Wireless networks have become crucial to almost any business. Here we’ll take a closer look at their importance.
Wireless Connectivity
In recent years, mobile devices have become a large percentage of the end user devices used by workers to perform day-to-day tasks. These devices include Personal Digital Assistants (PDA’s) and laptops. When a traveling user visits a satellite facility, or even the corporate office, it isn’t very convenient to pull out a network cable, find a network connection under or behind someone’s desk, and perform the gymnastics necessary to physically connect to the network. Users taking their laptops to conference rooms or into plant or warehouse environments often find there is insufficient network access. The cost of running network cable to every location where access is required can be rather high. Add to these issues the proliferation of technologies such as wireless voice over IP, radio frequency identification devices, wireless manufacturing devices, etc. and the significant improvements in productivity usually more than make up for the cost of a wireless LAN rollout.
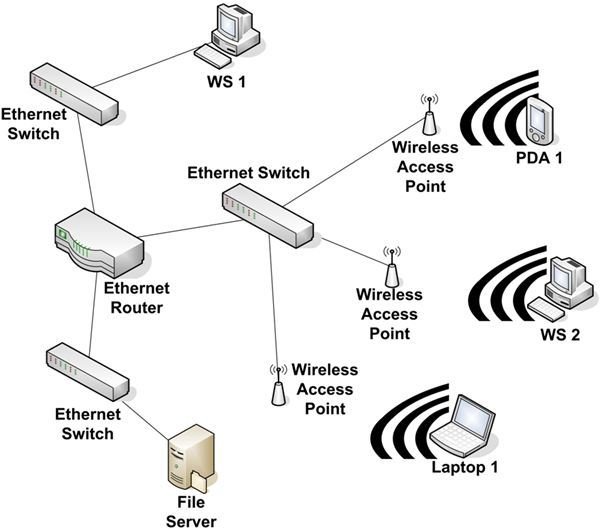
The image to the left shows an Ethernet network with wireless access points. An access point (AP) contains a radio receiver/transmitter to communicate with wireless end user devices. It’s typically attached to a network via a network cable. In this example, the AP’s are connected to a standard Ethernet switch with TP cable. An end user device must have a wireless NIC installed to connect to an AP. The NIC and the AP must support the same wireless protocols. (See IEEE Wireless Protocol Standards at the end of this article.)
The average real-world range on a business class AP is between 150 and 200 feet. Quality of connectivity and maximum range are affected by environmental conditions. These conditions can include large metallic objects, electromagnetic interference (EMI) produced by machinery, or building materials.
The downside to this is wireless connections create difficult security challenges.
Series Conclusion
We stepped through building a network from a peer-to-peer configuration to a routed network with WAN connectivity. We saw how the management of broadcast and collision domains can improve performance. You should also understand at an elementary level how information moves through a network.
At the beginning of this series I wrote this is a basic view of networking. What I’ve tried to do is provide a basic understanding of how various components work together to create a network. It’s through the proper implementation of these and other components - as well as policies, processes, physical security, and training - that you begin to protect your information assets.
If you find yourself wanting to learn more about networking, I recommend you pick up a book intended as a study guide for the CompTIA Network+ exam. I’m not necessarily suggesting you take the exam, but reading the material relevant to the exam will provide you with a solid understanding of network principles.
IEEE Wireless Protocol Standards
802.11b - Supports up to 11 Mbps over the 2.4 GHz band.
802.11g - Supports up to 54 Mbps over the 2.4 GHz band.
802.11a - Supports up to 54 Mbps over the 5 GHz band.
802.11b and 802.11g are commonly combined in the same AP. The bandwidth supported decreases as the distance from the AP increases or as environmental conditions degrade. 802.11b has been around for some time and counts for a very large piece of the wireless networking world. Both 802.11b and 802.11g devices typically use the same access point. 802.11g devices connecting to an older 2.4 GHz AP that only supports 802.11b will connect at 11 Mbps.
802.11a is not catching on very quickly. Its range, 60 to 100 feet, is much less than the 300 feet of 2.4 GHz technologies.. This means that it will take more access points, and a bigger budget, to provide wireless connectivity in larger office environments. In addition, the 5 GHz radio is not compatible with 802.11b or 802.11g devices. So if you decide to install 802.11a AP’s, you’ll also have to replace all earlier technology wireless NIC’s.
This post is part of the series: Introduction to Local and Wide Area Networks
Understanding how networks work is an important first step in understanding information security. This series provides everything you need to know to get started.
- Introduction to Local and Wide-area Networks - Part 1
- Introduction to Local and Wide-area Networks - Part 2
- Introduction to Local and Wide-area Networks - Part 3
- Introduction to Local and Wide-area Networks - Part 4
- Introduction to Local and Wide-area Networks - Part 5
- Introduction to Local and Wide-area Networks - Part 6
- The Importance of Wireless Connectivity