Social engineering and passwords are two types of physical access attacks. Understanding about them and knowing some of the defense measures against them will help combat against such attacks. Read on for an insight to how social engineering works as well as how to safeguard passwords.
Network Attacks Explained
“Attackers can be from outside organisations, but they can also be insiders — disgruntled or greedy employees or contractors. When attackers are able to physically access a system, they can wreak a world of havoc.” [1] As well, they “can easily attach a protocol analyzer to the network and then capture traffic.” [2]
Why network attacks continue to rise: Lack of security and network awareness training has lead to weaknesses in physical security. If computer users fail to physically protect their systems, it leaves open up a variety of avenues for attackers to hack a PC or network.
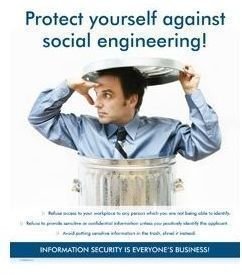
Social Engineering: A Physical Access Attack
One of the most common kinds of social engineering attacks is a physical access attack. Social engineering attacks target physical access to computer systems and networks. It involves interaction with computer users to have them reveal security-relevant information to cause breaches in a network system or perhaps even permit an attack. Since social engineering tries to persuade a victim to be helpful, the attacker will often impersonate the person. Many times, the damage of social engineering is not known by the victim for some time. To combat such an attack, people must first understand social enginnering and then know how-to protect against a social engineering attack .
Once a victim falls to a social engineering attack, the attacker will provide physical access to a computer and possibly a network. The only hold up may be the users’ password and authentication on to a PC or network. This assumes, of course, that no other biometric device (like a finger print scanner) is used. Hint: It may be a good investment in owning one since passwords are known to be easily hacked.
Next explains how a social engineering attack works…
An attacker would start by mounting your drive using a linux live-cd (for instance the security distro Backtrack 3). To gain read write access they would use ntfsmount. Assuming your disk was at /dev/hda1 they would use this command:
ntfsmount /dev/sda1 /mnt/hda1
Passwords on your computer are stored in the form of encrypted hashes. The attacker would use two commands to dump these hashes to their disk.
bkhive /mnt/sda1/WINNT/system32/config/system systemKey.txt
This dumps the computers boot key to ‘systemKey.txt’.
samdump2 /mnt/sda1/system32/config/SAM userHashes.txt
This dumps the password hashes to ‘userHashes.txt’.
The attacker can then crack these password hashes at their leisure on their own machines using tools like Cain and Abel, John the
Ripper or Rainbow Tables. To finish our example using John the Ripper, the attacker would use:
john userHashes.txt
The user then has access to all of the local accounts on the machine. Easy wasn’t it?
Advice: Since a social enginnering attack will raise awareness for victims, any education and user awareness training on social enginnering will be beneficial for them.
Passwords: A Physical Access Attack
Passwords are physical access attacks as well. Since passwords are a common access point into a PC and network, they are vulnerable to attacks by hackers–of whom may be able to access files and other data. A physical access attack caused by broken passwords is not rare these days; in fact, it is a risk each computer user may face, so knowing what can be done about it will likely help prevent a user from being a victim of such an attack.
Passwords provide access to computers and networks. Passwords that are hacked risk having a physical access attack. The best way to prevent such an incident or event is to use hard-to-guess passwords and regularly changing them too to avoid a hacker cracking them and using them to penetrate a system and cause a physical access attack.
One way a computer user may be able to protect his PC and network fom physical access attacks is to invest in biometric devices (such as the one previously mentioned) in addition to or to eliminate the need of using passwords. This, however, is expensive, especially if users want to protect multiple machines.
Another way to prevent physical access attacks is to keep attackers away from computers and networks. This is as simple as locking an office door or room when people leave it.
Advice: All suspicious people or unauthorized workers approaching machines (including employees accessing machines that they don’t regularly use) should be reported.
Tip: Creating a culture of security in your workplace will help you avoid the irrevocable damage that physical access attacks can cause.
References
[1] ZDNet UK, Mike Mullins - Protect your data from physical attack
[2] Tech-FAQ - Network Attacks
Social Engineering: https://www.microsolved.com/2009/Social _Engineering.html
Social Engineering Fundamentals, Part II: Combat Strategies: https://www.crime-research.org/library/Razum2.htm
Image: Terranova - Social Engineering - Awareness Poster