Overview: Information Security Primer - Part 1
The Evolution of Technology and the Rise of Information Technology
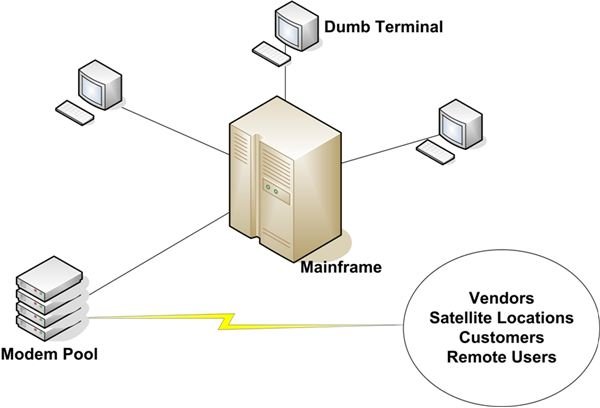
In the early days of computing, securing information was relatively easy. Information was stored in a locked room, on a large mainframe computer, with a proprietary operating system, supporting tightly controlled remote access from known locations. Figure 1 depicts this type of environment.
The dumb terminals used to access applications and data on the mainframe were incapable of storing data locally; they had no disk drives. Viruses were unknown because information couldn’t be loaded or downloaded to terminals, and the Internet wasn’t a critical business network. Physical access to the mainframe was necessary to load programs. Even then, the permissions necessary to load applications were very tightly controlled. In addition, technology that allowed the easy download and removal of information, such as thumb drives, didn’t exist. Access to the information on mainframes was effectively controlled by a few User IDs, passwords, and locked doors.
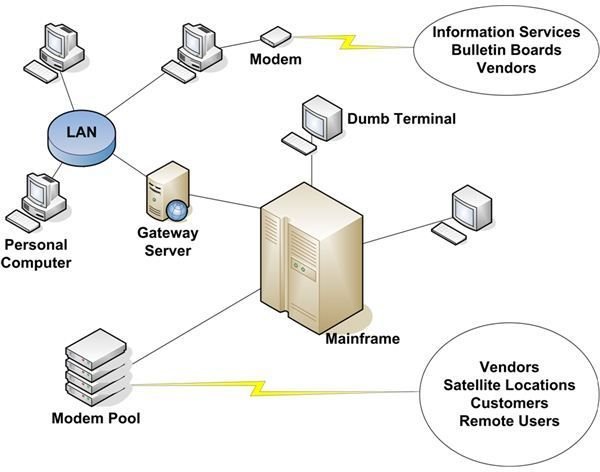
The next major innovation in business processing was the personal computer (PC). The PC introduced new security concerns. First, much of an organization’s processing was moved to the PC. Unlike dumb terminals, PCs had local processing capabilities and local storage devices. In addition, PCs provided opportunities for placing confidential information on removable storage, such as a floppy disk, which could be easily moved to unauthorized locations. Second, organizations began to connect PCs together in LANs. This allowed the movement of information between PCs and a mainframe. See Figure 2. As more and more information moved about an organization, there were additional opportunities for it to be intercepted by unauthorized individuals.
Third, PCs introduced non-proprietary OS’s, like MS-DOS. (Microsoft Disk Operating System). With the proliferation of these OS’s came the birth of viruses. Early viruses were spread by floppy disk sharing or by moving files from one PC to another over the LAN. Finally, PCs were frequently equipped with modems. Connecting a simple telephone line to one of these communication devices provided users with access to the outside world. Although the Internet didn’t exist, threats to information security were still downloaded into business environments by unsuspecting business users.Like with the mainframe-only environment, security was primarily provided by User IDs, passwords, and locked doors. The mainframe remained the primary center for the processing and storage of critical business information.
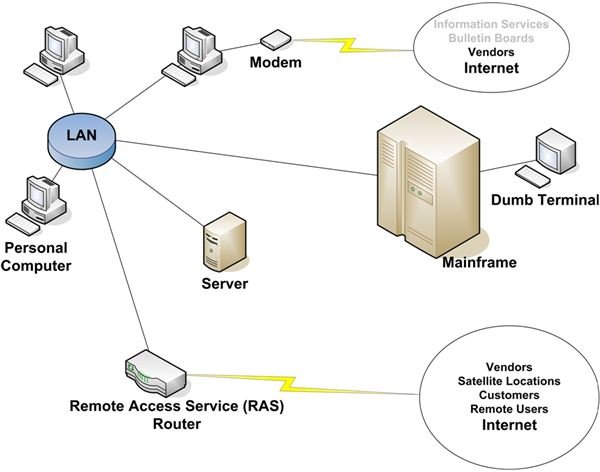
Over time, the simple PC evolved into a PC server. The combination of the processing power of the PC server and the convenience and flexibility of desktop PCs led to less dependence on the more costly and proprietary mainframe. Dumb terminals were gradually replaced by PC’s. Figure 3 depicts a LAN centric network. The mainframe has become just another network attached device. The primary device used to access the mainframe has changed from the dumb terminal to the desktop PC. Modem pools were replaced by more flexible and secure remote access routers.As LAN’s grew, so did the decentralization of an organization’s information. No longer was information stored in a centralized mainframe. Much of the information necessary to operate the business was located on multiple servers or desktop PC storage.
