When talking about cloud computing security issues, there are several factors that may endanger your data on a cloud. Compared to an on-premise server, cloud security is more promising. Still, there are some issues that need to be assessed and that’s what we’ll talk about in this article.
Cloud Computing Security Issues - Cloud Security and DDoS
Before talking about different cloud computing security issues, let me ask you a question. Why did Wikileaks turn to cloud computing in the year 2010? While hacking is the primary issue among cloud computing security issues, distributed denial of service (DDoS) is one of the aspects that is still far below the reach of clouds. When Wikileaks started leaking important diplomatic cables toward the end of November 2010, some agencies started directing “denial of service attacks” to the on-premises hosting servers to bring the site down. This is when Wikileaks turned to cloud security.
As cloud security is more powerful when it comes to DDoS, Wikileaks turned to Amazon Cloud Computing . It is a different issue that Amazon refused to host the website saying it can’t risk the data of other clients. Following this, supporters of Wikileaks offered it mirror servers so that the site is now hosted from more than 200 places, most of them being cloud.
Politics apart, you may be wondering about DDoS. Distributed Denial of Service (DDoS) is a type of intentional, targeted attack that disrupts the normal functioning of websites. While it is very easy for hackers to target and direct as many DDoS attacks to any service provider using traditional infrastructures, the cloud security measures make it difficult for them to bring down the cloud.
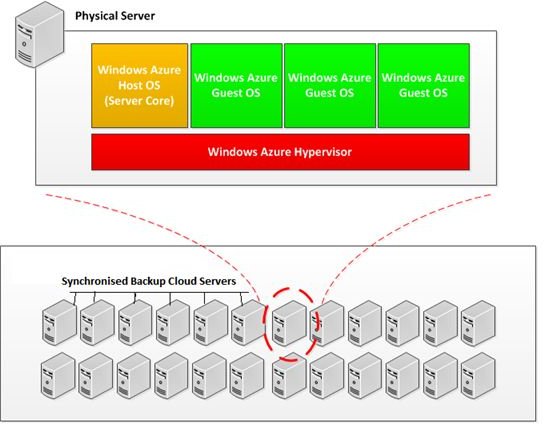
Though not impossible - the probability of DDoS attacks bringing down a cloud is far less when compared to traditional infrastructures. This is because clouds have resources such as emergency backup servers that always sync data. If one server is down, data would be rerouted through the backup servers so that the service is not interrupted. Please note that most clouds, including Microsoft , keep both the original and backup servers synchronized in real time so that users can always access the latest information (see image-click to enlarge).
Image Courtesy: Wikimedia Commons .
Authorized and Unauthorized Access - Cloud Computing Security Issues
Among the serious cloud computing security issues is - access to data. I call it serious because while authorized people can always access the data, the cloud service provider can also access it. That’s a cloud security breach, if it happens without the client’s permission. The third type of access is unauthorized access by third parties. Hackers, in the context of cloud security, are people who are on lookout for confidential data that they can use for personal gains.
I won’t say that only the last two types - cloud service provider and hackers - are the only issue. Your own authorized personnel can misuse the data.
This does not mean that you should not trust your employees. There are cases of social engineering where external people befriend your employees and try to obtain data even as the poor employee is assuming that s/he is helping a customer. You need to train your employees to help them avoid falling prey to such tactics.
First of all, you need to have a policy that checks who is accessing the data and what actions are being performed on the data. Using logs will not only help you identify malicious authorized personnel, they also show you unexpected attempts to access data by third parties - the cloud service provider or any hacker. Based on these logs, you can create and modify your cloud security policies.
Note: It may also happen that hackers could target the log files so that no intrusion attempts are recorded. This aspect should be taken seriously while creating your own cloud security policy. It is not a good idea to depend just on the security policies of the service provider.
In short, you should consider a cloud security policy before opting for any computing package. This policy should cover possible cloud computing security issues. It is always better to spend some time researching different cloud issues so that you are prepared.
This concludes my observations of cloud computing security issues. If you wish to add anything, please share it using the comments section below.