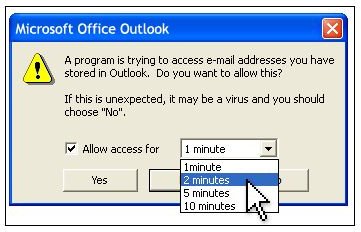
“A program is trying to access e-mail addresses you have stored in Outlook”, “a program is trying to automatically send e-mail on your behalf”, “a program is trying to access email address information stored in outlook” are common dialogs displayed by Microsoft Outlook.
Why Block Access to Outlook Contact List?
Much of the malware in the Internet spreads by accessing your address book and sending itself to your contact list. This process forced Microsoft to apply security measures to its popular e-mail client, Microsoft Outlook. On the other hand, it is not possible to block access to the Outlook contacts totally: imagine that you would not be able to synchronize your mobile phone with Outlook.
Although I criticize the security applications of Microsoft, I think this one is an exception, but it is not perfect. The application that wants to access to your contact list may be a malware or a regular device-synchronizer. Logic dictates that if you receive the warning after you start your synchronization software, it is OK to allow access to Outlook. But what if the malware is triggered with such an event? Let’s say that the malware is coded to intercept the program’s access to Outlook and wait for user’s permission and when the user allows the program, the malware will gain access to the contact list. Seems improbable? I don’t think so. Therefore, I would rather see which program is trying to access the Outlook contacts, not a simple permit/deny message.
But, Microsoft is trying to implement its own safety measures here. Microsoft says that users who receive such a warning are using programs that fail to identify themselves as safe programs to Outlook. This may be the case, but frankly I do not expect Microsoft Outlook to identify all the mobile phone manufacturers’ software correctly.
How to Allow Access?
When you see the dialog in the message window asking whether you want to allow the program to access Outlook data, just think: is it anticipated? Does the message appear after you have started a program? If you are sure, allow. If not, deny. It is that simple. But no, you can not stop Outlook from displaying this message.
Solution?
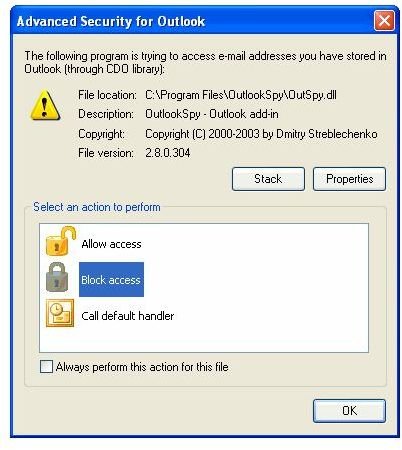
With all the discussion above, I can recommend you to give Advanced Security for Outlook a try, which is free for both commercial and personal use. It is exactly what I have in mind; it shows which file is trying to access Outlook and it also shows the stack if you want. Checking out the stack you can see the full path of the program and its description which is trying to access Microsoft Outlook data.