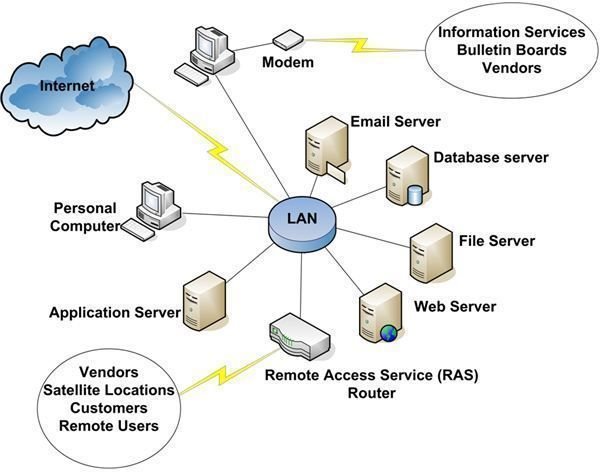
One of the most significant developments, however, was the introduction of the Internet. This public, shared, global network was accessible from both controlled access points as well as uncontrolled access points, such as locally attached modems. Customers and vendors began insisting on business use of the Internet for email, file transfers, or simply providing general information about an organization. Along with vendors, customers, and employees, crackers also got busy transforming their viruses into worms and trojans that had the capability of moving effortlessly across the Internet’s various nodes.Today, the mainframe is usually absent from an organization’s network. Instead, large businesses deploy hundreds of servers to process and store data. Figure 4 is a logical view of a modern network.
In today’s networks, organizations must protect information as it travels across various network devices and is stored on a variety of storage media. In addition, there are multiple connections to the outside world that are less safe than in the past. For example, most organizations have a high speed connection to the Internet. The Internet is like the Wild West; no one is in control and it’s each person’s responsibility to provide protection for himself. Many organizations have multiple locations, each with a LAN, storage, and outside connections. This significantly increases the risk to critical information. Although the move from isolated, centralized processing to distributed, connected networks has improved business agility and productivity, it has also introduced a host of security challenges. This resulted in the elevation of Information Security from simple account management to an integral part of business operations.
Figures (Hover for caption, click to enlarge)
Key Terms
Mainframe – A large, expensive, powerful computer. Early mainframe computers often filled an entire room. These systems became know as mainframes because the early models occupied a number of metal frames, the main one containing the processor and memory.
Proprietary Operating System – An operating system (OS) is an application that manages the processing activities of a computer. Microsoft Windows XP, Microsoft Windows Server 2003, and Linux are examples of operating systems. A proprietary operating system is written for a specific computer and cannot be run on any other system. For example, the IBM AS/400 ran an operating system called OS/400. OS/400, written and sold by IBM, could not be run on any other device but the AS/400. Compare this to a non-proprietary OS like Windows XP that can be run on many different platforms from a variety of vendors.
Dumb Terminal - A device consisting of a screen and keyboard, used for communicating with another computer, usually a mainframe. Unlike a personal computer it has no local processing capabilities or disk storage.
Thumb Drive – A thumb drive is a small, compact, rewritable storage device that interfaces with a computer through high speed interfaces, like a USB port.
Modem Pool - A modem pool is a group of modems that answer calls placed to a single phone number. Users can also use the modem pool to dial out to remote locations. Modem pools, or other types of dial-up devices, were popular for remote terminal and personal computer access to centralized business systems prior to the introduction of Internet-based technologies.
Gateway Server - At the most fundamental level, mainframes and PC’s use different coding standards to process information and different protocols for communication. The gateway server acts like an interpreter, helping the PC’s and the mainframe understand each other
This post is part of the series: Information Security Primer
This series introduces those new to information security to the basics. It is a good start for entry-level security professionals or those who need to know a little more about the subject.