If you want to restrict any user in your home network from modifying the list of trusted sites that IE uses, use the trusted sites Internet Explorer group policy object editor in Windows. This is the method use by many system administrators to prevent modification in an IE security feature.
Trusted Sites in Internet Explorer Using Group Policy
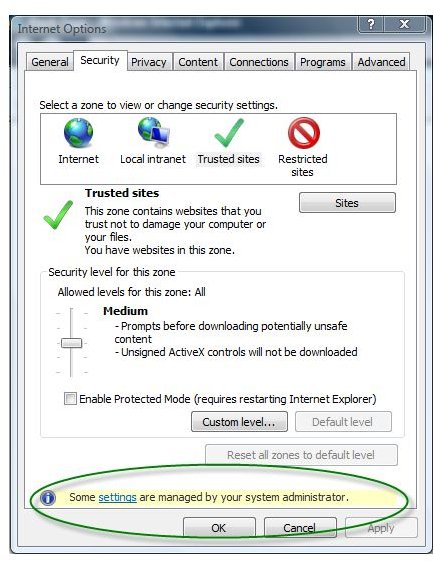
One of the Internet Explorer security zones that most system administrators manage is the Trusted sites. Any IP address or website that they trust in their network or organization is placed in the Trusted sites. Managing the list of trusted IP and URL addresses is easy using the Internet Options in IE, but administrators may not let you change the settings if they have to control the security zones in IE using a group policy object. The image at the left shows an example of security zones managed by a system administrator which means the end-user may not be able to add or remove trusted websites or IP addresses.
Managing Trusted Sites Using Group Policy Object
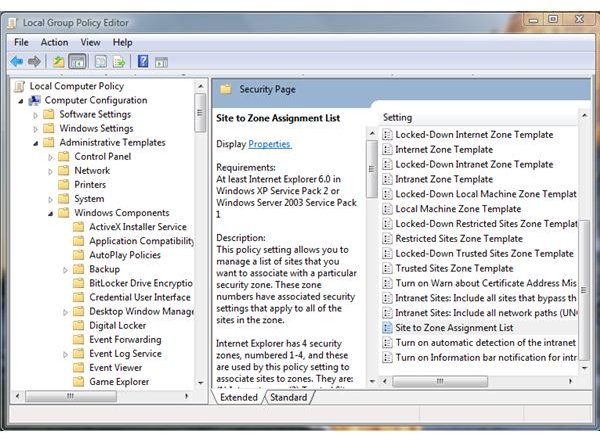
A non-home edition of Windows allows system administrators to access the group policy editor in Windows (type gpedit.msc in the run command to open the group policy editor console). The group policy editor includes a group policy object (GPO) to manage many settings in Windows, including the Internet Explorer component. To manage the trusted sites Internet Explorer group policy, navigate to the following:
-
For all users in the network: Local Computer Policy > Computer configuration > Administrative Templates > Windows Components > Internet Explorer > Internet Control Panel > Security Page. In the details page, double-click the “Site to Zone Assignment List”.
 Advertisement
Advertisement -
For the current user only of a single machine: Local Computer Policy > User configuration > Administrative Templates > Windows Components > Internet Explorer > Internet Control Panel > Security Page. In the details page, double-click the “Site to Zone Assignment List”.
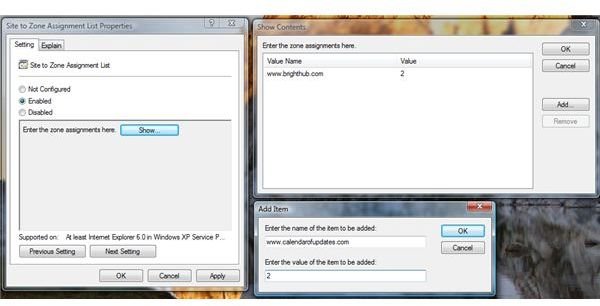
If the system administrator decides to use both or only one, any websites that they will add is automatically used by Internet Explorer. To add the trusted sites in one of the GPO for IE, select “Enabled” and then click “Show” button. Start entering the websites or IP address that IE will recognize as trusted sites. Note that you should not add https:// if you plan to trust all pages and protocols used by a website. An example is when you want to trust the Bright Hub website, simply enter www.brighthub.com so that all pages and protocols are trusted such as https://, https://, ftp://. Always enter the “2” value which means it is for the trusted sites security zones of Internet Explorer:
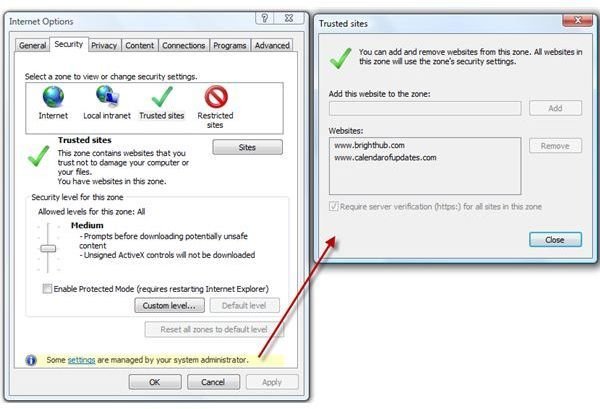
In the above example, you will see it is automatically applied in IE’s security zones for trusted sites and there is no way for the end-users to add or remove the list because it is managed by a system administrator using the Group Policy object editor in Windows:
Third-Party Tool to Manage Trusted Sites Internet Explorer Group Policy Object

If you often modify or manage the security zones in Internet Explorer by adding or removing a URL or IP address for the trusted, restricted or Intranet sites zone, you should consider using the free software , ZonedOut . With ZonedOut, you can import a list of URL or IP address from a notepad instead of entering one by one any URL or IP address. ZonedOut lets you add the trusted sites in any user hive: User or Local machine hives, which means for the current user or all users of a computer.
Image credit: Screenshot taken by the author.