If the anti-virus software you had established on your systems is going to have its way and check for each program or file against its updated database – it is still firefighting. It isn’t pro-active defense. How are you going to combat ‘Unknown" security threats? Trustware Bufferzone helps.Read on
To combat the vicious digital vermin on the Internet, you would have gone all out to battle them all with your latest anti-virus software, firewall or perhaps both them combined into one big expensive Suite. No one is going to hold you to the wall. You deserve accolades, really, because you at least take precautions and it’s not your fault if your system is haunted by any of these above mentioned vermin after you gave it your best shot.
Anti-virus Software might not be your best bet yet, because we are forever in the fire-fighting mode. The anti-virus software that you had purchased relies on signature matching technology which checks the digital signatures of each file that you come across or download to the ones updated in the software’s database.
That isn’t comforting at all, since there are a lot of threats we don’t even know that exist.
Solution? Trustware Bufferzone 3.01 perhaps?
No, this isn’t your regular anti-virus software. It has nothing to do with anti-virus at all. It isn’t even a firewall. It is a decidedly unique, rather quirky approach to solving your “Always-on and hence always vulnerable” Internet surfing habits.
Bufferzone uses concepts of virtualization to achieve a “make believe” system “Virtually” with the same configurations and sets up as that of your laptop or PC. That means, it makes space elsewhere virtually, the environs of which will look exactly similar to that of your PC or laptop – the registry entries, the desktop, the configurations, etc – and allow you to use this virtual system instead of your actual system.
So, the next time you would like to go online and surf, or if you like to ensure that there could never ever be a situation wherein your enterprise’s security can be jeopardized, all you have to do is set up a bufferzone for each of the systems that connect to the Internet.
How Does Web browsing Work with Bufferzone?
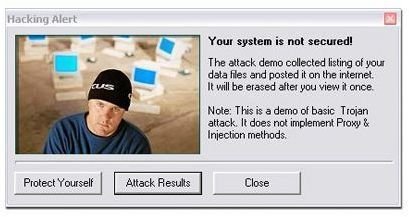
When you download and install the bufferzone software, you will have to run the installation manager as you would for any application. Once installed, it shows up on your task bar to the lower bottom right corner. When you fire up one of your browsers to surf the web, there is a slight delay in launching your browser (since the bufferzone software has to configure your settings appropriately). As you go about your normal activity, you will realize you are on your bufferzone’s virtual atmosphere when you see a red border surrounding any application window that you might open up. So henceforth, any file you might download and anything that you might do, is all being done virtually.
So, the take away is that if you were to be attacked now, while you are on the bufferzone’s virtual atmosphere, it wouldn’t harm your real system, since all your activity can be cleansed or deleted leaving no traces of anything behind (that includes all your digital vermin too).
Part 2 (of 2) discusses how Bufferzone works with Files, Folders and Other applications and precautions on using bufferzone.
[ Img Courtesy net-security.org ]
This post is part of the series: Trustware Bufferzone
This is a 2 part Series on Trustware Bufferzone software.


