There are multiple types of security, physical and logical. Physical security involves things like locks or biometrics. Logical security examples consist of software safeguards including access control and auditing, user account management, violation and security activity reports, and firewalls.
Access Control and Auditing
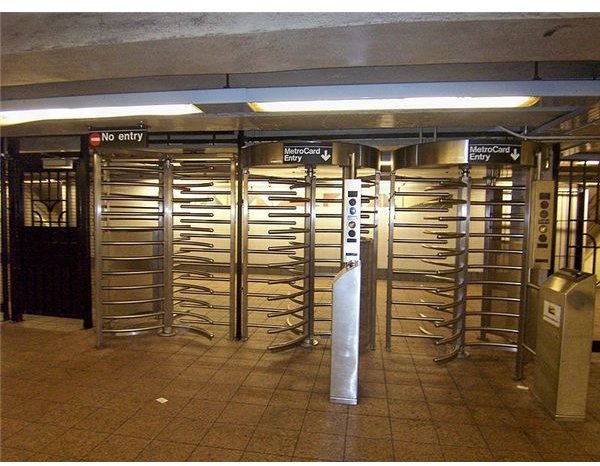
Access control is a system enabling authorities to control access to areas and resources in a given physical facility or computer-based information system. Access control is, in reality, a common, everyday phenomenon. For example, a lock on a car door is essentially a form of access control. The PIN on a bank’s ATM system is another form of access control. Even nightclub bouncers, standing in front of a door, are another example of (perhaps) a more primitive mode of access control. Using an access control mechanism is important when persons seek to secure confidential, important, or sensitive information and equipment.
Auditing is a way of tracking the occurrence of entrance or attempted entrance into a system. This is important because it shows how successful the access control system is, as well as who was denied, and if they attempt entrance more than once, why are they intent on getting into the system?
See also: Physical Security Threat Assessments
User Account Management
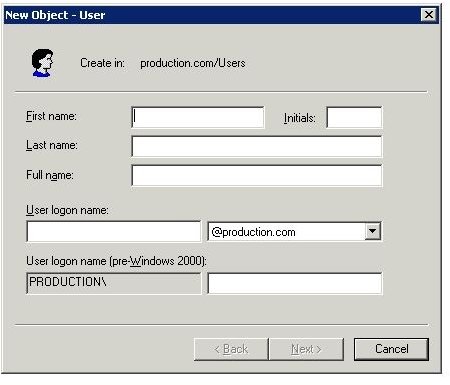
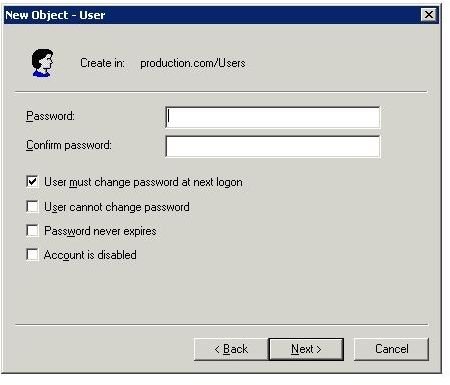
Logical security examples include user account management. In order to provide access control to a user, several steps have to be in place to make it work. It is necessary to create a user account with a login and password. Special features have to be in place here as well. For instance, the login account must uniquely identify the person, but it must be part of a standard similar to all other logins. Secondly, the password has to be sophisticated. It must be at least 6 to 10 characters in size; it cannot be a common password, like “password”; it should have upper and lower case letters and also numbers.
Another part is the access control even after the user is in the system. For example, a user should not have access to finance folders or documents (unless the person is in the finance department). Besides location restrictions, an administrator or manager can put restrictions on document or folder use, such as whether the user can read but not modify or even create.
See Also: Securing your Network with Policies and Procedures
Violation and Security Activity Reports
Once you create a network, you need to monitor it. Two questions should be part of the examination: Who is trying to get access, and how often do they try? Two possible answers should develop; one involves the normal users with access to the network, and the other is unknown users, possibly hackers. From this the IT security administration should check to see that violations and security activity is logged into the system, that it is reported, reviewed and appropriately escalated. This must be done frequently not only to identify and resolve incidents involving unauthorized activity, but to test whether the system is working at all, and how is it performing.
See Also: Security Log Management for Small Businesses
Firewalls
One of the best-known logical security examples is a firewall. A firewall is a software or hardware device that controls or prevents access into a network. A logical device is a software firewall. A logical firewall can have filtering content like a subnet, or an IP address, or a port. The firewall controls access by controlling what traffic can enter the system. If based on subnets, then any traffic associated with the network designated with a network number and subnet mask, for instance 130.12.0.0 / 255.255.0.0, would be rejected.
Another logical firewall uses Virtual Private Network (VPN) technology instead of Network Address Translation (NAT). With a VPN you have a point-to-point connection which allows only those that were set up beforehand to communicate with the network. NAT takes a public IP address, like 200.10.1.1, and converts it into a private IP address like 192.168.1.1; no other networks have access. This, however, means that the network must be set up beforehand, and anyone that can access the 200.10.1.0 network will be able to access the internal network.
See Also: Why Do We Need a Firewall?
Resources
Logical Security: University Of Houston, Author Unknown https://www.uh.edu/infotech/php/template.php?nonsvc _id=289
Access Control and Auditing :
Image - Wikimedia Commons/Canadaolympic989
User Account Management: WindowsNetworking, Author Unknown, https://www.windowsnetworking.com/articles _tutorials/Networking-Basics-Part12.html (screenshots are part of the site).
Violation and Security Activity Reports: ADAudit Plus, Author Unknown, https://www.manageengine.com/products/active-directory-audit/active-directory-auditing.html
Firewalls: Satten, Cory. University of Washington. E-mail, retrieved at https://staff.washington.edu/corey/fw/variations.html