Managing Security During an Economic Crisis
Economic Impact
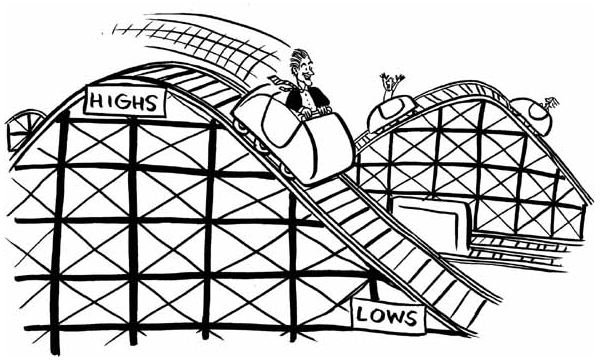
The economic impact on the security b
udgets passed out during this fiscal year can directly affect the overall future of businesses. Security often is looked at as a luxury. CIOs and IT Managers who often present security budgets at the beginning of a fiscal year find their budgets immediately approved. Knowledgeable managers know that during recessions and financial downturns that an approved budget is not a guaranteed budget.
With the economic and financial downturn, companies will begin cutting budgets and seeking other sources to manage and secure their information technology departments. Although many business executives today realize the importance of security; security often gets pushed to the bottom of a company’s overall budget.
Things to Do
Because the overall welfare of the company is priority one, it may be necessary to look at cutting or implementing the following items:
Operating System Upgrades- newer operating systems are not always necessary. With Windows XP Professional matured and stable, upgrading to Windows Vista may not be necessary. Further savings can be seen by using operating systems such as Ubuntu. Ubuntu requires very little training and with Opensource add-ons such as OpenOffice, money can be saved on applications. Implementation of this operating system on computers can in the end save money.
Database Upgrades – companies using SQL Server 2000 or SQL Server 2005 may not need to upgrade to the latest SQL.
Application Upgrades – just like operating system upgrades, applications don’t always need to be upgraded.
Personnel – if financial cuts begin to hit the information technology personnel within an organization, IT managers and CIOs can consider the restructuring of an organization by offering salaried positions to hourly employees. This restructuring can be complex and touchy. If hourly personnel are working overtime because of needs, the overtime has to be calculated for an average work week and salaries may have to be adjusted in order to keep dependable personnel and to meet the needs of your organization.
It may not be necessary to look at applications that can save your money in the future. You may have to save money now! These applications, hardware or cost savings applications need to be monitored if the ROI (Return of Investment) cannot be seen immediately.
Communication is the Key to Survival
While thought is given to what is truly needed and what can be substituted during a financial downturn; with today’s ecommerce and complex business needs security cannot be sacrificed. Executive management and the CIOs of companies need to be informed early on about the importance of security prior to the cutting of the Information Technology / Systems department. Failure to communicate the needs of maintaining security can be devastating to the security stance companies currently have. Communication needs to happen on all levels from the CIO to the entire information technology department.
Vendors and Security
IT management personnel may need to also look at vendors that supply security products and security services. The IT department has to focus on quality of service and hidden cost of outsourcing. Outsourcing is not always the answer. Because of the often late discovered hidden cost or annual increases, outsourcing to vendors can sometimes cost more than keeping services ‘in house’. Some vendor options such as Trend Micro’s Worry-Free Business Security could save money. With other major vendors in the IT business, no option should be overlooked. Caution should be used in deciding when the Return of Investment will take place.
Evaluating Hardware and Software
Information technology personnel need to evaluate their ‘high end’ items. These high end items may be items such as firewalls, ISA servers and other protection hardware or software. Often upgrades instead of the ‘latest’ model are the responsible decision to make. Firmware updates on your network along with the monitoring of service packs, patches and updates is the highest priority of managing it. Keeping security priority one is the single most important thing to think about.
Consideration has to be given to training and compatibility when implementing any open source operating systems or applications. Although Linux has Wine which allows windows applications to run on within the os, tests need to be conducted within the operating system to ensure true compatibility. Security of this open source option has to be monitored just like Microsoft products.
Regulations
Because of the upset on Wall Street, government regulations that are unseen at this time will become apparent for information technology professionals. Companies will be under a microscope because of the ethics shown by some of the larger companies that were bailed out by the U.S. government. IT departments’ roles will change because of the aforesaid crisis. These future regulations will look at compliance in areas of security and email (SOX enforcement).
Overview
Information Technology professionals should look at alternative means of upgrading hardware and software. Personnel within these departments will have to maintain network, product and ecommerce security on a shoe string budget. Regardless of the economy, security has to be prioritized as the single most important factor in a company’s budget.