Can the Computer Security Procedures of Forensic Investigations Uphold Privacy Protection?
The Need for Building Stronger Evidence against Cyber Criminals
After the March 2011 security breach that assailed the security of RSA’s SecurID, companies like Lockheed Martin, Citibank, Sony, Booz Allen, and the Oak Ridge National Laboratories were likewise attacked by cyber space criminals. The latest addition to the list is the International Monetary Fund (IMF). Although the breach in security was publicly disclosed only in June 2011, the IMF admitted that its system had been assailed several months earlier. The official who disclosed the information, however, did not provide details but described the incident as a major security breach.
Computer forensic investigators (CFI) previously encountered difficulties in pursuing their cases against cybercriminals as affected computer user-organizations are wary of exposing more of their sensitive data for use as evidence in courts. The complexity of these cases pertains to the acceptability of the hidden data left behind by hackers in the user’s operating systems when introduced as court-case evidence.
Presentation of evidence has placed CFIs in a quandary, since they are at risk of violating privacy policies by inadvertently revealing irrelevant files. As a result, the unavailability of information is being used as defense by the cybercriminals who have been identified and being investigated.
To allay the fears and anxieties over data exposure and liability for possible privacy policy violations, CFIs have furnished information about the computer security procedures to which they adhere. These policies serve as precautionary measures taken during the process of identifying, reconstructing and compiling relevant files to be presented as evidence in the courts of law without violating privacy policies. Their aim is to nurture trust between affected organizations and forensic investigators that would allow the broadening of the scope of investigations.
The objective of the forensic examiner is to come up with a disk image of the information contained in the hard drive, which includes data gathered not only from workstations but also those found in the Internet, in routers, web logs, and emails. The time, the date and the size of files that were transferred are valuable to the prosecutors as they will allow the court cases against fraudsters and hackers to flourish in the courts of law.
Gathering of Evidence at Workstation Environments
Procedural Step 1 -The forensics team will make two identical copies of the hard drive, one of which will be retained by the affected user, who will, in turn, keep the copy in a safe environment. That way, the users can reference the CFI’s prepared evidence against their copy as it was maintained in its original state. A hash signature of the stored data shall be used as proof that the user’s copy is an exact replica of the original disk and has not been tampered with.
Procedural Step 2 – Removal of all irrelevant data shall be made on the CFI’s copy only, by using a special eraser tool called “Evidence Eliminator.” The affected user is given assurance that no law is being violated, since deleted data can be retrieved from computer storage. This is not regarded as equivalent to the shredding of original documentation in a paper environment, for which the intention is to render it impossible to retrieve data considered acceptable evidence.
Procedural Step 3 – Data retained and gathered as evidence shall be limited to those that are directly associated with the investigation. In such a case, sensitive document decryption shall not be performed on data that belong to individuals who are not connected to the cyber fraud under investigation. This vital step ensures that privacy is being protected.
Procedural Step 4 – Handle all evidence gathered in the strictest confidence. This procedure takes into consideration time- and place-related information that is not directly relevant but could be revealed if certain data are presented. The irrelevant information can be constituted as a violation if this places any individual in a compromising situation that is irrelevant to the cybercrime under investigation. Examples of this type of information are the credit card purchases that furnish information regarding the time and place of transactions, which likewise denotes conclusive evidence of the whereabouts of individuals not involved or among those accused in the criminal investigation
Gathering of Evidence in a Network Environment
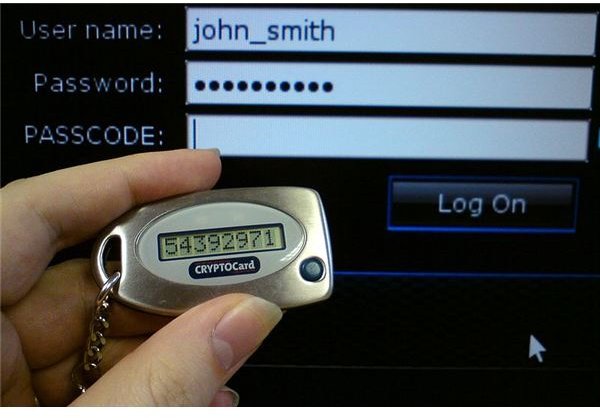
Procedural Step 5 – Use security tokens instead of IP addresses when gathering information about data routed from a point of origin to any destination inside the Net–this method protects the computer-user’s privacy rights.
Security tokens allow authorized users to gain access to network services but only for a limited time. Tokens are usually provided in the form of a “smart card” or “key fob” that requires the user’s personal identification number (PIN) before he is furnished with a special number identifier. The second set of numeric codes allows the authorized user to log in. This ensures that the data gathered from the network service are kept secured and accessible only to the authorized user by virtue of his token.
