One of the actions by Trojan horse is by modifying settings in Windows. An example is by hiding itself or the location where it’s hiding. If folder options in Windows shows hidden files and folders that won’t change, a Trojan virus may need to be removed.
Actions by Trojans
Most malware and Trojan horses have one thing in common when they succeed in infecting Windows, Mac or Linux operating systems, and that is to steal personal and valuable information. They log or record the activity on the computer when browsing, playing games, chatting or any computing activity that uses login credentials. Note that some Trojans targets online banking activities only while others will target specific online games.
When a Trojan is executed, it performs some actions on the operating system and starts to infect the computer. The actions by Trojans may vary because there are several types of Trojan horses . In most cases, they will add as startup item, install a rootkit which is a hidden file, and add a value in the Winlogon registry keys so that it will load as soon as Windows loads the desktop–and then attempt to make a network connection to the attacker’s location.
Another action by some Trojans is to modify current settings in Windows such as changing the desktop background, disabling access to important utilities in Windows [Task Manager, Startup Configuration (MSCONFIG) and Registry Editor], disable antivirus and firewall protections, inserts browser add-ons, hijacks the home and search pages, and changes the settings on how files and folders are displayed by hiding where the Trojan adds itself.
Hidden Files and Folders
When Trojans modify the way Windows displays the file and folders, it only means that the registry keys were set as:
- [HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced] “Hidden” = 2
- [HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\explorer\Advanced\Folder\Hidden\SHOWALL]“CheckedValue” = 0
An example of Trojan infection that modifies the settings to show or hide folders is Trojan OnlineGames , which is a password stealing Trojan, and sends the logged or recorded information to the attacker’s computer.
Hidden Files and Folders Won’t Change - Trojan Virus Infections
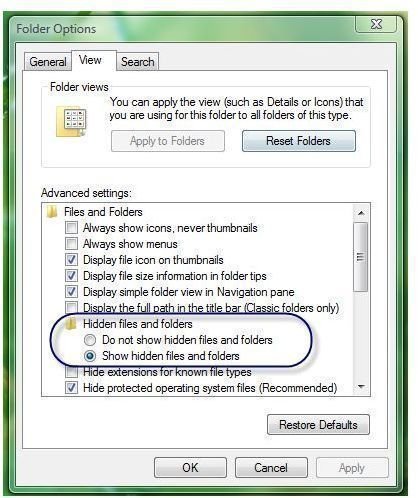
People may recommend to manually change the settings in Windows to show hidden files and folders to be able to view the location of the Trojans:
However, if the hidden files and folders won’t change–Trojan viruses control the system by reverting changes made by the computer user, there is no other solution but to try accessing the above-mentioned registry keys using Registry Editor in Windows, and then change the value to:
-
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced] “Hidden” = **1
Advertisement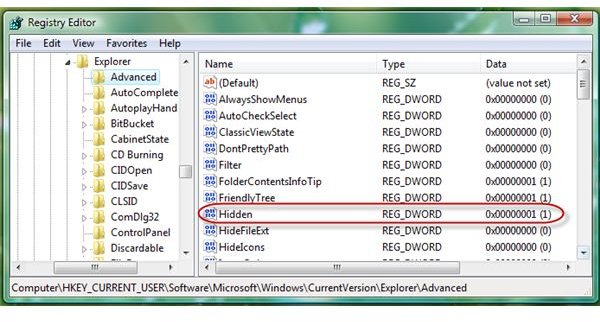 **
** -
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\explorer\Advanced\Folder\Hidden\SHOWALL]“CheckedValue” = **1
Advertisement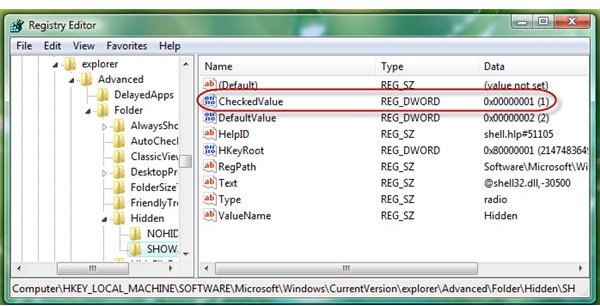
**
Advertisement
Another solution is to run a scan using anti-malware, antivirus or anti-Trojan programs. If the installed anti-malware can’t detect or remove the infection, the end-user should try using an online scanner such as BitDefender online scanner , Trend Micro Housecall , or ESET online scan .
It is also important to note that in some cases; restoring the computer to previous state using System Restore in Windows may help get rid of the infection, in addition to recovering the system settings back to normal. Other methods of system recovery can be found in the article “Will System Recovery Eliminate Trojans, Viruses, and Malware?”
Image credit: Screenshot taken by the author.