Who says computer training should be boring? Certainly not Phil of Anti-Phishing Phil, a game that teaches employees how to recognize and dodge phishing scams. Does this game really work?
If your network contains all the standard security precautions, outsiders hacking into your network isn’t the problem. As the famous quotation from the comic strip Pogo says, “We’ve met the enemy, he is us.”
Techies and security experts have a technical term to describe the action of attempting to con a person into revealing confidential information – social engineering. This isn’t limited to the user taking action on a computer network. A delivery person could walk in and access company confidential information or someone could call a user claiming to be tech support and request the user’s sign in information.
The most effective tool in battling the effects of social engineering is education. This especially applies to phishing scams because phishers count on users to give away information without bothering to check the site or source’s credentials.
Enter training programs like Anti-Phishing Phil. These programs aim to educate employees about phishing and what to do to avoid being hooked into the scam.
Meet Anti-Phishing Phil
Anti-Phishing Phil takes a different and much-needed approach to user education – through a game. How many business courses have you taken that were fun and engaging?
The game has impressive backing as its developers include members of Carnegie Mellon University Usable Privacy and Security Laboratory, with funding from the US National Science Foundation (Cyber Trust initiative) and ARO/CyLab.
Wombat Security Technologies is commercializing the game. The company can customize Phil to integrate a company’s name, URL and brand. The game’s claim is that it only takes 10 minutes for employees and customers to learn the basics of recognizing phishing attacks with Phil’s help. Companies can deploy Phil on the intranet.
The game requires running on any web browser with Flash 8 installed. It also works in Flash 9 in Firefox, and usually Internet Explorer 7. If the game doesn’t work right with IE7, upgrade Flash.
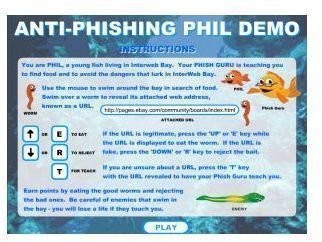
How to Play the Anti-Phishing Game
You play Phil, a young fish swimming in Interweb Bay. Phish Guru (or Father, depending which edition you play) teaches you how to find food and duck dangers around InterWeb Bay. Use the mouse to move around the bay hunting for worms to eat. Before you can eat the worm, you must decide whether to eat it or reject it based on its URL. Press “E” to eat or “R” to reject.
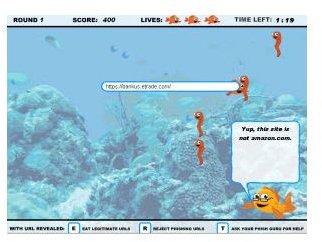
You earn points for eating healthy worms and avoiding the bad ones. If you’re not sure about a URL, press the “T” key so Phish Guru will teach you. The site uses URLs of well-known sites such as eBay, Amazon, National Geographic, banks, and so on. Of course, a URL isn’t always a simple as www.nationalgeographic.com – it could be www3.nationalgeographic.com (it’s edible).
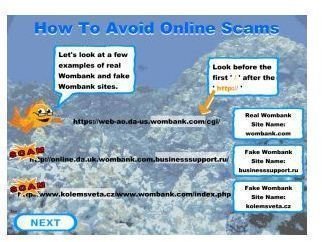
After finishing round one, Phish Guru teaches a lesson. Lessons cover URLs having several parts and whether Wombankonline.com and wombank.com are legitimate. Plenty of valid URLs go beyond the www.url.com address or use a variation like the Wombank example. These lessons show how you can figure out which one is legitimate – if not both.
Anti-Phishing Phil Game Screen Shots

Usability (4 out of 5)
Anti-Phishing Phil’s controls work smoothly. You use the mouse to move Phil. Take him to a worm to see its URL and decide whether to Eat, Reject or Teach. Sharks and eels will occasionally swim along to get in Phil’s way. They don’t teach anything, but instead make the game more challenging.
Some users may wish they could move Phil around with the keyboard, which isn’t an option.
Graphics Quality (4 out of 5)
The game’s graphics get the job done. They could be sharper and higher quality considering the sueprb quality found in today’s games. The graphics don’t impede with playing the game or the learning process.
The Verdict (4 out of 5)
Some URLs require you to switch out from the game to do a search. This teaches you how to determine if wombankonline.com or wombank.com are valid.
Even with the browser window completely open, the entire game’s screen doesn’t appear without a little scrolling. Nonetheless, it won’t interfere with the game and instructions.
Users can quickly grasp the concept of phishing and how to avoid phishing scams within 10 or 15 minutes without falling asleep. The demo lets you play a couple of rounds to get a feel for Phil. Anti-Phishing Phil does its job while keeping the user’s attention without spending much time. Sounds like a sound investment for a business. To get pricing information, contact Wombat Security Technologies.


