Learn how to get rid of spyware infection if antivirus or anti-spyware does not detect spyware or malicious activity in your computer. Find out how you can determine if a computer does have a spyware infection.
Free Spyware Removal Guide
Removing spyware that is detected by antivirus or anti-spyware program will not give the PC user a headache. Spyware removal programs will automatically remove the files, processes or drivers installed by spyware application. This is the reason an antivirus or anti-spyware tools should be kept up-to-date, to receive new and improved detection signatures for known spyware or malware.
If you have become a victim of a new spyware program that is not yet detected by antivirus or anti-malware software, your options is to try another scanner or manually remove the nasty and new spyware application. Find out more in this elimination free spyware removal guide on how you can clean computers that have nasty or new spyware.
Symptoms of Spyware Infection
There are several symptoms to determine whether a computer is infected by a spyware program. The first thing you will notice is the slow performance of the computer. The boot-time or shutdown timing is longer than the normal boot and shutdown process in Windows. In some cases, the desktop background is modified or hidden.
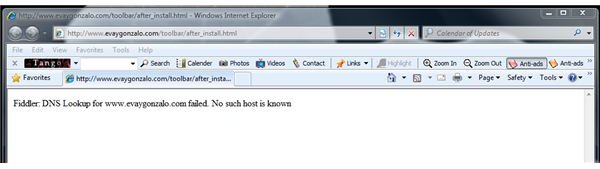
Most spyware program will modify browsers’ search and home pages. It can also redirect web-search results to unwanted websites. The default hosts file in Windows is sometimes modified or hijacked by spyware to prevent end-users visiting legitimate websites. DNS servers and Internet connection settings can be hijacked as well. Toolbars are also added in Firefox or Internet Explorer browsers.
Other computers that are infected with spyware programs will no longer boot in normal mode. This is true if the spyware program also installed other malware such as a rootkit, Trojans or another spyware application.
Removing Spyware Using Free Spyware Removal Tool
It is known to the security community that there is no single malware scanner that can detect all types of threats. This is because new malware is created, modified and distributed every day.
Often, the malware and spyware distributors will release a new version to prevent detections by antivirus and anti-spyware tools. They are actually using online virus scanners such as VirusTotal or Jotti online malware scan services to find out which antivirus software will detect the malware sample. It is easy for them to know if there are plenty of malware scanners that will fail to detect and remove the new variant of malware or spyware.
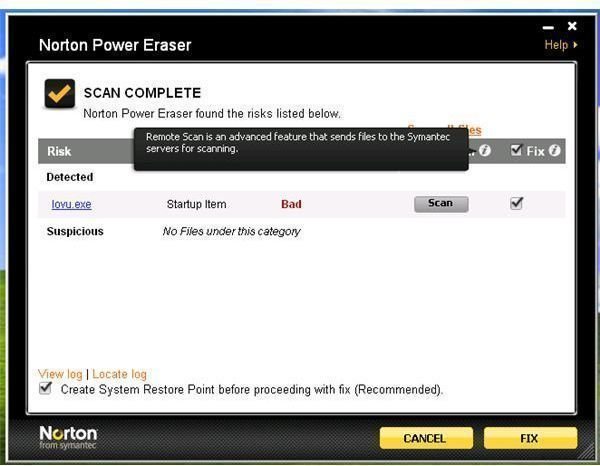
If your computer is showing the symptoms of spyware infection but the antivirus and anti-spyware is not detecting malicious or spyware activity, you should scan the computer using other spyware scanners.
If the browser is not hijacked and you can use the web browser to download new spyware removal tools, proceed to downloading the following programs. Install and update the scanners before running a quick scan.
However, if the browser has been hijacked or the computer could not connect to the legitimate websites, you need to use another clean PC to download the programs. Save the files to a removable device; e.g. USB or flash drives. Run the installer of the malware scanner in the affected computer from the USB or flash drive.
When the computer won’t boot to normal mode, you can try using other boot options: Safe Mode or Safe Mode with Networking. The above spyware scanners run on Safe Mode but booting to Safe Mode with Networking is necessary to update the detection signature or program.
If none of the above applications will detect the spyware infection, you should consider downloading HijackThis tool. HijackThis is not a spyware scanner, and it will not detect good and bad files in your computer. Learn how to use HijackThis in removing spyware in this article . Note that if you are not comfortable in using HijackThis tool or manually removing spyware, it is best to visit free malware and spyware removal forums such as Aumha.org or BleepingComputer.com .
Image credits: Screenshots taken by the author, https://upload.wikimedia.org/wikipedia/commons/f/ff/Malware _logo.svg By Skull_and_crossbones.svg: Silsor Computer_n_screen.svg: Everaldo Coelho and YellowIcon derivative work: Kizar (Skull_and_crossbones.svg Computer_n_screen.svg) [LGPL (www.gnu.org/licenses/lgpl.html )], via Wikimedia Commons.



