Phishing Scams are a dime a dozen these days, but luckily there are many free tools you can arm yourself with to keep your identity safe. This article will share with you some of the top tools to help spot phishing scams as well as some guidelines for staying safe.
Overview
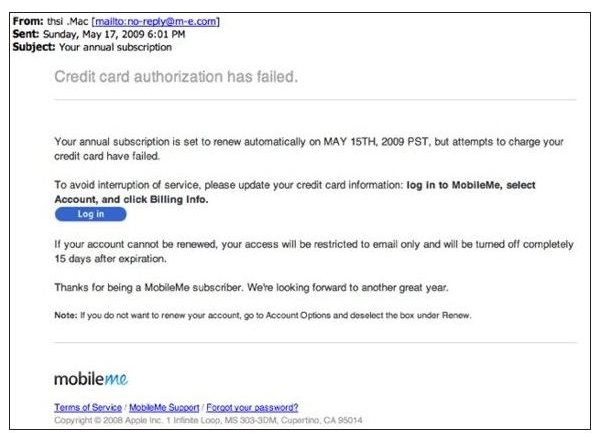
In my article entitled “Understanding Social Engineering” (link coming soon), I discussed a few popular techniques used by con artists trying to steal your money or your identity. Phishing by far is the most popular technique used primarily due to the ease of the con. Social engineers can set up a fake email template, website and domain in the matter of days with freely available tools on the internet. See Figure 1 and 2 for example emails sent out to look like the “real thing”. What can you do to fight back? Luckily, there are some great tools out there to help you.
Anti-Phishing Tools
You have a few options when it comes to protecting your computer and yourself against phishing attacks.
- Antivirus vendors products typically include a “web” or “online” edition of their product that includes a browser add-in that monitors a list of known phishing sites and will redirect you if you attempt to access one of the malicious sites. These are great tools as they are typically easy to maintain, have high reliability and are relatively inexpensive. One example is Trend Micro Internet Security Pro.
- Anti-Spam products are a necessity not only for blocking the flood of SPAM you’re likely to get, but also for taking care of pesky emails that direct you to phishing sites. Many of the free email providers (Yahoo, Gmail) already do some basic filtering for you.
- Browser Add-Ons are freely available to help protect you. Microsoft Internet Explorer 8 includes built in phishing protection while add-ons are available for most other browsers. One example of a Firefox add-on is the Google Safe Browsing add-on. You can find more information here . Google Chrome includes phishing support – additional information can be found in this Brighthub article by Yvette Davis.
With these tools, you should be well on your way to protecting yourself from falling for phishing scams.

Eyes + Brain = Great Tool
You don’t always need to use a tool to spot phishing attempts – using your eyes and brain is sometimes the easiest way. Here are some basic guidelines to help practice “safe computing”.
- If you receive an account notice via email from one of your service providers (bank, telephone, cable, etc.) and you have a gut feeling the warning or issue may be legitimate, use a phone to call and talk to an account rep – don’t click on the links in the email.
- Never click on a link in an email to change your password. If you do want to change your password, go directly to the web site and change it.
- Realize that most companies will not simply send you an email if you have account issues. For example, if your credit card company suspects unauthorized usage, they are going to call you – not send an email.
- Look for grammatical or spelling errors.
- Keep an eye out for generic emails – most companies will tailor emails directly to you as opposed to “Valued Customer” or “Dear,”.
- Be sure to look closely at the URL they are pointing you to. Hover over the link to make sure the real business domain is used. Note that https://accounts.bigbank.com could be a legitimate site whereas https://accounts-bigbank.com could be a phishing site.



