This article describes how to make a copy protected photo CD for distribution. This helps to ensure that no one can make unauthorized copies of your images.
Introduction
This software tutorial attempts to answer the question “how do I make a copy protected photo CD?” It is targeted at photographers who distribute copies of their work to potential clients and want to safeguard them from making unauthorized / unlicensed copies of their copyrighted images and also for amateur / hobby photographers who want to distribute their work on media such as CDs but want to ensure that no unauthorized copies are made without their consent.
Adding Copy Protection to the CD
Various Types of Copy Protection
The various types of copy protection which have been used over the years include:
- File Level Encryption
- Passive Protection
- Product Activation
Each type of copy protection can be added to the CD as described below.
File Level Encryption
This is not really copy protection per se, but rather a way to add security to the files. This ensures that even if the CDs are obtained by unauthorized personnel, the only way they can access the data is by using an “encryption key”.
In order to add file level encryption, i.e. adding password protection to one’s files, one can make use of archiving software such as WinZip , WinRar, etc.
Adding Password in WinRar
- Right click the folder to be encrypted and select “Add to Archive…”
- Click on the Advanced Tab and click on Set Password
- Type a Password and click on OK. Have the Encrypt Filenames checkbox selected for added protection
Password Protection present in Microsoft Windows can also be used.
**
Passive Protection
Passive Protection involves adding an additional track onto the CD, usually a dummy data track, which causes the default Windows CD drivers to throw an exception (display an error) while trying to copy the CD, but work well while trying to read the CD.
This can be done by using a free program known as CD Manipulator using the following steps:
-
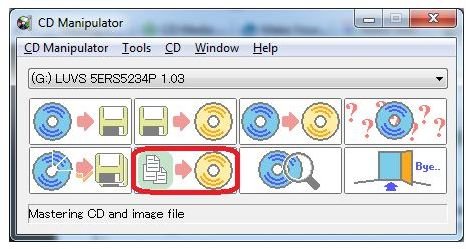
Open CD Manipulator. Select the option “Mastering CD and Image File”.
Advertisement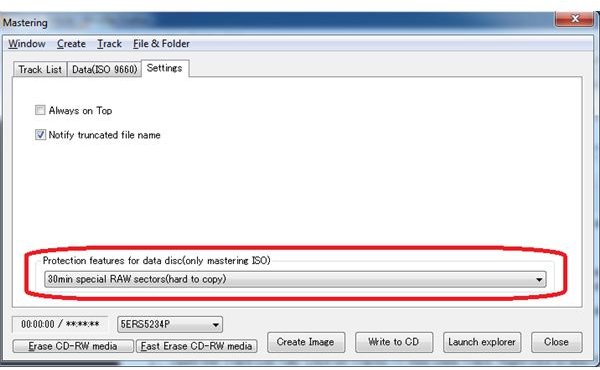
-
Open the Track List Tab. Click on Tracks –> Add Data Track. Right click to add Files and Folders as required.
Advertisement -
Click on the Settings Tab. Use the Protection Features drop down box to select the level of protection (30 second RAW Sectors are easy to copy whereas 30 minute RAW Sectors are very hard to copy).
-
Click on the Create Image File and then Write to CD as required.
Advertisement
For further information, read this similar CD Copy Protection technique using NERO and CloneCD .
Note: However, this technique is not foolproof. Enhanced software which use modified drivers to read the CD may be able to bypass such protection methods. Such CDs may also be readable on other operating systems such as Linux and Mac-OS.
Product Activation
Product Activation involves a certain amount of technical expertise and is similar to Product Activation in Windows or other software such as Microsoft Office which involve activation over the internet. By providing an authentication key which is verified by your server, you will prevent most people from duplication. The downside to implementing this technique is significant expenditure, and is not easily implementable by the home user. Also, the product activation technique is yet to be perfected, even by big corporations such as Microsoft. So it may be too complex and too expensive a solution for an individual’s needs.
Conclusion
In conclusion, any one of the above methods in isolation or in its vanilla format may not be the best technique. My suggestion is to use a combination of these methods as described below.
- Add a watermark to all your sample images which you provide for distribution purposes.
- Password protect the images using an archiving software as described above.
- Copyright all the images using IPTC tags.
- Add passive protection to the CD using CD Manipulator as described above.
These above methods when used together provide very good security for an individual’s needs. You may also want to read Benefits and Cautions of Different Methods Used to Protect Photos for more information.