While the Internet offers a wealth of knowledge, it also holds many hidden dangers. With the help of these guides you can teach yourself how to stay safe when using the Internet. Learn the types of threats that exist so that you can browse without fear.
Types of Threats and Protection Levels
Securing a computer and its network depends on the type of users at the home or office. For example, if it’s a family computer, where a child or children use the Internet, you should be protecting them from inappropriate content and rogue contacts. This does not mean that you can go easy on Internet security if children aren’t around. Some seemingly fine content can hide nasty scams, tricks and malware.
The guides in this article will keep you aware of different type of threats, tell you about protection tools to use and how you can stay safe online.
Malware Protection
Malware, as you may already know, is a shortened name for malicious software. This type of threat can be distributed in many ways, such as an email attachment, unsafe downloads from websites, file transfers in instant messengers or Internet relay chat (IRC) client software, compromised websites and social networking services.
The software we need to protect against malware are anti-virus and anti-malware programs. You can choose to use cloud-based anti-virus or traditional anti-virus software, but ensure that the on-access, or what other calls as “real-time protection,” is enabled. Some free anti-malware software programs do not include real-time protection, so it is best to check the key features before you start using your Internet connection to download files or click on hyperlinks in webpages and email messages. It’s also better to use an advanced antivirus program that will protect you and your computer from exploits that most attackers will use to spread zero-day malware. Below, you will find a selection of reviews and comparisons to make the choice easier.
Another thing to consider in choosing malware protection program is the operating system that your computer has. Are you using Windows Home Server (WHS), Windows 7 or a mobile operating system?
- Anti-virus Programs for Windows 7
- AVG vs. AntiVir vs. Avast!
- Review of Panda Cloud Anti-virus
- Kaspersky Mobile Security Review
- Eset Mobile Security for Symbian and Windows Mobile
- Microsoft Security Essentials 2.0 Review
- Anti-virus Programs for Windows Home Server
Keeping the Network in Stealth Mode
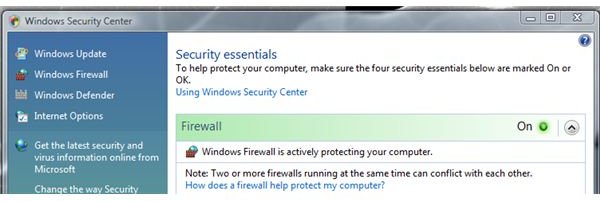
Firewall protection is a must for any type of computer, whether it’s a Mac, Linux or Windows system. It will protect the computer and the network from being seen by attackers. It can also protect against known and unknown trojans that will try to download and install malicious software without the user’s consent. Advanced firewall programs can also help to determine which applications on the computer will call home, without the user’s knowledge. Learn what firewall software (or hardware) to use and find out if your computer is leaking data.
- What You Need To Know About Firewall Leak Tests
- Top Free Firewalls for Windows 7
- Using Windows 7 Firewall
- Best Firewall: Software or Hardware?
Protecting Your Privacy
Identity theft is one very important threat to protect against. People can lose money, take a hit to their credit score or suffer embarrassment from friends and business contacts if their private information has been stolen or used by attackers. This type of threat should be protected using the following software or services, or by following the tips listed below for keeping your private information safe:
- Checking the Strength of Your Passwords
- Configuring Password Policies in Windows
- Top Password Managers for the iPhone
- Identity Theft Protection Using KeyScrambler Premium
- The Best Free Encryption Software for Mac and Windows
Avoiding Scams
Fraudsters are another type of attacker that you need to avoid and protect yourself against. Phishing and SMiShing is seen often by people who use email, browse the Internet, use an online chat system or receive short messages (SMS) using their mobile phone, personal or office computers. These fake messages are also distributed in popular social networks, such as Twitter and Facebook.
- Who’s After Your Information - Understanding Phishing Data
- Stop SMiShing From Harming Your Business
- Phishing Attacks and Phishing Techniques
- How to Spot a Phishing Scam
- Facebook Phishing - The Tactics
- Phishing Protection and Phishing Tools
- Phishing Versus Spoofing
Patch Management

Malware and other types of malicious attacks on networks and computers will be very successful if the computer is not protected against known vulnerabilities and exploits. Software vendors such as Apple, Google, Microsoft, Adobe and others help protect end-users by releasing software and security updates. It’s important to keep your computer up-to-date because no anti-virus will provide 100% protection if the computer is missing security or critical systems updates.
- Keeping Windows Secure and Updated using Windows Update
- How to Check for Windows Updates
- How to Set Up Mac OS X Updates
- Get Software Updates for Your Mac
References
- Image credit: Screenshots generated by the author