How are fraudsters able to convince Internet users to revealing personal information? Is there a way to prevent these attacks? This article will guide you on how to avoid phishing attempts.
Phishing is a way to trick computer and Internet users into revealing personal and financial information through a fraudulent email or website. The content of a phishing e-mail usually looks like an official notice from a bank, credit card issuer or trusted online merchant. In the email message, computer users are directed to a fraudulent website where they are asked to provide personal details, such as thei username, account number or password. Some email messages will ask the recipient of the email to respond to the message with personal information, such as their birthday, email or postal address, full name, credit card number and so on. Anyone who responds to the email or enters their personal information on the fraudulent website is a victim of a phishing attempt. The personal information gathered by phishers is usually used for identity theft.
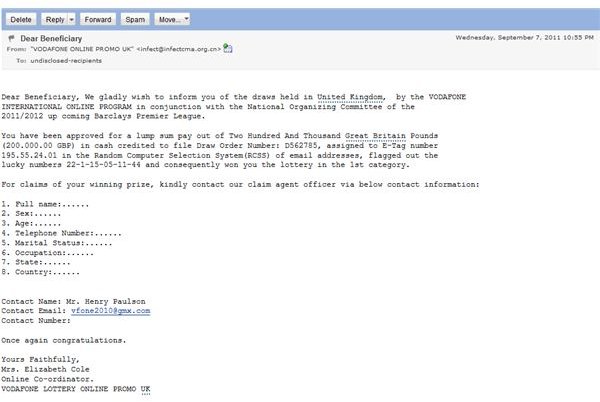
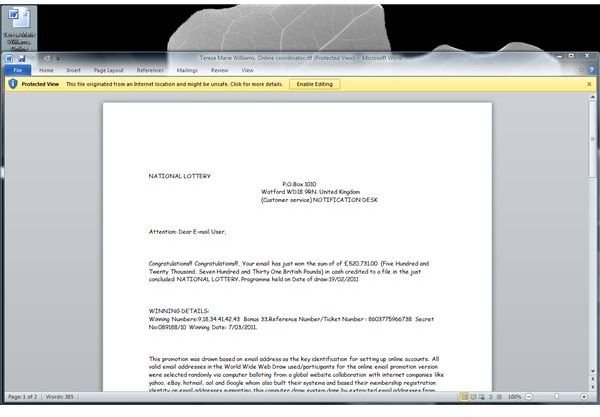
Scammers will also try to use the name of popular services or products to trick people in providing personal information, such as web-based email and social networking services, government or hospital services for example. Some fraudsters will even use phishing e-mail message to trick computer users in downloading or installing malicious software, such as fake antivirus and rogue anti-spyware programs.
There are plenty of tools that can help protect from phishing scams. Most browsers and e-mail programs provide anti-phishing protection. It’s recommended to double-check the status of the fraud and malware protection feature in browsers and e-mail clients to block the loading of fraudulent websites and blocking the images and links of the email message.
Below are some great articles, tips and user’s guide to prevent phishing attempts. In these articles you’ll learn about the dangers of phishing and common phishing techniques.
What is It All About?
Learn how phishing started and what the dangers are when you mistakenly provide your personal and financial information to fraudsters.
- The History and Future of Phishing
- What Does a Phishing Scam Look Like
- Why is Phishing so Dangerous?
- What is Vishing Scam?
- How Spear Phishing Works
- Why Smart People Fall for Scams
- Effects of Phishing Scams on You and Your Personal Data
- Phishing Statistics: Who Are the Primary Targets
Attacks
In the linked articles below you find true stories and examples of phishing attacks or attempts that Bright Hub experts and writers have
gathered or experienced. You’ll also learn why these services are being used by phishers to trick Internet users into revealing personal information.
- Phishing Scams - Top Threats
- Beware of IRS Phishing Scams During Tax Season
- Facebook Phishing - The Tactics
- How to Avoid PayPal Phishing Scams
- How to Avoid Car Warranty Phishing
- Phishing with TinyURL.com Links
- Image Gallery of Phished E-mails and Websites
Avoidance
Education is the best solution to prevent security incidents. Find here our articles that describe several methods on how to practice safe computing. It’s recommended to educate computer users at home and at work to prevent security incidents caused by phishers.
- How You Can Avoid Phishing Scams
- Train Employees on Anti-Phishing with Anti-Phishing Phil
- How to Stop SMiShing From Harming Your Business
- Best Practices to Prevent Phishing
Prevention
To fight phishing e-mails and links to bogus websites many software vendors have added security features to their programs to protect users from fraudsters. Take advantage of the security features offered in browsers and email programs. You can also use anti-phishing tools as an extra layer of protection.
- Using the Phishing Filter in Internet Explorer
- Phishing Protection and Phishing Tools
- How to Block Phishing Message Using Windows Live Mail
- Use OpenDNS To Improve Your Security
- How to Block Pharmacy Spam Using Outlook
- Phishme Review, The Easy Way to Enhance Employee Phishing Awareness
Protection
Below are some of the Internet security programs that provide anti-phishing protection to home and office computers. The phishing protection module should actually be part of every security software, freeware or not. You should check the documentation of the antivirus program on your computer and make sure that its anti-phishing feature is enabled. Remember that web-filtering can also be used as well to block phishing websites.
- Avast Internet Security
- AVG Internet Security
- Avira Premium Security Suite
- BitDefender Internet Security
- Kaspersky Internet Security
- Norton Internet Security
- Top Parental Control Programs for Windows and Mac OS
Reporting Fraudulent E-mails and Websites
Did you receive an e-mail message that looks like a phishing email? Have you seen a website that does not nothing but scam people? You can help the community of Internet users by reporting scammer’s dirty work!
References
- Image credit: Screenshots generated by the author.