Many employers have the same rules when it comes to formulating a computer security policy - make sure you know what they are!
Computer Security for New Employees…
So it’s your first day at work in your new job and you’re looking forward to getting settled in and engaging in the tasks described in your job description – but instead you find yourself sitting in a small room learning about your new employer’s computer security model.
It might sound dull, but it happens every day as new employees go through corporate induction processes, covering the usual suspects like manual handling, how to react in the event of a accident and how to use a computer responsibly.
If you have had several jobs in the past it might all seem very familiar to you, but there is nothing to be gained from ignoring or glossing over the information. All organisations have a computer security policy, and adhering to it could be vital for your job security.
Computer Security at Work
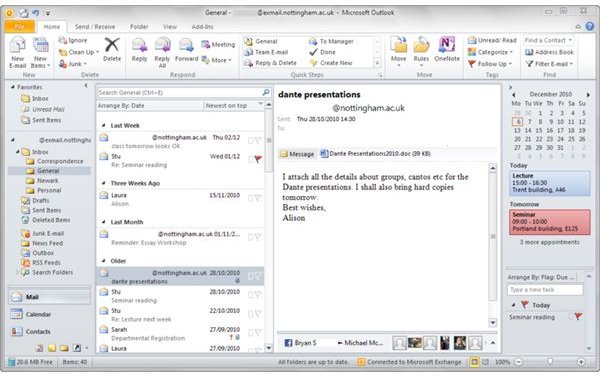
Now it’s all very well booting up a PC and logging in to begin the process of checking emails (or working out why you haven’t received any ), writing reports and editing presentations, but there will probably be a bit more to what is expected of you as a networked computer user.
For instance most organizations are particular about connecting devices to PCs. Often USB ports are disabled in order to protect systems from worms and viruses as well as to prevent the stealing of data. Users with sufficient permissions may be able to overcome this restriction.
Meanwhile you will be expected to maintain the secrecy of your password. Sharing passwords is a big no-no – regardless of the wider security implications, telling a colleague your password can lead to disciplinary actions and even if you’re not caught out, there is every chance that your colleague might misuse the account, intentionally or otherwise.
Changing Passwords and Accessing the Corporate Network
Accessing the corporate network of your employer will no doubt require a password, often combined into the same one that gives you access to your PC and email. This single sign-in method is becoming popular, but is also controlled by requesting users to change their passwords periodically, typically after 28 days.
With this level of security in place and auditing used to track your behaviour should a data breach or other security issue be traced to your PC or account, it is wise to always lock your workstation when you are away from your desk. You can set a Windows PC to automatically lock after so many minutes of inactivity, a useful feature in the corporate environment.
Using Hardware: Company Laptop Security
Naturally most hardware in your organization will be locked down in some way, with the obvious exception of laptops which are designed to be carried around.
Along with portable hard disk drives, projectors and perhaps even USB flash memory devices, your employer will probably expect anyone planning to use these devices to pre-book them as well as sign them in and out, possibly even using a barcode scanner to record the device as being physically present.
Additionally these devices will (space permitting) have security information etched into the casing, as well as some form of identification in the operating system in the event that they are lost or stolen.
Using the Internet
Most office jobs require a level of online research, although this naturally depends on your role. More and more companies are applying strict controls over the use of the Internet and in particular the web as more and more web sites offer a wider variety of services. You will probably find that sites like eBay, Facebook, YouTube, etc, as well as other media streaming sites are blocked in order to safeguard bandwidth and prevent employees from being distracted.
Meanwhile the usual warez, adult, gambling and other non-work-friendly websites will of course be blocked using popular web filtering software such as Websense.
The computer security model your employer uses is in place ultimately to safeguard the livelihood of all employees, so it is wise to stick to it.
References
Author’s own experience.
Image credit: Wikimedia Commons/MKFM