How to Use Avast Removal Tool & Boot-Time Scanner for Windows
Avast Boot-Time Scanner
Avast boot-time scanner is one of the great features in the Avast antivirus program. Boot-time scanning in Avast scans all hard-disks or only the system drive. It checks the boot-sector for viruses, worms, Trojans, spyware, rootkits, adware, potentially unwanted programs (PUPs), and other types of malicious software.
It’s easy to use the boot-time scanner as the Avast removal tool rids your PC of nasty infections, especially from malware that loads even before the Windows logon or desktop has started.
Why Use Avast Boot-Time Scan?
Avast is able to detect rootkit infections and some malware, but removal requires a sophisticated malware removal engine. Boot-time scanning in Avast helps in removing active but hidden malware infections. Also, there are rogue antivirus programs that may prevent some antivirus and anti-malware scanners to do their job – to scan, detect and remove the fake AVs.
Boot-time scan in Avast does not require advanced knowledge because Avast Software, the maker of Avast antivirus software, has integrated the boot-time scan feature within the program. There’s no need to create a bootable malware removal tool in using the boot-time scanner.
Using Avast to Remove Malware
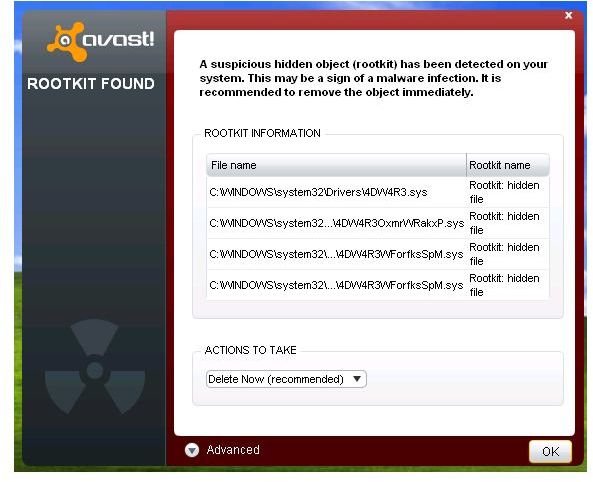
If you received an alert that there is rootkit infection on your computer, but Avast couldn’t remove it using its on-demand or real-time detection and removal engine, the only way to get rid of the infection is by using boot-time scan in Avast.
The image at the left (click to enlarge) is an example of a rootkit detection by Avast. Allowing the antivirus program to scan the system to remove the rootkits will fail.
The test system in this article is infected with a TDSS rootkit which can cause a Google redirect virus infection. Also, I infected the computer with several types of Trojans such as Trojan dropper, agent and password stealer. I also installed a fake anti-spyware that displays a fake Microsoft Security Essentials Trojan alert.
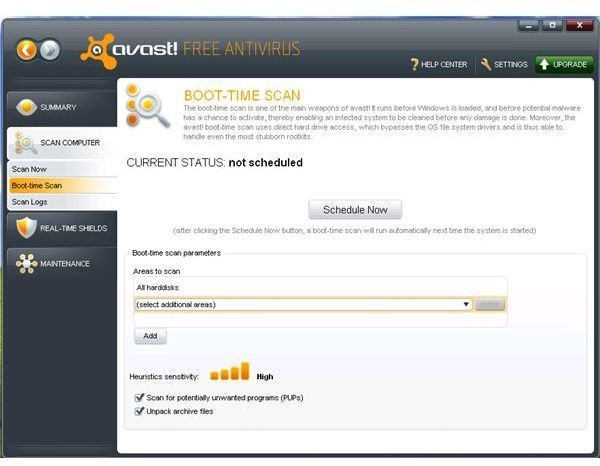
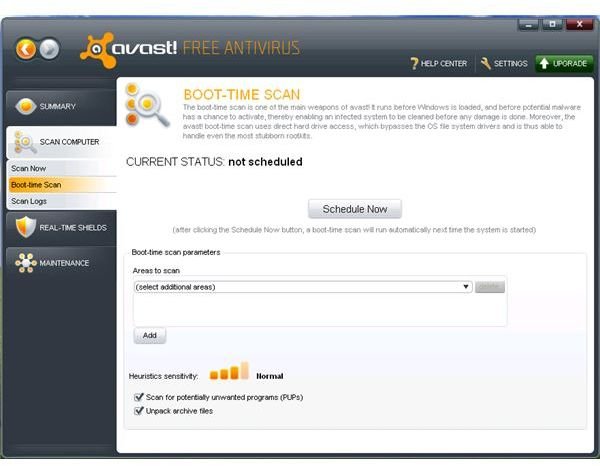
To use boot-time scanner and the Avast removal tool for malware, simply open Avast antivirus program, click on Scan Computer, and then select Boot-time Scan. The default settings are enough and recommended, but if you prefer adjusting the sensitivity of its heuristic engine, simply click on the last bar to use high sensitivity. Avast boot-time scan can detect potentially unwanted software and decompress archived files. Leave those settings as is, proceed to selecting the areas to scan by clicking on the drop-down menu, and then select All harddisks. Finally, click on Schedule Now, and then click Restart computer to allow Avast in running a boot-time scan.
