Over time, all Windows-based computers accumulate services, drivers, and other applications that load at boot up or on logon. Some just slow down the system while others might perform more insidious tasks. Understanding what exists, what’s new, and what should go is often tedious. Enter Autoruns.
The Challenge
Normal use of systems on which users have local administrator access inevitably results in an accumulation of services, drivers, and other long forgotten applications running at startup. They slow system performance and make restarting an older system a tortuous event. And these are just the non-malicious apps.
In addition to applications your user wanted to install are unwanted applications that slithered in through your firewalls, intrusion detection/prevention systems, and other defensive controls, often assisted by the user. And although AV software ostensibly removes them, sometimes auto-run remnants remain, including components intended to reinfect the system.
On some systems, there can be hundreds of startup applications, sucking up processor and memory resources. Finding them all is a daunting task, but Autoruns can help.
Autoruns and AutorunsSC
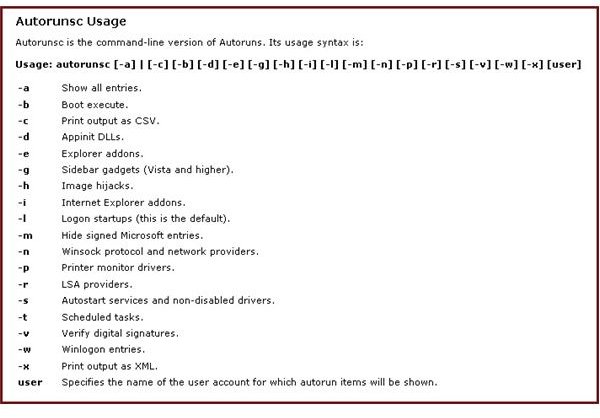
Autoruns is a Microsoft Sysinternals utility, free for download . It uses a GUI to provide deep inspection of startup applications referenced in Startup and various locations in the registry. AutorunsSC provides similar capabilities from the command line, with the command line parameters listed in Figure 1.
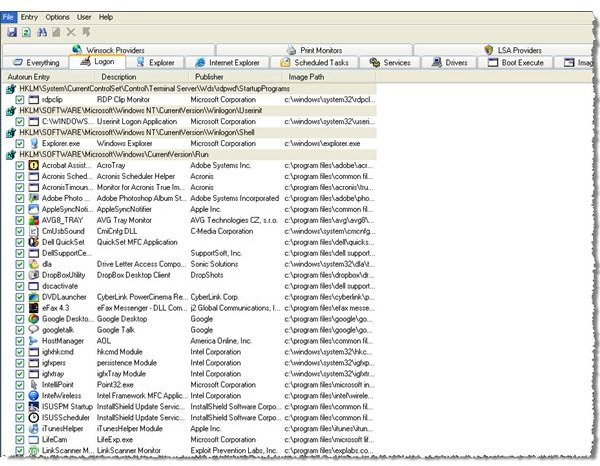
When Autoruns is executed, it immediately lists all applications that load at power up or logon. You can select a set of executables to view by clicking on the appropriate tab at the top of the display window. For example, Figure 2 shows applications from a test machine that load at logon as well as many of the available filtering tabs. One of the more useful features is the ability to filter out all Microsoft Windows components so you can focus on post system install additions.
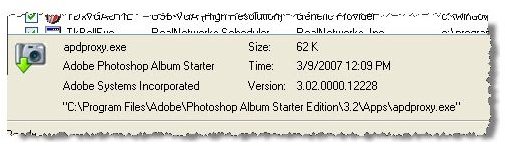
When you find a suspicious application, you can get information about it in several ways. One way is to examine the application description box that appears when you click on the app, as shown in Figure 3. If this doesn’t provide enough helpful information, you can select a Web search, bringing up the results of a Google search for the application.
There are two ways to prevent an application from loading. First, you can uncheck the check box at the left of the application name. This allows re-enabling startup execution if you later find you broke something. Second, you can delete the application. This is not recommended unless you’re sure you no longer need it.
I tested the uncheck-the-box approach by removing the check marks from four applications I knew I no longer needed. When I rebooted my system, they did not reload.
Another use for Autoruns is checking for newly installed applications. Autoruns allows you to save a copy of the current startup list and compare it to a future list. This is useful when a user complains of system slowness or when you suspect something malicious has found its way onto the computer.
This is a very useful tool. One that every system administrator and engineer should have in his or her toolkit.
Tables and Figures (Hover for caption, click to enlarge)
This post is part of the series: Use SysInternals security utilities to manage network and system security
SysInternals provides free security utilities for managing Microsoft Windows networks and systems. Available for download from Microsoft, they provide a powerful set of applications for oversight and protection of network assets.
- Validate System Access with AccessChk
- Streamline Kiosk Operation with Auto-logon
- Enumerate Windows File and Folder Access with AccessEnum
- LogonSessions and PsLoggedOn to Oversee and Manage System Access
- Use Autoruns to Improve Performance and Identify Malware
- Manage, Monitor, and Kill Windows Processes with Process Explorer
- PSExec: Free Security Testing and System Management Tool
- PsLogList: Free Utility to Parse and Review Windows Logs
- Map System Configs with PsInfo
- Use SigCheck to Validate System Files