Looking for a vulnerability scanner that will do the job, yet not burn through your limited budget or resources? Look no more. Check out Nessus or Nmap. Both have capabilities, but one is better than the other. Nessus vs Nmap - which one to use?
Introduction
Before the advent of tools like Nessus or Nmap, network and server administrators manually checked their network and servers for vulnerabilities. “Manual” means that they used their command console or TELNET to do some basic vulnerability scans. Over time, they started using scripts to automate this, then collections of scripts to make their jobs even easier. SATAN (Security Administrator Tool for Analyzing Networks) was an example of such a collection of scripts released in 1995. Then people figured out that they can make big money from this; they packaged a set of tools, and started charging thousands of dollars for it. Some commercialized products included:
- NetSonar Vulnerability Scanner (by WheelGroup Corporation)
- Internet Security Systems’ (ISS) Internet Scanner
- NETECT’s Netective Suite
- Secure Networks’ Ballista Security Auditing System
Others continued on with their own development on the open source side of the isle. Nmap was released in 1997, and Nessus followed in 1998. Both were released as open source, free solutions. Nessus became proprietary in 2005, but it continues to be freely available for personal use.
About Nmap
Nmap (Network Mapper) was released in September 1997. Its primary purpose is network discovery/mapping by facilitating the discovery of hosts and the services that run on them. Network administrators and security professionals use it to map out their networks, as well as to determine the following:
- The up or down status of a host
- Presence of unexpected hosts
- Presence of unexpected services
- Network services available on a host
- Type of host
- Presence of a firewall
- Operating system and version used on host
- Name and version of services running on host
Nmap used to be 100% command line, requiring some strong familiarity with its vast options to fully utilize it. However, a user interface was developed for it–called Zenmap --making it more intuitive to use.
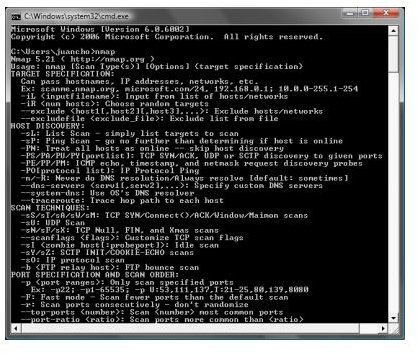
Note that Nmap by itself doesn’t tell you the existence of vulnerabilities on a system. Between the scanning results, your knowledge of computer networking, and your knowledge of your network baseline, you may be able to figure out what vulnerabilities exist, address these issues, and improve your security posture. To this end, other utilities were added to Nmap to help improve its capabilities–namely Ncat (the utility knife for sending or receiving data to an application connection) and Ndiff (shows delta between scan results).
To a large extent, it is an excellent tool for a hacker. The reason being is that it allows one to figure out the network “lay of the land”. Once the “lay of the land” is clear, all it takes is to figure out known vulnerabilities in discovered operating systems or services, and the network is basically breached.
About Nessus
Nessus was released in 1998. It was initially developed as a free remote security scanner but later became proprietary when Renaud Deraison–the developer of Nessus–co-founded a company called Tenable Network Security. For personal use, the product is freely available, but for commercial use, it is not. It costs $1200/year subscription fee for a single scanner. For the latest on their pricing check out their online store .
Nessus’ primary function is to provide security scanning capabilities to its user. Like Nmap, it can do network discovery, but unlike Nmap, it is designed to scan systems to determine their vulnerabilities. Some vulnerability checks, if safe mode is disabled, can crash a system! As such, administrators expose a system to the scans prior to putting them in production.
Because of what Nessus can do, it can be applied in the following ways:
- Security audits
- Asset profiling
- Sensitive data discovery
- Vulnerability analysis
All these can probably done with Nmap, but it would take a lot of work.
Tenable Network Security develops many security check plugins . Between all these plugins, Nessus is able to check for over 12,000 CVEs (Common Vulnerability Exposures) .
Nessus is really a different class of tool compared to Nmap. It is more of an enterprise scanner. Nessus uses a web interface for its user interface, and it allows the Nessus administrator to create multiple users. The one interesting thing about Nessus is the ability to create policies which are composed of scanning specifications–to include what security plugins are to be used, the types of ports to scan, any credentials that may be needed, and so on. A scan can then be created using that policy. It is in scans where targets are specified.
Through the user interface, one can view scan results even as the scan is in progress. Reports are generated invarious formats. This complete approach to vulnerability scanning puts Nessus on a higher level than Nmap.
Conclusion
Depending on your position and purpose, it may already be clear which tool is for you. However, if you main focus is making sure any vulnerabilities are discovered, without the need to hire a network and security expert, then Nessus may just be the answer. It is not free, but it is relatively inexpensive. If you are a penetration security engineer and assigned to check out a company’s network, Nmap may just do the job because of its portability and utility.