How do files, folders and applications work? How would you download or upload something with Trustware BufferZone 3.01? Read on to find out.
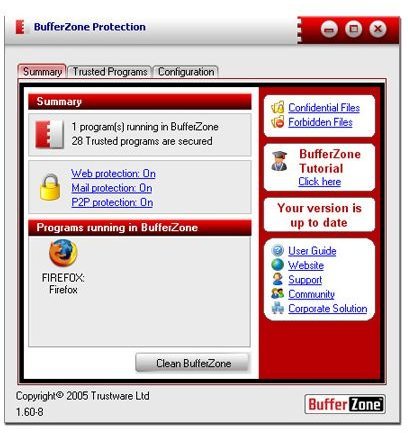
Bufferzone V3.01, brings to fore a rather unique approach to combating the various threats that prowl online. The computer users are forever paranoid about these threats and Bufferzone then would come as a gift because its approach to fighting the threats turns the tables around in the sphere of Internet security. The Part 1 discusses how buffer zone allows you to surf online without the fear of any of these threats lurking around shady corners. This part discusses how Bufferzone works with files, folders and other applications and also plumbs into some precautions you must take.
Bufferzone with File Folders and Other applications
As mentioned earlier, Bufferzone operates by stashing your entire operating system into a similar ‘make believe’ virtual environment – as a replica of your usage environment. Just as in the case of web surfing, any file downloaded or saved into the bufferzone’s virtual environment is designated as such and you would have this small indicator showing that your file currently resides on the bufferzone’s virtual storage. You are actually opening the file out there in the virtual zone itself. However, if you deem the file to be safe and free from any malicious code, you can easily move into your actual system by right-clicking and choosing where you want your file to be downloaded.
The best of the software comes forth when you try to download and open applications. This is the hot bed of most of the malicious code – like spyware and malware – so in this case, when you download an application, it sits in the virtual zone by default and as you double-click it to open, it opens in the virtual environment again and this is the best way for you to see if the application is trustworthy or not.
Bufferzone Clean-up: Coup De Grace
There are certain downsides to this software as well – all of this activity that you do on your virtual zone created by your Bufferzone software can be deleted and cleansed. Once you do this, there is no going back and if you have anything that you wanted in that virtual environment, it would be gone forever. The cleaning system is robust and doesn’t leave a trace within your system. You can set-up and delete your virtual workzones any number of times.
Precautions while Using Bufferzone
- Do not use Bufferzone when trying to download and store “once-only” type files, like say your subscription to some software, online services, etc.
- Do not use Bufferzone while transacting with financial accounts and bank accounts.
- Bufferzone has no way to know what’s right and what’s wrong. It doesn’t even know what’s important for you. Move out all files before you purge it all.
The Verdict
What’s Good: A rather unique approach towards internet security; keeps you safe from even the unknown threats; enterprise version is available; uses virtual environments and systems to isolate Internet activity from the actual hardware
What’s Bad: Software will take some time getting used to; has no way to remind you that you have stored certain files that might be important and that you are about to delete them forever; no multi-user access; doesn’t support Windows Vista
Costing about 40$ per system, per user, With this rather unique approach to fighting Internet security it gives you the much needed freedom and piece of mind. If you are using it for your small business, you can try out the enterprise edition for free( available as evaluation version)
[ Img Courtesy net-security.org]
References and Additional Resources
Mark Woodstone’s Review on Trustware’s Bufferzone at net-security.org
This post is part of the series: Trustware Bufferzone
This is a 2 part Series on Trustware Bufferzone software.