Windows Group Policies can be an extremely powerful means of tracking employee logon times. This article will show you how to enable logon auditing using a Windows Domain and Group Policy Objects (GPO).
Getting Started
This article assumes you have a basic working knowledge of Microsoft Group Policies. If you need to catch up on Group policies, I’d suggest starting with these articles. Please note that if you are not completely comfortable working with Group Policies, you may want to set up a test domain so you can play around without any great consequence. There’s nothing worse than trying to make a simple Group Policy change only to make a mistake and criple your entire domain.
- The Basics of Group Policy in WIndows Server 2003 Network Environments
- Group Policies for Functional and Secure Server 2003 Networks
There are several steps to take in order to properly audit logon times for your end users.
- Enable auditing in your policy
- Assign computers to the policy
- Verify computer have received the policy
- Monitor event logs for events
Enable Auditing
In this section, we’ll walk through setting up a new policy and configuring it to audit logon events.
- Start the Group Policy Management Console. You can find it here if you don’t already have it installed.
- Browse to the following location - Forest:Domain Name-->Domains–>Domain Name-->Group Policy Objects, replacing “Domain Name” with your domain.
- Right-Click on Group Policy Objects and select New.
- Give your policy a name and click Ok.
- Expand the Group Policy Objects folder and find your new policy. Right-click on the policy and select Edit…
- Browse to the following location - Policy Name-->Computer Configuration–>Windows Settings–>Security Settings–>Local Policies–>Audit Policy. Left click on Audit Policy. The policy settings will be displayed in the right-hand window.
- Double click on “Audit account logon events” and select “Success” and “Failure”. Click Ok.
- Double click on “Audit logon events” and select “Success” and “Failure”. Click Ok.
- Close the Group Policy Window.
The difference between the two policies is that “account logon events” are tied to the domain - it’s when a user authenticates to a domain controller. These logs will be displayed in the Security event log for the domain controller. The other policy setting, “logon events”, will track the user accounts authenticating to the local machine. These events will be stored on each individual computer’s Security event log.
You’ve now successfully set up a Group Policy.
Assign Computers to the Policy
Next, you’ll need to ensure computers have the policy applied to them. We will be assigning the policy to an Organizational Unit (OU) containing the computers we wish to have under the policy. An Organizational Unit is really just a folder that contains various Active Directory objects. In this example, the OU will contain our computers.
- Make sure you’re still in the Group Policy Management Console.
- Find the OU you wish to apply the policy to. Right click on the OU and select “Link an Existing GPO…”
- Select the newly created policy and click Ok.
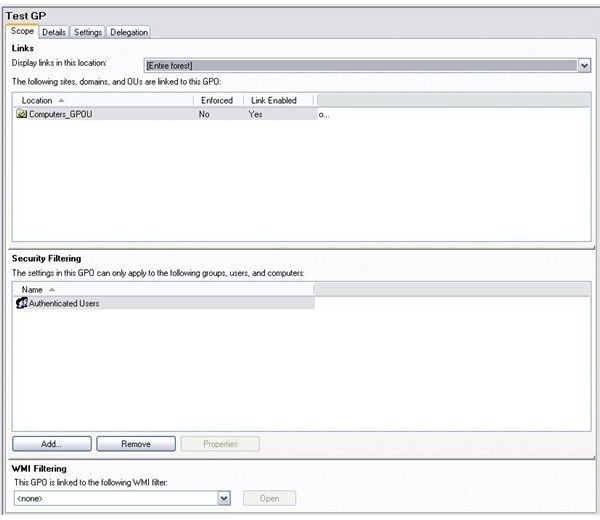
- Click on your policy and you should now see the OU that it is linked to as shown in the picture below.
Verify the Computers are Under the Policy
After applying the policy to an Organizational Unit, the computers under that OU will start to accept the policy over the next several hours depending on the size of your network.
You can force a manual policy refresh by using the built in command Windows command “gpupdate”.
- On a workstation the policy should be applied to, open up a command prompt and type “gpupdate /Force /Boot”. This will apply the policy and reboot your computer.
When Windows comes back up, you will want to verify the policy is being applied to the workstation.
- Go to a command prompt and type “gpresult”.
After a few seconds, you will be presented with a list of applied policies. Make sure the newly created policy is listed.
Monitor Event Logs for Events
After your computer has rebooted you will want to verify that the auditing is working.
- Open up the Security Event Log by going to Start → Settings → Control Panel.
- Double click on Administrative Tools.
- Double click on Event Viewer.
- In the left-hand pane, click on the Security event log. You should now see several events appear in the right-hand pane.
When looking for logon times, you will want to look under the “Event” column for 528 (or 4624 for Windows Vista). You can then double click on the event and you will be able to see the date, time and user who logged in.
As you can see in the picture below, the user that logged in was “Administrator”. The user logged in at approximately 8:26pm on 02/10/2009.
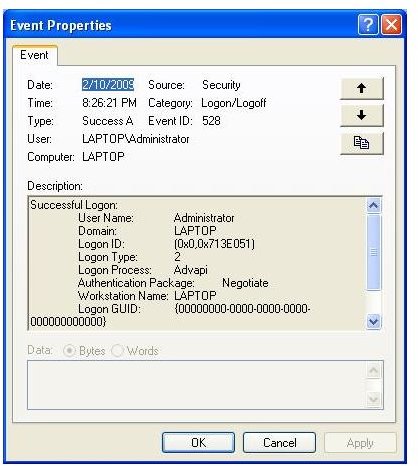
The other interesting piece of information you can glean from the event log is the type of logon - was it someone unlocking your machine, logging in remotely, or logging in directly at the console? In the screenshot below, you can see the logon type was “2”. Using the table below, you can see this type of logon corresponds to a logon at the console.
Common Logon Types:
2 - The user logged in at the console
7 - The user unlocked the computer
10 - The user logged in remotely - via Remote Desktop or Remote Assistance
11 - The user logged in while using cached domain credentials.
This post is part of the series: Auditing Windows Logon Events using Policies
This series walks home users and small\medium businesses through setting up security event auditing to monitor user account logon details using built in Windows XP, Vista and Windows Server tools.