Phishing is all about making money and trying to get away with it. With thousands of businesses the target of phishing scams, how can you determine if a business you deal with has been the target? How big is the problem today? These answers and more will be discussed in this article.
Phishing Cases
When talking about phishing cases, name any large scale business that deals with financial information or processes payments and they’ve likely been a target of a phishing scam.
One of the largest phishing cases came to an end in 2009 when the FBI and Egyptian authorities charged 100 people in one of the largest scams in phishing history. This particular crime ring was responsible for stealing approximately $1.5 million from 2007 to 2009 from various banking and financial institutions and their customers. ‘Operation Phish Phry ’ (I’m not kidding) was a success.
To find out more about how many companies are targeted, one can take a look at the Millersmiles.co.uk site and phishing database. As of March 2010, over 1800 businesses have been targeted – some more than others. When you drill into the information, you can see specific phishing example emails for each business. Take Amazon for example – with over 150 types of phishing scam emails, they are one of the most targeted businesses out there. You can see the full list here .
To give you an idea of just how quickly the prevalence of phishing has become, the Anti-Phishing Working Group (APWG) – a trade group that strives to solve the issue of phishing through education and technology, estimated that 174 unique phishing cases were discovered in January 2003. A little over a year later – in May 2004, over 1200 unique cases were reported. If we look at a popular phishing tracking site called PhishTank, an average of 600 unique phishing attacks are reported daily. Pretty amazing. Obviously the more people that fall for phishing, the more effort phishers will put into tricking people out of their money.
Protecting Yourself Against Phishing
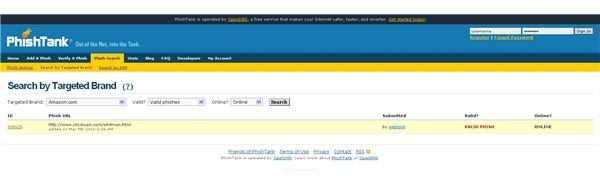
Finding out if a brand is targeted by phishers is as simple as heading over to the phishtank.com website and doing a search in their comprehensive database. Head over here and select the brand you are looking to search for. You can also specify whether or not you only want to search for valid phishes (ie, sites that really are seeking information maliciously) and online phishes (ie, the phishing site is still active). When you finish the search, you’ll get a list (see figure below). Click on the ID to learn more about the reported phishing scam. One way to use the data from PhishTank is by setting your DNS settings to use OpenDNS (who owns and operates PhishTank). By using OpenDNS, when you go to a site that has been verified as a phishing site, you’ll be redirected to a safe location – stopping you from accessing the malicious site.
Below are a few more resources to help you understand phishing and how to protect yourself.
Understanding Social Engineering – Techniques Used
Top Tools to Spot a Phishing Scam