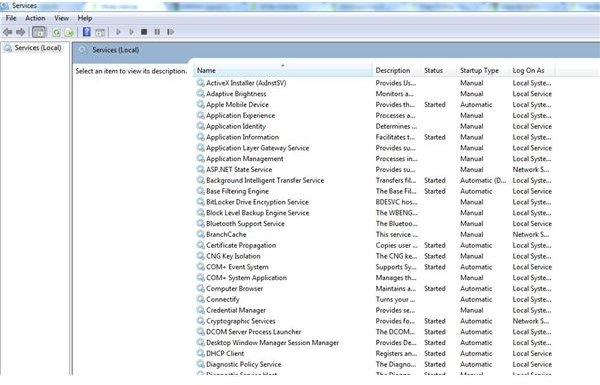
Service hardening protects the system services that run in the background, usually with high administrator rights, which makes them a target for malicious software attacks. Viruses and worms all target system and restricted services and service hardening fights this.
Security in Windows Vista and Windows 7 has been engineered to support technologies that assist non-Microsoft developers to construct more secure code and provide additional protection for the operating system kernel from the malicious intent of malware software.
Window Service Hardening is a concept that has been designed to mitigate the effect of malicious software attacks, like the Slammer, Blaster and Sasser worms, which all target system services on a computer system. System services are background processes always running in the background to support important functionality in your operating system. Their importance means they usually run with high system rights, which makes them a prime target for individuals who want to take key control of important parts of your system, hopefully without you being aware of it.
We will be discussing the ways in which Microsoft has improved security, their latest operating systems, and exactly what these improvements are and how they work.
Protection
In Depth Protection – Malicious software is often designed to take advantage of buffer overflows on a computer system and use inherent weaknesses in the system to install overtly themselves onto a system. Essentially they trick software into running code that they have secretly placed in areas set aside to store data on the computer.
A good way to decrease the possible problems associated with individuals taking advantage of these weaknesses is through the use of no-execute technologies (NX) at the hardware level of the system. NX gives software the ability to mark specific sections of the system memory as being just for data, so the processor will stop applications and services from carrying out any code stored in there.
Microsoft has provided protection for no-execute technologies (NX) since Windows XP SP2 through the Data Execution Prevention feature.
Windows now has Address Space Layout Randomization (ASLR), a defense feature in Windows Vista and Windows 7 that makes it more difficult for malicious code to take advantage of a system function. ASLR randomly assigns executable images to one of 256 different places in memory; this in turn makes this activity more difficult for the malicious code to find and use the functionality inside the executable images.
Microsoft’s Built in Protection
Microsoft has also designed Heap buffer overrun detection into Windows Vista and Windows 7. It is always working in these systems to protect operating system components. It includes built-in system services, and works even better than code that originated in Windows XP SP2. If Windows Vista or Windows 7 detects signs of heap-buffer tampering, it will terminate the affected software, stopping any additional damage that might be done.
Anti-Virus Protection and Patch Management
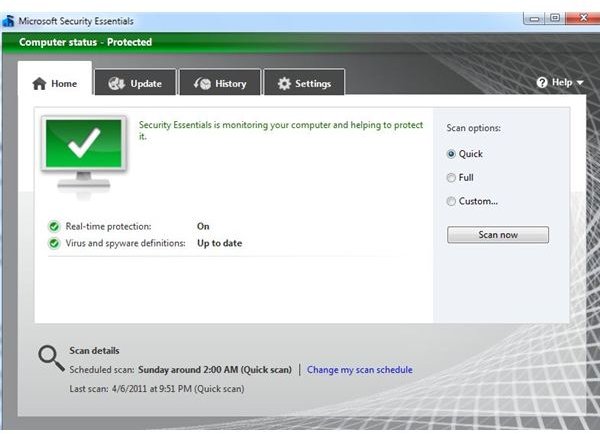
To keep malicious code from having a direct effect on Windows services, the end user should use an anti-virus such as AVG, AntiVir, Avast , McAfee , Microsoft Security Essentials or Symantec’s Norton. Immunet can be run with other anti-virus programs . Anti-Virus programs help to prevent services from being changed and protect your valuable data.
The second methodology of protecting your computer and preventing these changes is simple. It is important to keep your computer up to date by getting all of your updates, patches and service packs. As malicious programs are found, Microsoft produces updates for their operating systems.