Winlogon is the common target of several types of malware. If the malware succeeds in modifying the Winlogon’s Shell and Userinit processes, the computer requires a clean-up and Winlogon Trojan removal–learn the simple steps for doing this on your own here.
Winlogon and Malware
Winlogon is a legitimate component in Windows operating systems that handles user interface (the desktop), user account login (Windows logon screen), and other commands that interact with the user or load to perform an important task. Winlogon registry keys can be found in the following locations:
- HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon
- HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon
The above registry keys contain a Shell and Userinit registry values. Shell entry loads the desktop and allows the user to interact. Userinit loads user profile settings e.g. your profile settings, fonts, and colors. In some cases, the Winlogon also contains other tasks such as passwordexpirywarning and forceunlocklogon, which means the current user, is notified when the password for Windows expires and allows logon without a password. Such entries are not malicious because Winlogon may or may not contain additional programs to load or run, that are safe or unsafe.
Malware often takes advantage of the Winlogon component in Windows by adding itself in the Shell and Userinit values so the malicious file will load right after the user logs into Windows, and when the desktop has loaded.
Example of Winlogon Trojans and Malware
Below are some examples of malware that uses Winlogon to load their malicious software or file after the user logon and once the desktop has loaded:
- Trojans with rootkit capability that will cause Google Redirect Virus .
- Trojan DNS changers that cause a Google popup virus in Windows and Mac computers.
- Fake or rogue antivirus programs e.g. Fake Microsoft Security Essentials Trojan alerts.
- Other type of Trojans e.g. Win32 Agent which is a Spy Trojan, Vundo Trojan and Zeus Trojan .
- Autorun worms .
Winlogon Trojan Removal
Most antivirus, anti-Trojan and anti-malware programs will scan the registry in Windows for malware. The scanners are designed to check the registry for any values that should not be there. However, some antivirus scanners will fail to fix the Winlogon registry key after they finish removing the malicious files that are located somewhere on your hard-disk e.g. in Documents, System and Program folders.
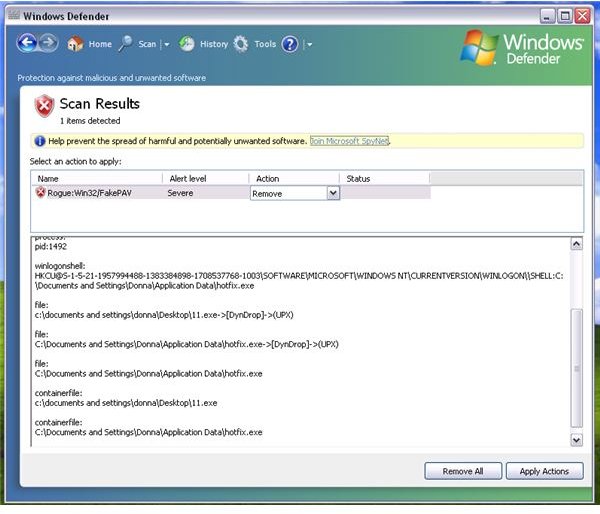
If your antivirus program has detected and removed spyware, Trojans, worms, fake alerts, rogue antivirus, worms, and other types of malware, it is a good idea to manually check the above-mentioned registry entries for Winlogon in Windows. Advanced users should have no problem identifying the malicious path or values in the Winlogon registry keys. For end-users that prefer automatic checks on Winlogon registry, you should use on-demand scanners that will scan not only the files on the computer but also the memory and registry. An example of an on-demand scanner is Windows Defender that scans Winlogon and then fixes by removing the winlogon Trojan path.
Standalone scanners that were developed to remove specific malware infections will automatically scan Winlogon registry keys. An example of these scanners are Stinger by McAfee, TDSSKiller by Kaspersky, Windows Malicious Software Removal Tool by Microsoft, or other scanners that only remove a few sets of malware .
Advanced users who prefer to remove Winlogon Trojans should simply navigate the specified registry keys of Winlogon, and then right-click Shell or Userinit to delete them. Windows will automatically load the default Shell and Userinit when the computer is restarted. It is important to remember that you should only delete the Userinit and Shell registry values, but do not delete the Winlogon registry key which is at the left pane. Doing so will cause nothing but trouble, Windows may not logon or boot properly if you mistakenly delete the Winlogon registry keys that are located in HKEY_LOCAL_MACHINE and HKEY_CURRENT_USER registry hives.
Normal and safe mode boot options in Windows allow you to access the registry editor in Windows, to modify, add or delete offending and malicious entries and proceed with the Winlogon Trojan removal method. Be sure to backup Windows registry before modifying it because it can cause damage instead of fixing, if you mistakenly delete a key or value.
Image credit: Screenshot taken by the author.