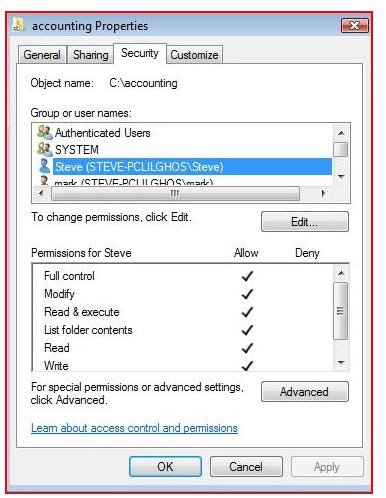
Access Control Lists known as ACLs is a set of permissions that are associated with an object such as a file or folder. (See pictures below). This list specifies who is allowed to do what to an individual folder or file. ACLs are put in place to restrict access to an individual object. If an individual request permission to gain access to a specific folder or file, the ACLs that are put in to place come into play. With ACLs, several things take place. If a file or folder is shared out to other users, a unique security identifier known as an SID for a user account is associated with the individual user. (When you create a user, the user has a unique number issued to the user.)
Images

The SID
The SID for any user account, group account or logon session is unique in itself. the security identifier associated with these aforesaid users or groups ensures that the individual gaining access has the appropriate permissions to use the folder or file. The operating system (Microsoft Windows, Macintosh or Linux) ensures that each entry in the access control list uses an access control entry or ACE for maximum security.
Because ACLs and SIDs are associated, the access mask (rights) are controlled by the access control entry. Each ACE uses flags to indicate the appropriate rights (read, execute or write - in the most simplex form).
If a folder is shared out to several users, and later a user is deleted (an employee quits or is terminated) the SID associated with that employee cannot be used again. If you recreated the employee (the employee returns to work), the folder must be reshared out (or permissions reset on the file or folder in order for the employee to regain access or use of the file or folder.
Bottomline
The bottomline is that access control list play a critical role in any computer security network. ACLs are important to use. Never share out a folder or file to the Everyone group. Everyone means just that - anyone and EVERYONE. Every job role in any organization should be carefully analyzed to see exactly who needs what access. Data Integrity and security is of the utmost importance with any organization.