Phishing has been in the news a lot over the last few years. A scourge of many internet users, phishing scams have swindled thousands. But the scams have an interesting and varied history, stretching back for many years.
Defining Phishing
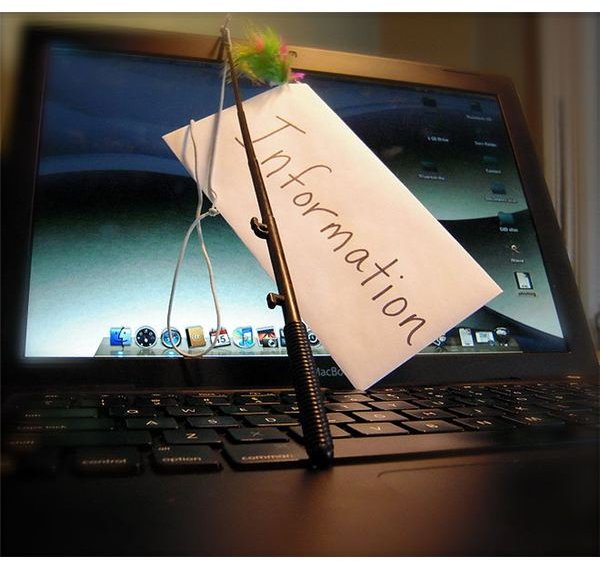
When examining the history of phishing, it is first vital to understand where the phrase comes from. Phishing is defined as “attempting to acquire sensitive information … by masquerading as a trustworthy entity in an electronic communication”. As a social engineering technique it’s a logical continuation of dressing up in a fake uniform to gain access to a certain area, or pretending to be a federal agent on a telephone call. But because of the multicast nature of email and other electronic communications, it is far simpler to find a target. To misquote Abraham Lincoln, “You can fool … some of the people all the time, but you cannot fool all the people all the time.” In practice there is little chance of the people operating phishing scams getting caught, and hence fooling some of the people they target brings in a perfectly adequate revenue stream.
The term phishing derives from the concept of ‘fishing’ for targets, sending out bait and seeing who strikes. The replacement of ‘f’ with the ‘ph’ phoneme comes from the practice of phreaking, or illegally exploring telephone systems.
Early Scams
The first exploration of the phishing concept came in 1987, at the Interex conference. Jerry Felix and Chris Hauck presented a paper called “System Security: A Hacker’s Perspective,” in which they discussed a method for a third party to imitate a trusted service. The first use of the term phishing is commonly attributed to the America Online newsgroup, and is closely related to the first commonly credited use of phishing techniques. Before 1995 it was possible to open an AOL account using a fake, algorithmically generated credit card number. However AOL caught on to this and clamped down, leading the active warez community on AOL to begin phishing for legitimate accounts. This was often done by sending an instant message to a user’s AIM account (which was linked to their AOL account), claiming to be a member of AOL who required their password. Tools like AOHell were developed to help automate this process, and for a while phishing was rampant. AOL soon devised countermeasures and by 1997 most phishers left for greener pastures. But the message “no one working at X will ask for your password or billing information” is still a common sight when opening many IM clients.
The Evolution of Attacks
Those phishing for AOL accounts soon realised that these phishing scams could be generalised to many other systems. Financial institutions in particular were seen as perfect targets. September 11th, 2001 marks an important date for the American psyche, but also an important date in the history of phishing. In the aftermath of the twin towers attacks, opportunistic criminals used an email asking for a ‘post 9-11 ID check’ to steal financial details from the E-Gold digital currency service. This was the second known attack. The first was a similar attempt against E-Gold taking place in June of that year. Both were initially seen as failures, but they helped to put phishing firmly on the radar of many criminal organisations.
By 2004 phishing was firmly established. Between May 2004 and May 2005 it was estimated that $929 million (USD) was lost to phishing scams. Since then a vast variety of different attacks and techniques have become common, including those highlighted below:
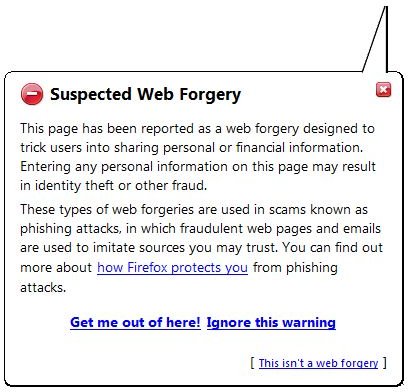
Link Manipulation: One of the earliest attacks was to send targets an email with a link to a misspelled or misleading domain, which looked identical to a legitimate site. The target is then tricked into entering their credentials. Over time this has evolved, with modern phishers making use of images instead of plain text in an attempt to avoid spam filters, and complex technical means to make websites seem identical to that of the targeted institution. A recent evolution of this is to direct the user to the legitimate website, and then make use of cross-site scripting flaws to display their own window over the top of the actual content.
Social Media: One of the major targets of phishing campaigns are social network sites like MySpace and Facebook . In 2006 a worm was used to alter links on MySpace , and direct users to disclose their login details. The mass of detailed information stored on social networking sites makes them a tempting target for phishing attacks, as they can be used for identity theft on a large scale.
Vishing: April 2006 saw an interesting development in the history of phishing, as phishing attacks were executed against targets outside the web. By using voice over IP (VoIP) technology, attackers were able to exploit public confidence in the land-line system by spoofing caller IDs. Automated messages claiming to be from a bank were used to extract the details of bank accounts and were dubbed ‘vishing ’, a combination of ‘voice’ and ‘phishing’.
Spear Phishing and Whaling: Spear Phishing and Whaling are both targeted phishing attacks, developed after a few years experience of running traditional phishing scams. Spear Phishing is designed to exploit information disclosed through other means, for example leaked usernames. Whaling is aimed at executive level users, where a single cracked account can lead to major information loss.
Tabnabbing: In May 2010, Mozilla Firefox’s creative lead, Aza Raskin, described tabnabbing , a new way to get users to enter their credentials into fake sites. If a user has a legitimate site open on one tab, it is possible to execute a JavaScript program from another tab to change the contents of that tab and hence trick the users into re-entering their credentials.
Anti Phishing Techniques
The size of losses caused by phishing is debatable. A 2007 Gartner report indicated losses of $3.2 billion (USD) to phishing scams in 2007, while Microsoft claims that this may be overstating losses almost 50 times . What isn’t in doubt is that anti-phishing countermeasures have been evolving almost as fast as phishing attacks themselves. In the second part of this series we explore the technical and social methods undertaken to stop phishing.
Image Credits
Both images courtesy of Wikipedia Commons
https://commons.wikimedia.org/wiki/File:Phishing.JPG
https://commons.wikimedia.org/wiki/File:Firefox _2.0.0.1_Phising_Alert.png