Did you know that it is possible for a malicious hacker to fake an SSL certificate and pipe your encrypted traffic through their machine, stripping out your personal information along the way? Read on to find out what you should do if your browser announces an insecure SSL certificate.
SSL Certificates
The Internet was not originally built as a secure environment. Early developers looked more for stability and uptime then they did secure protocols. For this reason, much of the modern Internet revolves around insecure communications and traffic, leaving anything and everything you send and receive open to the public.
Secure Socket Layer (SSL), sometimes referred to as HTTPS, was a way to provide a secure connection for the exchange of information over the Internet. SSL uses public key encryption to ensure a secure environment and essentially creates a tunnel layer through the old, insecure Internet protocols. The one catch with SSL certificates is that just about anyone can create and sign them, allowing any hacker to come between you and your secure connection, fake an SSL certificate, and mediate your encrypted session in plain text.
Enter Certificate Authorities
Certificate Authorities (CAs) are a sort of solution to this problem. Several companies decided to form a coalition where they would
provide signed and verified SSL certificates to websites. The problem with this is that they charge large amounts, depending on your website’s traffic, so unless a website makes a large amount of money, they have to use an untrusted self-signed certificate.
Essentially, signed and verified certificates from a trusted CA do not show a popup window in your web browser, producing a seamless encryption experience. This means that many websites, choosing not to use CAs because of their price, have gotten users used to clicking the “Allow” button and simply moving through an untrusted certificate.
This negates the entire goal of the CAs and SSL certificates in general because it makes a man-in-the-middle (MITM) attack very easy.
Even More Problems
Since SSL certificates are typically used to encrypt and secure things like banking transactions, online shopping, and other areas where sensitive personal information is exchanged, the temptation to find weaknesses was a strong one for attackers. Commonly, an SSL connection produces a small lock symbol at the bottom of the page.
This is called a “favicon” and is used to denote that you are using a secure connection. Originally, when using the MITM attack, hackers and security researchers alike were unable to make the SSL favicon appear.
However, with more research, it quickly became apparent that this favicon could be faked to provide a seemingly encrypted experience for the user. This has since been implemented into a number of security tools, provided seamless-looking encryption when really there is none.
What You Should Do
When you come across a bad SSL certificate there are one of three things that could be happening: the SSL certificate has timed out and the website has not renewed it with a CA yet, you are seeing an untrusted self-signed certificate, or you are seeing a self-signed certificate produced by a MITM attack.
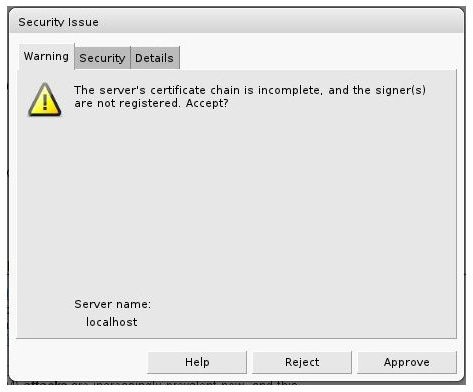
The first thing you should always do is take a look at the certificate’s date and the issuer information. If the certificate comes from a CA, the company information matches the website you are viewing, and the renewal date is passed then you can safely click the “Approve” button. If the certificate announces itself as self-signed and all of the contact information matches the credentials of the website you are viewing, then you can safely click the “Approve” button.
However, if you have used that website before in the past and there is no mention of them changing their self-signed certificate than you should be wary of your connection, especially if you are on a public network.
Finally, if you are on a public network and you are visiting a major website, like Facebook or Google Mail, and you receive an SSL certificate where the information does not match the website you are visiting, your connection is being intercepted and stripped of encryption. The only thing you really can do is close your web browser and access the website from a more secure, private location.