Procedural Step 6 – Ensure that all internal transaction logs are safely stored, inasmuch as transaction logs at a specific point in time in relation to the network status cannot be recreated. It is vital to the investigation that data held and presented as evidence are not corrupted.
Procedural Step 7 – Safeguard event logs only in external leaf nodes as this is vital in securing the trust and cooperation of a network service provider.
Procedural Step 8 – Maintain a track record that action performed and actionable items involved are all in accordance with organizational policy and are related to the cyber attack. As an example, if the policy calls for the restructuring of the system prior to the intrusion event, it is important for investigators to handle only the events that are consistent with the said policy. Any inconsistencies could cast doubts that would subsequently trigger investigations pertaining to privacy policy violations.
Procedural Step 9 – Institute policies and procedures for upholding the integrity and protection of back-up data related to the investigation. This procedure addresses the concern regarding misuse or abuse over stored backup data, which if not properly secured will enable unscrupulous users to extract sensitive personal information, tantamount to privacy violation.
Procedural Step 10 – Use only secure methods of disposing of all data not related to the computer attack being investigated. These data pertain to individuals that have been assessed as not connected with the crime. However, they are formatted in a way that establishes certain relationships; hence, proper disposition is a must to ensure that irrelevant information is properly deleted or destroyed. Appropriate methods of disposition or deletion will eliminate possible issues about privacy violations.
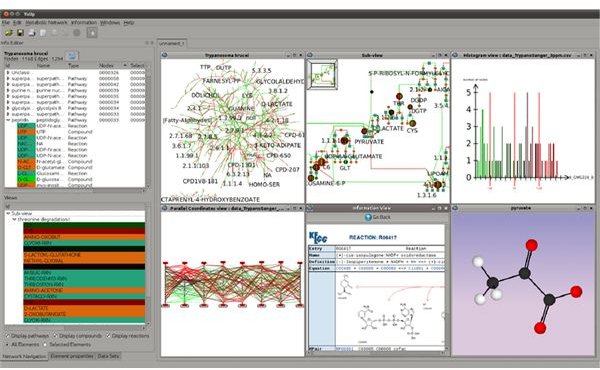
Computer Forensic Tools That Meet Privacy Policy Protection
STOP or Session Token Protocols – They are security-enhanced devices that allow the computer forensics investigators to trace hackers’ logging-in activities through a series of web hosts, as their means to hide their identities. They are accessible only on request and are permitted by using a special TCP connection and a randomly selected token number that is unique to a single session.
ILook Investigator Toolkits are funded and developed by the U.S. Internal Revenue Service (IRS) Criminal and Investigation Division Electronic Crimes Program. Said toolkit is not available to investigators as a commercial product, but is being offered as no-cost software to state and local law enforcement units in order to maintain a national standard for computer forensic investigations. It is a suite of computer applications composed of multi-threaded, Unicode-compliant forensic tools, with robust-processing capabilities to allow fast and efficient analysis of digital media.
EnCase Forensics® - A product of Guidance Software, regarded as an industry-standard computer investigation solution currently being used by private corporations, law enforcement agencies and government agencies for data collection from a wide range of devices. Its capabilities include disk level forensic analysis and reports on the findings without compromising the integrity of the data as acceptable evidence.
Forensic ToolKit (FTK 3) – A product of Access Data and also touted as an industry standard computer, this is forensic software being used by government agencies and law enforcement units on a global scale. Its digital investigations platform is accordingly court-validated based on its capabilities to deliver computer forensic analysis, decryption and password-cracking abilities. The platform is said to be customizable and scalable to allow the computer’s framework for forensic solution to expand with the organization’s growing needs.
Note: The computer security procedures enumerated above were based on research performed by S. Srinivasan, a professor of computer systems, for the security program development at the University of Louisiana, which was supported by a grant from the National Science Foundation.
Reference Materials and Image Credit Section:
References:
- By.Srinivasan,S. ISACA.org JOnline: Security and Privacy vs. Computer Forensics Capabilities – https://www.isaca.org/Journal/Past-Issues/2007/Volume-4/Pages/JOnline-Security-and-Privacy-vs-Computer-Forensics-Capabilities.aspx
- ILook Investigator Computer Forensics Software - ILook Investigator Overview –https://www.ilook-forensics.org/
- EnCase® Forensic - Guidance Software - https://www.guidancesoftware.com/forensic.htm#tab=0
- Forensic Toolkit 3 Industry Standard Computer Forensic Software - Access Data – https://accessdata.com/products/computer-forensics/ftk
Image Credit:
- By United States Federal Bureau of Investigation / Wikimedia Commons
- By SupremeDalek / Wikimedia Commons
- By Jonathan Dubois / Wikimedia Commons
- By Brian Ronald / Wikimedia Commons
