A biometric reader is an electronic device that determines a person’s identity by detecting and matching individual physical characteristics. There are a variety of biometric readers that make personal identification easy and accurate. Some are inexpensive; others are new and expensive.
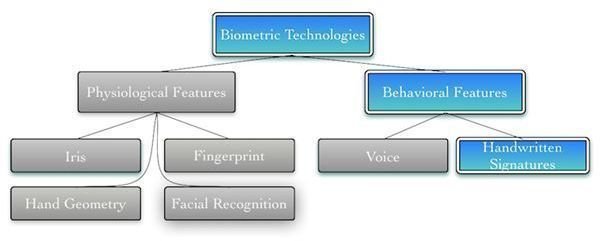
BioMetric Technologies
Biometric technologies fall under different categories that use fingers, signatures, eyes, and voice to identify a person.
See Also: Physical Security Controls
Fingerprint Recognition
What is a biometric reader that we are all familiar with? Fingerprint recognition as the traditional biometric recognition system is over 100 years old. There are two main categories of fingerprint matching techniques: pattern based and minutiae-based. Pattern compares two images to see how similar they are. Patten matching detects duplicates. Minutiae-based uses the location and direction of the ridge endings and splits along a ridge path. Fingerprints appear as dark lines that are the high peaking portion of the friction ridge skin. The valleys between the ridges appear as white space.
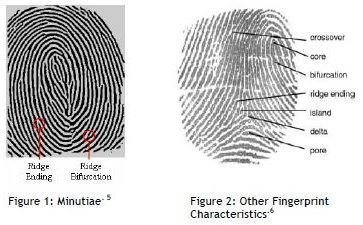
There are a variety of hardware sensor devices used for fingerprint recognition systems. There are optical, ultrasound, capacitive and thermal hardware systems. They collect the fingerprint. Software analysis identifies the fingerprint and associate it to an individual.
Door Access Systems
Fingerprint recognition is the most practical choice for a biometric system because of its reliability, non-intrusive interfaces, and cost-effectiveness. For that reason, using fingerprint biometrics in a door lock can be cost- and security effective. It uses fingerprint reader technology.
How does the fingerprint reader work? There are essentially three steps. A person’s fingerprint physical characteristic are scanned, turned into a numerical algorithm, and entered into a database. When the person tries to use the door, he must subsequently provide that same fingerprint physical characteristic to be read and recognized by the fingerprint reader before access is granted.
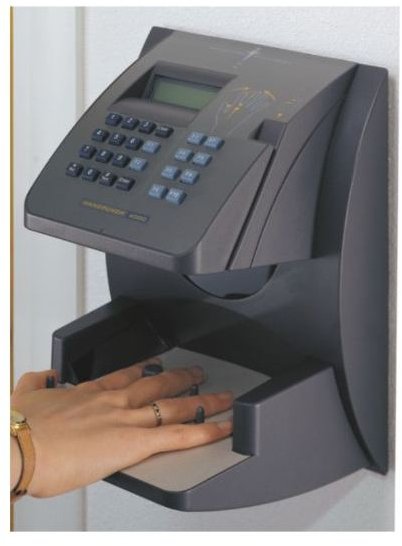
BioMetric Time Clocks
A biometric time clock and attendance tracking system replaces the typical time clock system to track employees and their attendance. The timecard is replace; instead they place their finger on the fingerprint reader sensor, place their hand into the hand reader, or flash a card in front of the proximity or HID card reader; and this marks their logging in.
Signature Recognition
This biometric identification system automatically scans a person’s signature and matches it electronically against a database of known signatures. The idea is that everyone’s signature is unique, and duplication is not possible; therefore this can verify a person’s identity.
There are two different approaches for signature recognition: online recognition, based on how to make the signature; and offline recognition, based on analyzing the outcome of the signature–in other words, analyzing an image statically.
Iris Recognition
Iris recognition is an extremely accurate method of personal identification but it is expensive to implement. Furthermore, scanning the human eye is a sensitive issue that some find disturbing.
The iris is a muscle within the eye that controls the size of the pupil and how much light enters the eye. Before iris recognition can take place, you photograph landmark features. These include the shape of the iris, feature isolation, and location. To make the image you use high quality digital cameras using infrared light. Once those features are collected, they are stored in a database. Then at the appropriate time, the person trying to get access places his or her eye in the iris scanner and the scan occurs.

Sources
See Also:
Using Biometry for Security and Identification
Biometric Devices: They Provide IT Security
BioMetric Technologies Image: https://www.mobbeel.com/technology/signature/
Finger Print Recognition and image: https://www.biometrics.gov/Documents/fingerprintrec.pdf
Door Access Biometric Systems and image: https://www.akmelock.com/
BioMetric Time Clocks and Image: https://www.sundialtime.com/biometric.asp
Signature Recognition and Image:https://www.mobbeel.com/technology/signature/
Iris Recognition: https://www.biometrics.gov/Documents/irisrec.pdf
Image: https://www.aditech.co.uk/L-1ID.html