How to prevent strangers accessing or viewing your data when using a Bluetooth-enabled device? The answer is simple and that is to take advantage of authentication and encryption in Bluetooth software.
Bluetooth Security Modes
Authentication in Bluetooth uses 128-bit random challenge. 32 bits of 128-bit are used for authentication process and the remaining 96-bits are used to create the Bluetooth encryption key.
There are four security modes, but each version of Bluetooth supports some and not all these modes. Below are the available Bluetooth security modes:
- Security Mode 1 – a non-secure mode in which security functionality is bypassed. Bluetooth connections do not employ any method to prevent other Bluetooth-enabled devices from establishing connections. This mode is only supported in Bluetooth v2.0 with Enhanced Data Rate (EDR) and earlier devices. Example is some Dell computers or Nokia E71 smartphone includes Bluetooth v2.0 + EDR wireless technology or modules.
- Security Mode 2 – service level-enforced security mode that uses Logical Link Control & Adaptation (L2CAP) and Link Management (LMP) protocols. Encryption for Bluetooth is used in this type of security mode. Authentication is not required in using this mode. However, it can be used before a Bluetooth-enabled device can establish connections. Security mode 2 is available in Bluetooth v2.1 + EDR devices.
- Security Mode 3 – link level-enforced security mode. All connections between Bluetooth-enabled devices require authentication and encryptions. Security Mode 3 is only supported in v2.0 + EDR or earlier devices.
- Security Mode 4 – similar to Security Mode 2 but the Simple Sharing Pairing (SSP) was introduced. Bluetooth devices with v2.1 + EDR can use this mode. If the other device does not support SSP, the security mode 2 is to be used.
Note that Bluetooth v3.0 + High Speed (HS) and v4.0 also use the above security modes. The only changes are v3.0 is focused on data reliability and higher data rate, while the latter is called Bluetooth Low Energy which means the version use less power with higher transmission speed.
How to Take Advantage of Encryption in Bluetooth
People should use the strongest Bluetooth security mode available for their Bluetooth devices e.g. wireless headset , printer, USB adapters, or mobile phones. It is important to use the above-mentioned 2, 3, or 4 security modes to prevent threats.
Authenticate the connections made by a Bluetooth device to not to allow other Bluetooth device using your connection or accessing the device. When entering the PIN code, use 8 or more characters to authenticate.
The most important security feature in using Bluetooth is the use Simple Sharing Pairing (SSP) to pair allowed or trusted Bluetooth-enabled devices.
Keep Bluetooth software and drivers up-to-date to take advantage of product improvements and security fixes. It’s also recommended to stop using a non-supported or not secure Bluetooth-enabled devices or module, e.g. Bluetooth 1.0 and 1.2.
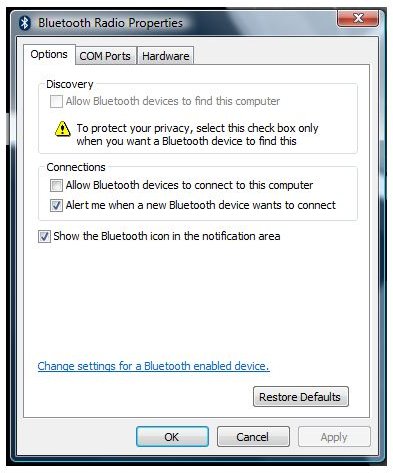
A Bluetooth software setting is important to configure by not allowing any computers to connect to the computer unless you are expecting an incoming connection from other Bluetooth-enabled devices. It’s also important to not to make it discoverable so hackers or intruders scouring the area will not find the unused Bluetooth connection.
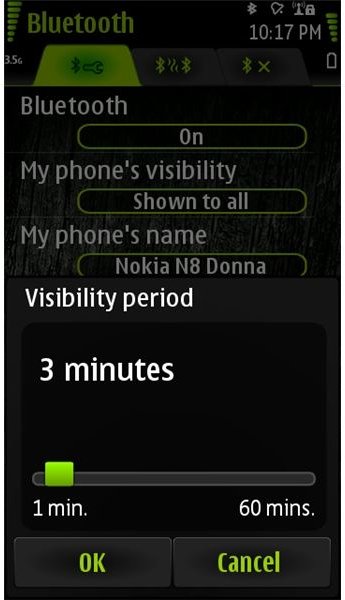
If your Bluetooth software provides an option to limit the device visibility, take advantage of it. The image below is an example option that Nokia N8 smartphone provides where you can temporarily show the device for other device to receive or send data:
Final words
If you are to find or buy Bluetooth enabled devices, e.g. a mobile phone, laptop or USB Bluetooth adapters, check whether the Bluetooth version is 2.1 or higher. Newer Bluetooth software provides better security features. Further reading in security Bluetooth in Windows can be found in this article .
Image credit: Screenshot taken by the author.