An Intranet is an internal business network that uses TCP/IP protocols and HTML just like Internet operation. The difference between an intranet and the Internet is that the intranet stops at the company’s local area network (LAN) edge, and then the Internet takes over.
Overview
Network administrators want to know what happens on their network. This is both from a machine and software perspective as well as from a user perspective. This is monitoring the network. The idea is to watch what happens so that the network can keep functioning during business or critical times.
Intranet software sits on a server. It monitors all data traffic between the Internet and the intranet. Moreover, it can monitor all traffic on the intranet itself. It works by examining every Internet Protocol (IP) packet moving in and moving out of the intranet. It examines both the IP header and the data itself. The IP header keeps track of the address, source, and destination. The data can be documents, spreadsheets, e-mail, and so on.
What should monitoring software provide the network administrator? It should provide information about who is logged on, who is sending e-mail, and who is signing in late or signing out early. It should record key strokes if necessary.
In the next few sections we will look at some top intranet monitoring software tools. These tools help IT administrators monitor the computer operations within an intranet.
For more information on intranets see: Understanding Intranet - What is an Intranet?
Spector Pro
It records email and chats (when using netmeeting software). It keeps track of web searches, files transferred, screen snapshots, websites accessed, the programs run on the computer, and even the keystrokes typed. It blocks Internet access and chats, and it provides instant notification alerts.
Source: Spector Pro
Elite Keylogger Pro 4.7
This program monitors software content from social networking sites and captures chat conversations; it also records accessed websites. However, it does not have content-filtering or website-blocking capabilities. It also does not have a keyword trigger. However, IT administrators can customize the monitoring frequency, plus the frequency of screen shots and remote reporting operations. Nevertheless, the monitoring application tracks user IDs, passwords, accessed applications, and more.
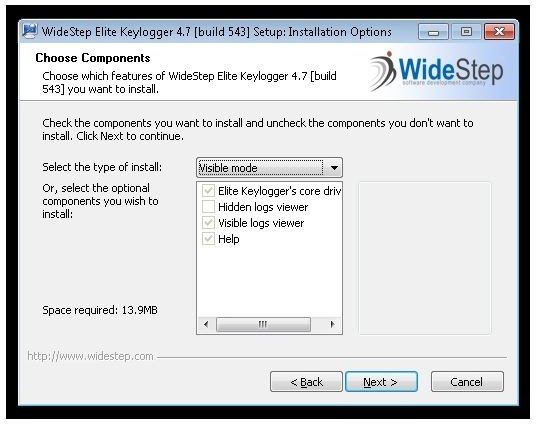
Source:WideStep
WebWatcher
The primary feature of WebWatcher is the keylogger, which captures every keyboard stroke a user makes. It has many of the features already listed with other programs: It can capture screen shots and it can record social networking traffic. It can gather information which includes typed passwords, website URLs, and user IDs. However, that is not the reason to look at this software closer than the others already reviewed.
WebWatcher allows IT administrators to monitor as many computers as they want regardless of whether or not the PC is on a network. So once you install the software, you can let it go and come back later, as it will continue to monitor and record keystrokes on the computer regardless of where it goes. If you install it on a laptop, or on a network PC, the software will continue to run.

As an intranet monitoring tool, this one has the best operations and gives full access to what users are doing on the network and on their PCs.
Source: WebWatcher
Summary
Intranet monitoring software allows IT administrators to keep tabs on the operations taking place on their network. This includes who is on the network, what the users are doing, what websites they are visiting, and who they are involved with in a social network sense. It can record the keystrokes that the user is typing to create a log of activity. These programs can provide the IT administrator with many tools for analysis and can even block user operations. In many ways, these programs are a real live firewall, with the IT admin acting as the firewall-in-chief.
See also: Monitoring System and Network Security



