Ever received feedback that your business has been SMiSHed? How does SMiSHing weaken your enterprise security measures, and what can be done to stop it? We’ll cover these questions and more with tips to help prevent your business from becoming a SMiSHing victim.
SMS Phishing
SMiSHing is another term for SMS Phishing—a type of phishing attack that is received through a mobile phone as an SMS message. The message may contain a link to a website and ask customers to verify their accounts, unsubscribe or subscribe to a service, or activate their memberships.
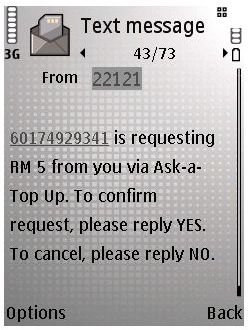
Some SMS-based phishing attacks do not contain website links in the message, but do include a phone number for the recipient to call to activate or provide information requested from automated prompts. The SMS phishing message may also contain nothing but a text message, and the potential victim is instructed to reply to the message with a yes or no text message in response.
How Can SMiSHing Harm Legitimate Businesses?
Phishing, as we know, is a form of criminal activity. If a business name is used by a fraudster, the company or business name may become unpopular to potential customers. That is, if the company being targeted by phishers does not take action to clarify that their business is not involved and associated with recent phishing attacks, customers may lose faith or even blame the business for the phisher’s actions.
Below are examples of SMiSHing attacks that I have received over the past few weeks:
The above message is from a service number. If I respond to the message with a “Yes”, my account will be credited for the amount requested by the SMiSHer. Here’s another example of a fake service message via SMS that contains a link to download a file which is infected:

Below is yet another example of SMiShing that I received. This one used a company name “Power Root Sdn.” (Sdn is an abbreviation for Sendirian Berhad, which means “private business” in the Malaysian language) in the message. The company Power Root may or may not exist, but the message announces that I won 20K and should call the provided number to claim the prize.
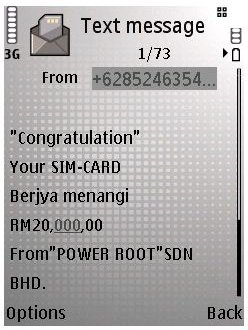
People who respond to the message or call the provided number will be prompted to provide their credit card number, mother’s maiden name, birthday and other personal information , allowing the phishers to gain access to their accounts.
People who have not heard of SMiSHing might fall into the trap of revealing their identity or giving out private information such as credit card numbers, social security numbers, and other personal data. If the victim realizes that they are being phished via SMS messages, they might blame the other victim—the business or company being used by the fraudsters. The customers will become unsatisfied because the company did not alert them of potential fraud or scam messages using their business name. In some cases, the unsuspecting customer might expect that something good actually happened, e.g. winning money from the company that supposedly hosted a contest. They will try to claim the amount they’ve won. The company will now have to deal with the customer and explain their business is not associated with the fake SMS message.
How Can You Stop SMiSHing?
A company or business should be aware of the current online and offline threats that their customers or their own company might face. Prevention is better than a cure, which is why it’s recommended to stay updated on all scams that are being perpetrated. If companies A and B are victims of phishing, then companies C, D and E could be next.
To stop SMiShing from using your business or company name, you should start creating security policies. An example policy to create and implement is to filter messages sent and received by your company. There are security software vendors that provide anti-spam and anti-phishing protections e.g. Trend Micro and Symantec . If your business sends an automated message to customers, but you are using managed security protection, then malware, security issues, vulnerable platforms and applications will be prevented. And, if your business system is free from any security issue, a fake SMS or phishing attempt will not be sent by your automated service messaging system.
Keep Your Customers’ Data Private
Phishers or spammers target a company or person for private data. Any information that was leaked (intentionally or unintentionally) is what they want. Apply the fixes and restrictions to ensure that all information will never be leaked and immediately respond to any report by customers to prevent another victim.
Use Verification Services
If your company is using mobile system messaging or providing mobile services to customers, ensure that there is some verification system, e.g. mobile transaction authentication code (TAC), in addition to the account PIN code.