Options of Avast Boot-Time Scanner on Detected Malware
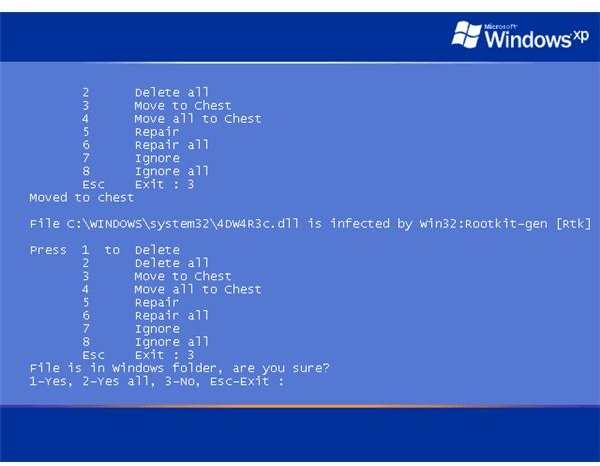
When the Avast boot-time scanner detects malware infections on a system, it will display the options on how you want the Avast boot-time scan module to handle the detections, by choosing the correct number:
- 1 Delete
- 2 Delete All
- 3 Move to Chest
- 4 Move All to Chest
- 5 Repair
- 6 Repair All
- 7 Ignore
- 8 Ignore All
If the detected item is confirmed malware only and not an infected critical system or program file, it is best to choose “Move to Chest” or “Move all to Chest” by entering number 3 or 4. This allows Avast to remove the infection but also keep the copy in quarantine. Quarantining any detected and removed files is recommended, just in case there is false detection in any antivirus program.
Only use “Repair” or “Repair All” if you are positive that the detected item by Avast is a legitimate and critical system or program file. By choosing the repair option, Avast will try to disinfect the file by removing the malicious code, injected by malware.
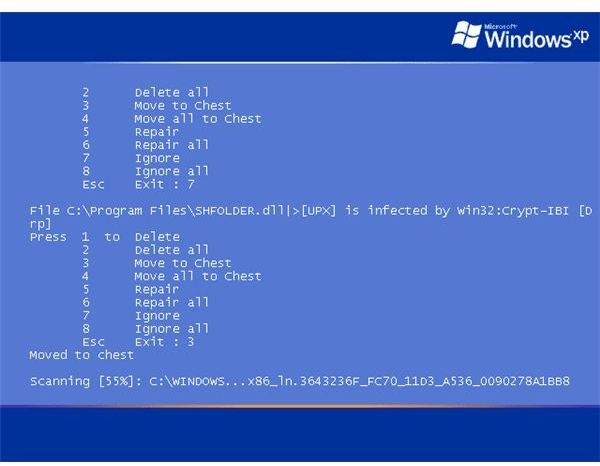
Note, that if the malware is located in critical system folder such as System32 or the Windows directory, the Avast boot-time scanner will prompt another option, which is whether you are sure you want to remove the detected item from system folder. Select the appropriate number to continue with the removal of rootkit or other malware files in the Windows directory only if you are positive that it is not a legitimate system file.
The screenshot at the left (click to enlarge) is an example of malware that is located in the Program Files directory and as you can see, there is no additional option whether to really remove the infected file. It is because Program Files are not a system folder.
Screenshot by author courtesy of <em>Avast Software</em>.