Biometrics measures biological characteristics for identification or verification purposes of an individual. Since IDs and passports can be forged, more sophisticated methods needed to be put into place to help protect companies and individuals. Discussed are the two types of biometrics.
In biometry,
there are two types of biometric methods.One is called behavioral biometrics. It is used for verification purposes. Verification is determining if a person is who they say they are. This method looks at patterns of how certain activities are performed by an individual_._
Physical biometrics is the other type used for identification or verification purposes. Identification refers to determining who a person is. This method is commonly used in criminal investigations.
Behavioral Biometrics
Keystroke or Typing Recognition
Keystroke recognition measures the characteristics of an individual’s typing patterns, including the time spacing of words. It can be used for identifying people who may create inappropriate email or conduct fraudulent activity on the Internet. Keystroke or typing recognition software is installed onto a computer. When a person uses it their typing patterns are then measured. It effectiveness depends on an individual using the same keyboard as different types may create a variance in the keystroke pattern measured.
Speaker Identification or Recognition
Speaker identification and recognition is used to discover an unknown speaker’s identity based on patterns of voice pitch and speech style. Behavioral patterns of a voice differ with every individual. In criminal investigations, a voice is compared to a database of voice model templates that were previously recorded. The success of the biostatistics voice data comparison varies since it is based on the availability of the voice recordings.
Physical Biometrics
Fingerprint Identification or Recognition
This type of biometrics compares two fingerprints to determine identification. It analyzes the ridges and valleys patterns on the fingertip for differences. These fingerprint patterns include the arch, loop, and whorl. In biometric forensics, fingerprint identification is useful for narrowing down suspects. Some laptop computers utilize fingerprint biometrics for authorizations for such purposes as logging in and entering website passwords.
Speaker or Voice Authentication
Speaker or voice authentication is the analysis of vocal behavior by matching it to a voice model template (that was previously recorded). Since every voice is unique, the physical characteristics of the speaker’s voice can be measured. It is effective for security purposes and used to help prevent fraud or theft of critical information/assets.
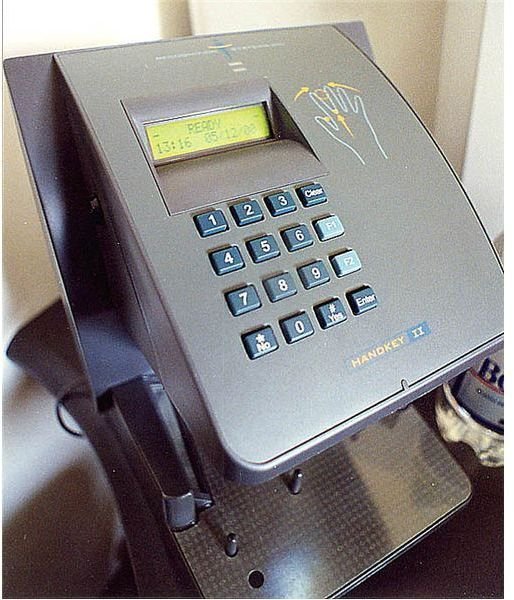
Hand or Finger Geometry Recognition
- The method uses 3D analysis of the finger for tracking and identification purposes. An individual places their hand (palm down) onto a special plate. A camera takes a picture of it and analyzes the length, width, thickness and surface area of the hand. This recorded biostatistics information is then stored for future use. Companies have used this type of biometrics for attendance tracking and accessing secure entrances.
Facial Recognition
Facial recognition uses algorithms to analyze features. These include the position/size/shape of the eyes, nose, cheekbones and jaw line. Initially, this process was known as 2D facial recognition. The 2D images were typically taken from security cameras that have integrated facial recognition technology. For the best results, face images needed to be looking directly at the camera with enough lighting. After analysis, they could be compared to other face images for identification purposes.
3D biometric facial recognition is the updated version of this identification process. Images are captured with a real-time 3D camera or by digitally scanning a 2D photo. Detailed information like the contour of the eye sockets, nose and cheekbones help make identification easier. The 3D method is also not affected by lighting issues. This improvement has benefited law enforcement and biometric forensics investigations.
References
- Images from stk.xchng website.