Curious about what applications under Linux can help improve your computer privacy? Find out what you can use to anonymously surf the Internet, send government-strength encrypted messages and maintain your privacy in the world of social media.
Privacy
Privacy as a concept has largely dissipated in our modern culture. People post every detail of their lives on social networking sites and provide companies with boundless amounts of advertising information. When attempting to regain your privacy in the Internet age, there are two areas that need to be observed: anonymity and encryption. Anonymity can make tracking your online movements impossible for advertisers, keeping your personal information safe. The art of anonymity encompasses not only using anonymizing proxies or virtual private networks (VPNs), but also being mindful of what information your computer is sending and receiving when interacting with a web service. Encryption on the other hand can help you keep private messages what they ought to be, private. The purpose of encryption is not to necessarily mask the participants, but to obscure the message. Both sections can be divided into remote and local privacy techniques. Since many privacy advocates use the free and open source Linux operating system, there are many tools to facilitate both anonymity and encryption in day-to-day computing on a Linux desktop.
Remote Anonymity
Your home network or computer announces and maintains its identity via IP address, a 32-bit decimal code uniquely assigned to your machine by your Internet service provider (ISP). The general practice of digital anonymity on the Internet involves ways of obfuscating and hiding your actual origin IP address. This can be done using free software like The Onion Router (TOR) or another anonymizing darknet that masks and distributes your traffic. Commercial proxies and VPNs are also available for subscription and can be enabled in all Linux web browsers, but may not be as reliable as a distributed solution since the provider still has access to all of your information. Furthermore, applications like Privoxy, the privacy enhancing proxy, can be used in conjunction with TOR and other services to filter and anonymize your traffic. Any application that allows proxies can be funneled through a proxy service like Privoxy.
Local Anonymity
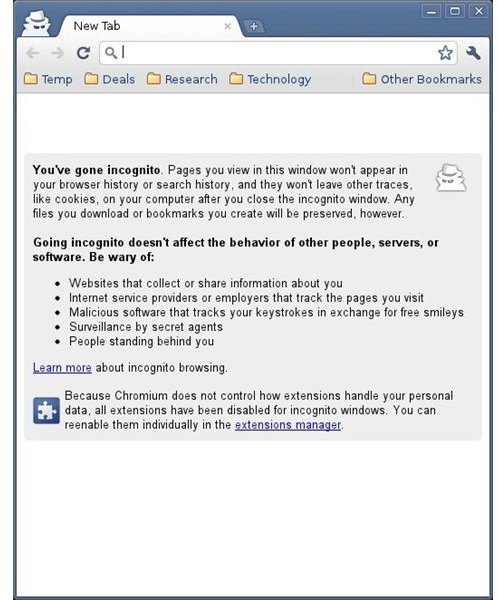
Locally, anonymity can be maintained by disabling both cookies and Javascript in any Linux web browser. Cookies are used to track
sessions and users as they move across the Internet and are distributed by every major website. They are a part of how the Internet maintains logged in users and facilitates commercial traffic. By disabling Javascript you remove the ability for the website to use cross-site scripting (XSS) attacks to execute malicious code in your web browser, often with the aim of acquiring account information. Finally, browser history can be deleted to maintain immediate privacy. Mozilla Firefox and Google Chrome, both major web browsers, now contain a private browsing or icognito mode that will purge your machine of all the above data once the window is closed.
Remote Encryption
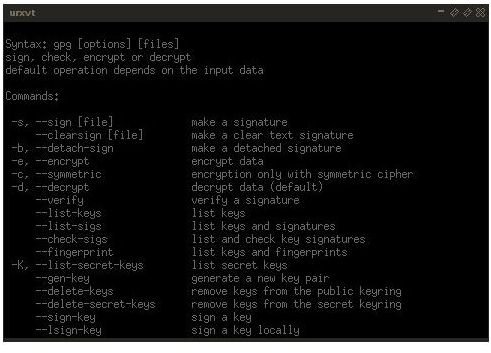
Linux really shines when it comes to encryption implementations on the desktop. The popular GnuPG implements the public key
cryptography PGP standard for free on the Linux desktop and comes with a number of front ends for key management. Linux e-mail clients like Mozilla Thunderbird and Claws integrate with GnuPG to provide secure communication through e-mail. Additionally, GnuPG can be used to encrypt local files with your own public key. For securing instant messaging (IM), the freely available Pidgin cross-platform IM client supports Off-the-Record (OTR) encrypted messaging, an implementation that can be thought of as a rolling encryption key. Finally, like all web browsers, Linux-based application platforms support secure socket layer (SSL), an encrypted form of web traffic. Although web browsers are the most commonly used tool to utilize SSL, Internet Relay Chat (IRC) communication clients such as Irssi and X-chat, both popular on Linux, use SSL as well. Browsers like Mozilla Firefox provide extensions that force continuous SSL, also known as HTTPS, on websites that support SSL connections.
Local Encryption
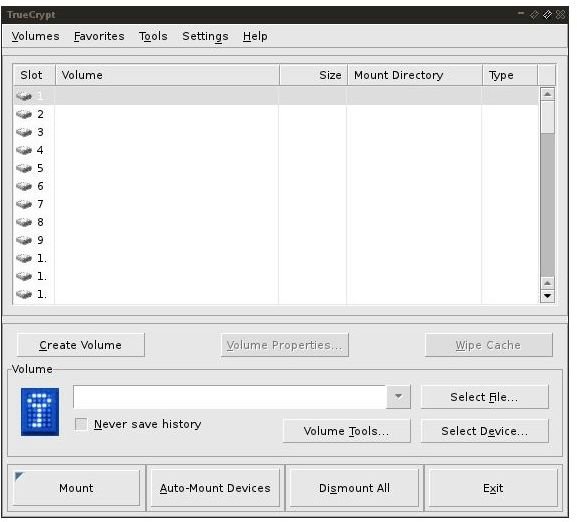
For local privacy, LUKS with dm-crypt and TrueCrypt can be used for hard disk and removable drive encryption . All three offer a number of ciphers that use government-grade encryption to maintain privacy and each offers its own advantages. SSH , a tool that can fit both local and remote anonymity and encryption, can be used to provide an encrypted, secure tunnel to any machine running an SSH server. This can be used to maintain local privacy by circumventing restrictive and invasive firewalls or for remote privacy by forwarding a remote port for another machine.
Resources
Claws - https://claws-mail.org
Dm-crypt - https://www.saout.de/misc/dm-crypt/
GnuPG - https://gnupg.org/
Google: Linux Unified Key Setup (LUKS) - https://code.google.com/p/cryptsetup/
Irssi - https://irssi.org/
Mozilla Thunderbird - https://www.mozillamessaging.com/en-US/thunderbird/
OpenSSH - https://openssh.com/
Privoxy - https://www.privoxy.org/
Tor Project - https://www.torproject.org/
TrueCrypt - https://www.truecrypt.org/
X-Chat - https://xchat.org/
Image Credit: Screenshots by the Author.