In this section, I’ll step through—at a high level—four common U.S. regulations which affect what controls you’ll design into your network. We’ll end with a short converstaiton about the PCI DSS, which forms the basis for the remaining sections of this manual.
In the previous sections covering security planning, we looked at understanding the business and the information it stores, processes, and shares. In this section, I’ll step through—at a high level—four common U.S. regulations which affect what controls you’ll design into your network. We’ll end the section with a short conversation about the PCI Data Security Standard, which forms the basis for the remaining sections of this manual.
HIPAA
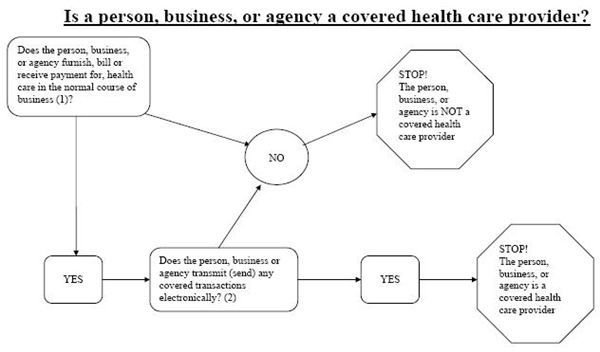
The HIPAA (Health Insurance Portability and Accountability Act of 1996) is a Federal law regulating privacy of individual health information. A sample chart from the Department of Health and Human Services (DHHS), the agency responsible for HIPAA enforcement, shows if your business is a “covered entity,” an entity which must adhere to HIPAA standards and guidelines.
In general, you’re a covered entity if you meet one of the following criteria:
- You are a health care provider that conducts certain transactions in electronic form
- You are a health care clearinghouse
- You are a health plan.
The HIPAA seeks to protect individual privacy by regulating both the release of non-electronic and electronic Protected Health Information (PHI). PHI is defined as,
“Individually identifiable health information” is information, including demographic data, that relates to
-
- the individual’s past, present or future physical or mental health or condition,
- the provision of health care to the individual, or
- the past, present, or future payment for the provision of health care to the individual,
and that identifies the individual or for which there is a reasonable basis to believe can be used to identify the individual. Individually identifiable health information includes many common identifiers (e.g., name, address, birth date, Social Security Number) (Summary of the HIPAA Privacy Rule , DHHS, 2003).
Standards and guidelines for compliance fall into one of two rules: the Privacy Rule and the Security Rule. They clearly define what is expected of covered entities to protect the confidentiality, integrity, and availability of PHI. If you’re a covered entity, NIST SP 800-66 is a good resource for understanding required information security controls.
SOX
The Sarbanes-Oxley Act of 2002 (SOX) is a Federal law regulating accuracy of financial reporting for publicly traded business entities. Unlike the HIPAA, SOX is primarily concerned with protected the integrity of financial data. It’s difficult to pin down exactly what is and is not required under SOX. Information services security audits are based on a small section of the act.
SEC. 404. MANAGEMENT «NOTE: 15 USC 7262.» ASSESSMENT OF INTERNAL CONTROLS.
(a) Rules Required.–The Commission shall prescribe rules requiring each annual report required by section 13(a) or 15(d) of the Securities Exchange Act of 1934 (15 U.S.C. 78m or 78o(d)) to contain an internal control report, which shall–
(1) state the responsibility of management for establishing and maintaining an adequate internal control structure and procedures for financial reporting; and
(2) contain an assessment, as of the end of the most recent fiscal year of the issuer, of the effectiveness of the internal control structure and procedures of the issue for financial reporting.
Based on Section 404(a), independent auditors use a variety of COBiT guidelines to audit financial security controls.
Gramm-Leach-Bliley Act of 1999
The Gramm-Leach-Bliley Act (GLBA) is another U.S. Federal law, which covers financial institutions. It consists of three main components: the Financial Privacy Rule, the Safeguards Rule, and Pretexting (social engineering) Protection. The Financial Privacy Rule requires a financial institution to notify a new customer of its privacy policy. The privacy policy notification must be repeated annually. The content of the policy must contain information about what information about the customer is collected, where it’s stored, how it’s used, and how it’s protected. Customers must also be offered the opportunity to opt out of any sharing of their information with unaffiliated organizations or individuals. The Safeguards Rule mandates a written information security plan. The plan must include the financial institution’s strategy for protecting confidential information, including:
- Denoting at least one employee to manage the safeguards,
- Constructing a thorough [risk assessment] on each department handling the nonpublic information,
- Develop, monitor, and test a program to secure the information, and
- Change the safeguards as needed with the changes in how information is collected, stored, and used.
Source: Gramm-Leach-Bliley Act. (2008, November 2). In Wikipedia, The Free Encyclopedia. Retrieved November 6, 2008, from https://en.wikipedia.org/w/index.php?title=Gramm-Leach-Bliley_Act&oldid=249121099
Pretexting , also known as social engineering, involves an attacker attempting to obtain access to sensitive information by pretending to be someone he or she is not. Social engineers use various means to obtain access information, including phishing, account holder impersonation, phone calls, or mail. Not only are financial institutions required to protect information they collect. They are also responsible for recognizing and responding to attempted identity theft.
FACTA
Completing our look at Federal laws governing information security is an examination of the U.S. Fair and Accurate Credit Transaction Act of 2003 (FACTA). FACTA places the burden of identity verification and identity theft response on U.S. businesses. The core of FACTA is the list of red flags and expected responses, known as the Red Flags Rule . FACTA requirements primarily focus on hiring, billing, and health care delivery processes. If network security is set up according to the recommendations found in this manual, FACTA network security requirements should be easily met.
PCI DSS
PCI DSS (Payment Card Industry Data Security Standard) is not a law. It’s a set of standards agreed upon by the credit card industry. Sanctions include revocation by member payment card organizations (e.g., Visa, MasterCard) of an organization’s ability to accept credit cards in payment for products or services. Most, if not all, SMBs are affected by PCI DSS. According to the PCI Security Standards Council,
All merchants, whether small or large, need to be PCI compliant. The payment brands have collectively adopted PCI DSS as the requirement for organizations that process, store or transmit payment cardholder data.
Source: PCI SSC FAQ
The PCI DSS does not mandate unreasonable, unattainable network security. For some organizations, the defined standards might not be strong enough to protect all types of sensitive information. So even though I use the PCI DSS as the basis for the rest of this manual, I’ll add recommendations for stronger controls where appropriate.
The final word
In this section, we looked at five legislative or industry mandates for protecting consumer/patient identities. The controls necessary to comply are applicable to all types of sensitive information, including intellectual property. Rather than look as these standards as interference in how you manage your business, see them as a bar to be reached. A bar that reflects reasonable and appropriate protection of business, employee, investor, and customer interests—and it’s the right thing to do.
This post is part of the series: A Security Manual for Small/Medium Businesses
A how-to manual for implementing reasonable and appropriate security in small/medium business, using clear, non-technical explanations of how to integrate emerging standards (PCI DSS, HIPAA, etc.) into security spending decisions.
- Introduction to SMB Security
- Security Planning: Data ownership and classification
- Security Planning: Data Storage and Sharing
- Security Planning: Regulatory Considerations
- Endpoint hardening and defense: Overview of layered security
- Protecting desktop computers
- Protecting laptop computers
- Choose Encryption Wisely
- Designing Network Security
- Locking Down the Network With Access Controls